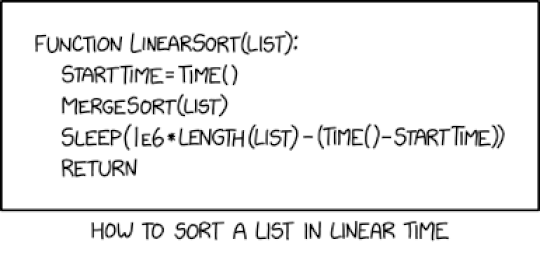
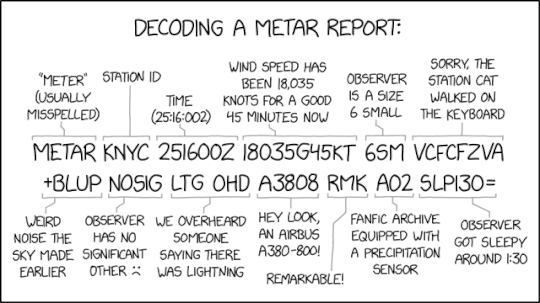
Source: securityboulevard.com - Author: Marc Handelman via the comic humor & dry wit of Randall Munroe,...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Lisa Haas Recently, an Apache Tomcat web server vulnerability, tracked as CVE-2024-50378,...
Source: securityboulevard.com - Author: Chris Garland Recent research has uncovered a concerning vulnerability in modern Trusted...
Source: securityboulevard.com - Author: Bob Palmer Here at ColorTokens, we’ve recently been engaged with a leading...
Source: securityboulevard.com - Author: Amy Cohn Why is Access Control Crucial in Cybersecurity? In the expansive...
Source: securityboulevard.com - Author: Amy Cohn Why is Secure Automation Essential for Cloud Operations? Modern businesses...
Source: securityboulevard.com - Author: Amy Cohn Is Secrets Security Management Crucial for High-Growth Environments? The digital...
Source: securityboulevard.com - Author: Sulagna Saha Since the earliest incidents of computer break-ins, experts have maintained...
Source: securityboulevard.com - Author: Santiago Rodriguez In an increasingly complex threat landscape, sophisticated mobile-targeted phishing campaigns...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, December 18, 2024 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Pushpendra Mishra In today’s ever-evolving digital landscape, businesses face increasingly sophisticated cyber...
Source: securityboulevard.com - Author: Omair Dawood, Principal Product Marketing Manager, Contrast Security As a Contrast Security...
Source: securityboulevard.com - Author: Jason Wagner The recent incident involving the United Healthcare CEO has sparked...
Source: securityboulevard.com - Author: Votiro The holiday shopping season is a time of excitement and anticipation...
Source: securityboulevard.com - Author: Rebecca Crum Business-critical SaaS applications are prime targets for cyberattacks due to...
Source: securityboulevard.com - Author: Rebecca Crum In today’s digital landscape, organizations rely on SaaS applications for...
DEF CON 32 – HookChain A New Perspective For Bypassing EDR Solutions – Source: securityboulevard.com
Source: securityboulevard.com - Author: Marc Handelman Wednesday, December 18, 2024 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Dave Ferguson Many software development shops deliver their product releases via virtual...
Source: securityboulevard.com - Author: Marc Handelman Permalink *** This is a Security Bloggers Network syndicated blog...
Source: securityboulevard.com - Author: mykola myroniuk Picture this scenario: You’ve used every tool you have to...
Source: securityboulevard.com - Author: Enzoic Updates from Enzoic’s Threat Research Team As the year’s end approaches,...
Balbix is recognized in Forrester’s CRQ Solutions Landscape, Q4 2024 – Source: securityboulevard.com
Source: securityboulevard.com - Author: Gaurav Banga Last week, Balbix was recognized in the Forrester Cyber Risk...
Source: securityboulevard.com - Author: Marc Handelman Tuesday, December 17, 2024 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Avast Blog Home » Security Bloggers Network » 10 telltale signs of...
Source: securityboulevard.com - Author: Scott Fiesel With less than four months until the compliance deadline for...
Source: securityboulevard.com - Author: Amy Cohn Why is Secrets Rotation Integral to Your Cybersecurity Strategy? In...
Source: securityboulevard.com - Author: Amy Cohn Can Robust Privileged Access Management (PAM) Secure our Digital Environment?...
Source: securityboulevard.com - Author: Amy Cohn Are You Ready to Manage Secrets Sprawl Effectively? One particular...
Source: securityboulevard.com - Author: Amy Cohn Are We Overlooking Machine Identity Management in Cloud Security? As...
Source: securityboulevard.com - Author: Andy Suderman In the constantly maturing landscape of cloud-native technologies, Kubernetes reigns...