Source: securityboulevard.com - Author: Chris Garland NIS2 is an EU cybersecurity directive that covers an incredibly...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters:Ayush Goel and Jingyuan Zhu, University of Michigan; Ravi Netravali,...
Source: securityboulevard.com - Author: Maycie Belmore How CyberWinter Studios Empowers the Warfighter with Automated Readiness Time...
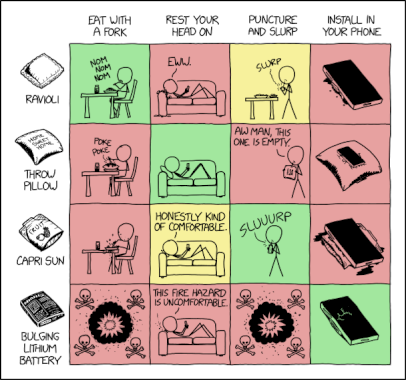
Source: securityboulevard.com - Author: Marc Handelman via the comic humor & dry wit of Randall Munroe,...
Source: securityboulevard.com - Author: Lisa Haas As the vast majority of modern applications rely heavily on...
Source: securityboulevard.com - Author: Vivek Kumar, Sr. Director of Partner Alliances, AppOmni SaaS applications like Salesforce,...
Source: securityboulevard.com - Author: Ontic Article Learn how the right integrations close critical data gaps, helping...
Source: securityboulevard.com - Author: Team Nuspire Generative AI is no doubt the leading frontier in AI....
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters:Abhishek Vijaya Kumar, Bill Owens, Nikolaj Bjørner, Binbin Guan, Yawei...
Source: securityboulevard.com - Author: Jeffrey Burt Congressional lawmakers are pushing for information from three wireless carriers...
Source: securityboulevard.com - Author: Marc Handelman via the inimitable Daniel Stori at Turnoff.US! Permalink *** This...
Source: securityboulevard.com - Author: Michael Vizard A report finds a third (33%) of the cloud security...
Source: securityboulevard.com - Author: Jeffrey Burt Federal investigators created a fictional company and cryptocurrency to ensnare...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters:Arjun Balasingam, Manikanta Kotaru, Paramvir Bahl Our sincere thanks to...
Source: securityboulevard.com - Author: Marc Handelman A Proclamation on Columbus Day, 2024 Today, we celebrate...
Source: securityboulevard.com - Author: Maggie MacAlpine At Seceon’s 2024 Innovation and Certification Days, we had the...
Source: securityboulevard.com - Author: Guest Expert Tiexin Guo OS Developer @Ubuntu CNCF ambassador | LinkedIn As...
Source: securityboulevard.com - Author: Rebecca Kappel When it comes to healthcare data security, HIPAA is the...
Source: securityboulevard.com - Author: Claude Mandy Executive Summary Researchers at the Spark Research Lab (University of...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters:Vaibhav Singh, Tusher Chakraborty, Suraj Jog, Om Chabra, Deepak Vasisht,...
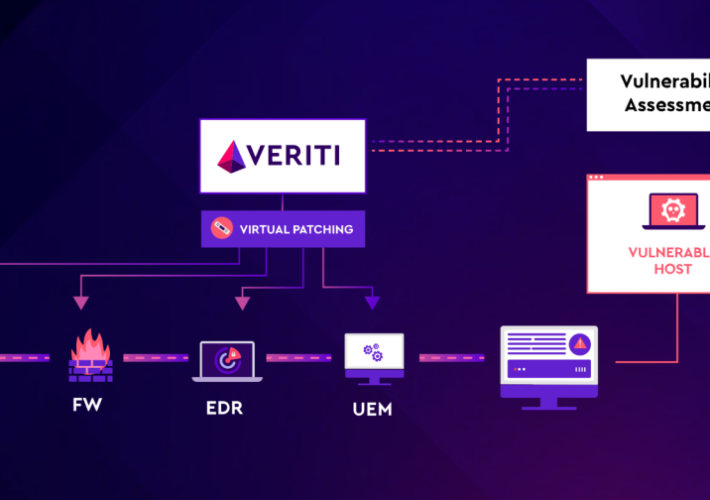
Source: securityboulevard.com - Author: Michael Greenberg One of the biggest dilemmas for security teams is when...
Source: securityboulevard.com - Author: Lohrmann on Cybersecurity Bad actors often take advantage of natural disasters, and...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters:Bill Tao, Om Chabra, Ishani Janveja, Indranil Gupta, Deepak Vasisht...
Source: securityboulevard.com - Author: Ethan Bresnahan In today’s complex cyber landscape, managing risks effectively isn’t just...
Cost of Online Brand Impersonation: Customer Acquisition and Loyalty – Source: securityboulevard.com
Source: securityboulevard.com - Author: Mitch Warren Online brand impersonation is an insidious threat compared to more...
Source: securityboulevard.com - Author: Ryan Healey-Ogden This year’s Cyber Security Awareness Month theme is “Generation Cyber...
Source: securityboulevard.com - Author: Matthew Rosenquist The InCyber Forum Canada 2024 conference is an outstanding event,...
Source: securityboulevard.com - Author: Bruce Schneier In July, I wrote about my new book project on...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters:Lixin Liu, Yuanjie Li, Hewu Li, Jiabo Yang, Wei Liu,...
Source: securityboulevard.com - Author: hmeyers Gary Perkins, Chief Information Security Officer, CISO Global October 11, 2024...