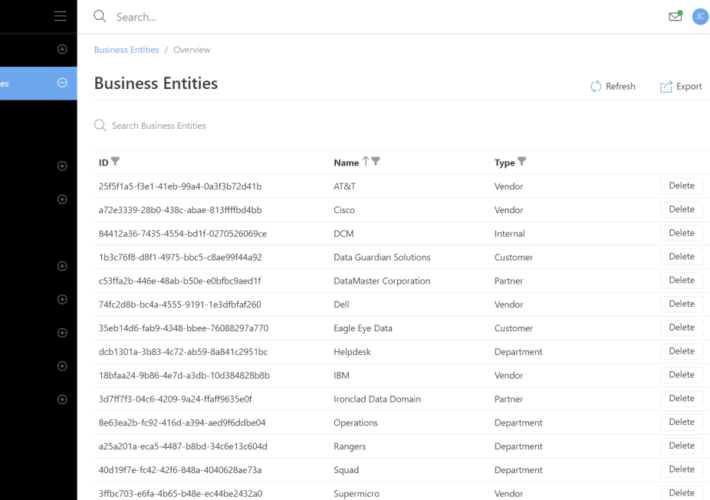
Source: securityboulevard.com - Author: Rajan Sodhi We’ve introduced Business Entities, a game-changer for tracking customers, partners,...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Kevin Murphy May 23, 2024 NTLM (NT LAN Manager) relaying is an...
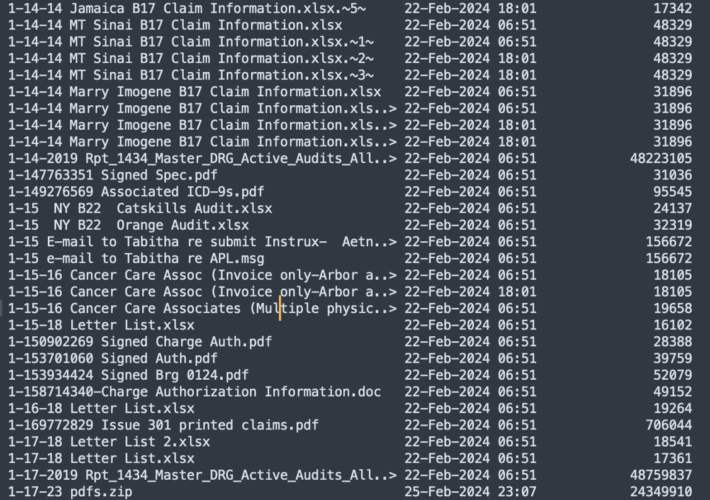
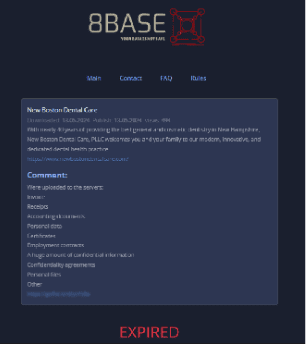
Source: securityboulevard.com - Author: Veriti Research In recent research by Veriti, a significant cyber security breach...
Source: securityboulevard.com - Author: bacohido By Byron V. Acohido AppSec has never been more challenging. By...
Source: securityboulevard.com - Author: Chris Garland Bob Martin comes on the show to discuss systems of...
Source: securityboulevard.com - Author: Tony Bradley The 2024 Proofpoint “Voice of the CISO” report is a...
Source: securityboulevard.com - Author: Nathan Eddy Prompt injection attacks, where individuals input specific instructions to trick...
Source: securityboulevard.com - Author: AJ Starita Responsible AI Licenses (RAIL) are a class of licenses created...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Matt Kelly Talk to any compliance officer today, and they will all...
Source: securityboulevard.com - Author: Richi Jennings Construction giant Arup Group revealed as victim of January theft:...
Source: securityboulevard.com - Author: cybernewswire Torrance, United States / California, May 22nd, 2024, CyberNewsWire AI SPERA,...
Source: securityboulevard.com - Author: Nathan Eddy Lasso Security has released a custom policy wizard designed to...
Source: securityboulevard.com - Author: Ronan Grobler, Compliance Success Manager, Scytale Understanding ISO/IEC 42001 ISO/IEC 42001 provides...
Source: securityboulevard.com - Author: Danielle Guetta While zero-trust policies and identity-centric programs excel at protecting user...
Source: securityboulevard.com - Author: Nathan Eddy Threat actors increasingly are targeting monitored applications with active protection...
Source: securityboulevard.com - Author: Joe Nicastro Understand why securing build systems is as important as securing...
FUD: How Fear, Uncertainty, and Doubt can ruin your security program – Source: securityboulevard.com
Source: securityboulevard.com - Author: Ryan Healey-Ogden The role of fear Fear drives irrational and panicked decision-making,...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Iskander Sanchez-Rola, Leyla Bilge, Davide Balzarotti, Armin Buescher, Petros...
Source: securityboulevard.com - Author: Melissa Goldberger Introduction It’s not a secret that organizations are increasingly investing...
Source: securityboulevard.com - Author: cybernewswire New York, NY, May 21, 2024, CyberNewsWire — Memcyco Inc., provider...
Source: securityboulevard.com - Author: Nathan Eddy Website impersonation scams are on the rise, and many companies...
Source: securityboulevard.com - Author: Leigh Dow Communications hijacking, also known as “conversation hijacking,” has emerged as...
Source: securityboulevard.com - Author: Alberto Casares Healthcare ransomware attacks are one example of cyberattacks for the...
Source: securityboulevard.com - Author: Elliot Volkman Today, while cybersecurity is a highly sought-after field, most of...
Source: securityboulevard.com - Author: TuxCare Team Hospitals worldwide to be offered extended lifecycle support and security...
Source: securityboulevard.com - Author: Cyber Risk Quantification TL;DR Business leaders know that managing risk...
Source: securityboulevard.com - Author: Rohan Timalsina Several vulnerabilities have been discovered in the Linux kernel that...
Source: securityboulevard.com - Author: Nisos Over fifteen million visitors, including 2 million international attendees, are expected...
Source: securityboulevard.com - Author: Blog Archives - Gurucul Harnessing and interpreting data insights for actionable solutions...