Source: securityboulevard.com - Author: Flare Flare recently hosted our first Threat Intel Workshop with Senior Threat...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Marc Handelman Monday, November 11, 2024 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: cybernewswire TEL AVIV, Israel, November 11th, 2024, CyberNewsWire Customers can now easily...
Source: securityboulevard.com - Author: Marc Handelman With Deep Respect, We Honor Our Canadian Allies, Family And...
Source: securityboulevard.com - Author: Martin Johnson Organizations today face a surge of vulnerabilities and exposures. With...
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author What is Open Source AI?...
Source: securityboulevard.com - Author: David Monnier As we observe Veterans Day in the United States and...
Source: securityboulevard.com - Author: Marc Handelman Monday, November 11, 2024 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Alexa Sander In our latest webinar, we explored real-world cybersecurity and online...
Source: securityboulevard.com - Author: Keon Ramezani Your internet account passwords are probably among the most guarded...
Source: securityboulevard.com - Author: Marc Handelman Sunday, November 10, 2024 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Grip Security Blog CISOs often face high-stake decisions. Imagine this hypothetical scenario:...
Source: securityboulevard.com - Author: Grip Security Blog Integrating ServiceNow and Grip Security delivers a robust solution...
Source: securityboulevard.com - Author: Ziv Gadot ISPs face a few unique challenges and risks when it...
Source: securityboulevard.com - Author: Marc Handelman MARINE CORPS BIRTHDAY CONTENTDate Signed: 10/25/2024MARADMINS Number: 511/24 MARADMINS :...
Source: securityboulevard.com - Author: Avigail Politzer What is the Montana Consumer Data Protection Act (MTCDPA)? The...
Source: securityboulevard.com - Author: Avigail Politzer What is the Tennessee Information Protection Act (TIPA)? The Tennessee...
Source: securityboulevard.com - Author: Avigail Politzer The Delaware Personal Data Privacy Act (DPDPA) is a state...
Source: securityboulevard.com - Author: Marc Handelman Saturday, November 9, 2024 Home » Security Bloggers Network »...
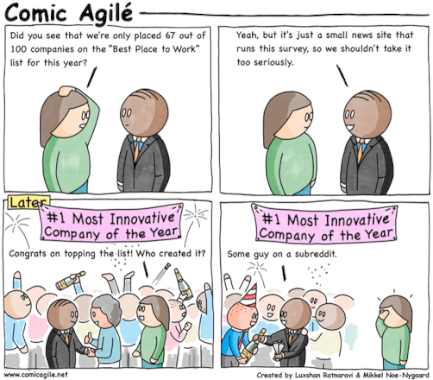
Source: securityboulevard.com - Author: David Ratner As CEO, I couldn’t be more proud of the entire...
Source: securityboulevard.com - Author: Rob Thomas A special message from Rob Thomas, CEO of Team Cymru,...
DEF CON 32 – Securing CCTV Cameras Against Blind Spots – Jacob Shams – Source: securityboulevard.com
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » DEF CON 32 –...
Source: securityboulevard.com - Author: David Irwin Have you ever wondered how to get the most from...
Source: securityboulevard.com - Author: Marc Handelman Friday, November 8, 2024 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » DEF CON 32 –...
Source: securityboulevard.com - Author: Avast Blog Home » Security Bloggers Network » Smart holiday shopping—How to...
Source: securityboulevard.com - Author: Dwayne McDaniel At one point in the not-too-distant past, the most exciting...
Source: securityboulevard.com - Author: Votiro Tool redundancy within organizations presents significant challenges that impede operational efficiency...
Source: securityboulevard.com - Author: Juan Perez CISA is warning about a spear-phishing campaign that spreads malicious...
Source: securityboulevard.com - Author: David Lindner, Director, Application Security Insight #1: Time for a new SIEM?...