Source: securityboulevard.com - Author: Amy Cohn Why is the Concept of Least Privilege Vital in Data...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Amy Cohn Are You Optimally Securing Your Non-Human Identities and Their Secrets?...
Source: securityboulevard.com - Author: Katie Bykowski Artificial Intelligence (AI) is rapidly transforming the cybersecurity landscape, offering...
Source: securityboulevard.com - Author: Rajan Sodhi Product Update: Version 4.7 Our latest software release delivers a...
Source: securityboulevard.com - Author: Crystal Derakhshan Ever wondered what VEX really is and why it’s crucial...
Source: securityboulevard.com - Author: Irene Berlinsky You thought your bot problem was firmly under control. After...
Source: securityboulevard.com - Author: Marc Handelman Thursday, December 5, 2024 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: pmiquel Do-It-Yourself Takedown Struggles A credit union based in the southern United...
Source: securityboulevard.com - Author: cybernewswire Alisa Viejo, California, December 5th, 2024, CyberNewsWire One Identity named Hot...
Source: securityboulevard.com - Author: Matt Weir “I have not failed. I’ve just found 10,000 ways that...
Source: securityboulevard.com - Author: Amy Cohn How Does API Security Influence Cybersecurity? As a seasoned data...
Source: securityboulevard.com - Author: Amy Cohn Why Are IAM Strategies Strategic to Data Breach Prevention? IAM...
Source: securityboulevard.com - Author: Jeffrey Burt National Public Data, the data broker that filed for bankruptcy...
Source: securityboulevard.com - Author: Marc Handelman Thursday, December 5, 2024 Home » Security Bloggers Network »...
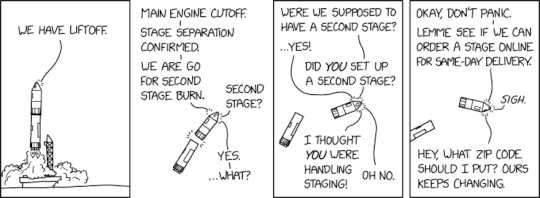
Source: securityboulevard.com - Author: Marc Handelman via the comic humor & dry wit of Randall Munroe,...
Source: securityboulevard.com - Author: Grip Security Blog The SaaS security landscape is shifting faster than ever,...
Source: securityboulevard.com - Author: Richi Jennings FBI and NSA recommend you use strong encryption.Chinese APT actors breached...
Source: securityboulevard.com - Author: Robert Curlee In the 10.8 release of SonarQube Server, you’ll find these...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, December 4, 2024 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: cybernewswire New York, USA, December 3rd, 2024, CyberNewsWire HyperRing, the leader in...
Source: securityboulevard.com - Author: Steve Winterfeld As leaders responsible for cybersecurity programs, we are asked to...
Source: securityboulevard.com - Author: Guy Guzner The democratization of IT fundamentally redefines what it means to...
Source: securityboulevard.com - Author: cybernewswire Tel Aviv, ISRAEL, December 3rd, 2024, CyberNewsWire Sweet Security Introduces Evolutionary...
Source: securityboulevard.com - Author: Rob Witcher As our digital world expands, so does the need for...
Source: securityboulevard.com - Author: Steve Durbin Business leaders continue to view cybersecurity as an expenditure, a...
Source: securityboulevard.com - Author: David Langlands Evidence suggests that a sophisticated group of foreign threat actors...
Source: securityboulevard.com - Author: Jeffrey Burt Interpol and law enforcement agencies from 19 African countries arrested...
Source: securityboulevard.com - Author: Michael Vizard Exabeam has allied with Wiz to gain access to security...
Source: securityboulevard.com - Author: Anupam Upadyaya The web browser has transformed significantly in recent years, becoming...
Source: securityboulevard.com - Author: Mary Henry AWS re:Invent 2024 is next week, right after a late...