Source: securityboulevard.com - Author: Marc Handelman via the respected Software Engineering expertise of Mikkel Noe-Nygaard and the lauded Software Engineering / Enterprise...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Impart Security Blog With Testing Time Control, Impart Security has built an...
Source: securityboulevard.com - Author: Chris Garland Over half of the most routinely exploited vulnerabilities worldwide in...
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog Software teams from...
Source: securityboulevard.com - Author: Glenn Gray For small and mid-size businesses (SMBs), balancing IT and security...
Source: securityboulevard.com - Author: Legit Security As a cloud service provider (CSP), working with federal agencies...
Source: securityboulevard.com - Author: Legit Security With advanced AI cybersecurity tools, you bring powerful capabilities to...
Source: securityboulevard.com - Author: Marc Handelman Thursday, November 21, 2024 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Paul Horn Managing digital certificates might sound simple, but for most organizations,...
Source: securityboulevard.com - Author: Marc Handelman via the inimitable Daniel Stori at Turnoff.US! Permalink *** This...
Source: securityboulevard.com - Author: Richi Jennings Stubborn network device maker digs in heels and tells you...
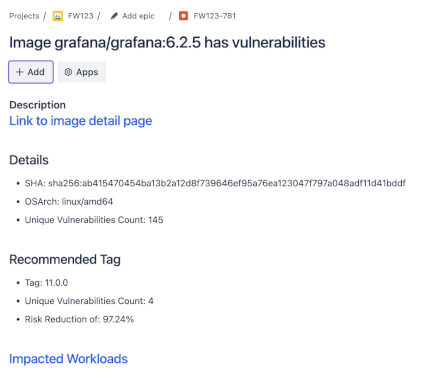
Source: securityboulevard.com - Author: Chris Garland As enterprises increasingly focus on supply chain security, a critical...
Source: securityboulevard.com - Author: Chris Garland In this episode, Paul Asadoorian, Allan Alford, and Josh Corman...
Source: securityboulevard.com - Author: Kolawole Samuel Adebayo The financial cost of a data breach is often...
Source: securityboulevard.com - Author: Brinton Taylor A landmark global report from cybersecurity agencies emphasizes 17 attack...
Source: securityboulevard.com - Author: Pierre Noujeim Isn’t it annoying when multiple alerts are clearly related, but...
Source: securityboulevard.com - Author: Courtney Chatterton Cybersecurity impacts us all. Third parties process and handle data...
Source: securityboulevard.com - Author: Michael Vizard Microsoft this week launched a raft of cybersecurity initiatives that...
Source: securityboulevard.com - Author: Robert Levine Executive Summary: In today’s security landscape, the concept of a...
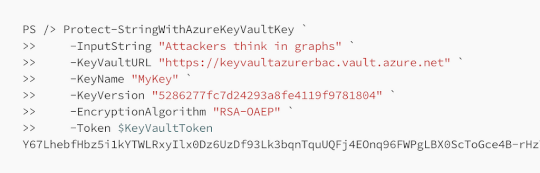
Source: securityboulevard.com - Author: Andy Robbins Brief This post details the existing and new functions in...
Source: securityboulevard.com - Author: Richi Jennings Redmond business leaders line up to say what’s new in...
Source: securityboulevard.com - Author: Dexter Garner Over the last few months, we’ve been working on making...
Source: securityboulevard.com - Author: Nathan Eddy As cybersecurity challenges grow in complexity, chief information security officers...
Source: securityboulevard.com - Author: Jesse Martin What Happened In August 2024, the United States Federal Trade...
Source: securityboulevard.com - Author: Michael Wright The Cybersecurity and Infrastructure Security Agency (CISA) has introduced a...
Source: securityboulevard.com - Author: Jeffrey Burt More than 300 drinking water systems in the United States...
Source: securityboulevard.com - Author: Marc Handelman Tuesday, November 19, 2024 Home » Security Bloggers Network »...
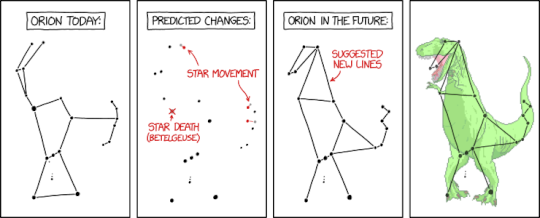
Source: securityboulevard.com - Author: Marc Handelman via the comic humor & dry wit of Randall Munroe,...
Source: securityboulevard.com - Author: Nikolaos Pantazopoulos IntroductionDiscovered in 2021, Raspberry Robin (also known as Roshtyak) is...
Source: securityboulevard.com - Author: Dana Epp In API security, one of the least visible and most...