Source: securityboulevard.com - Author: Stevie Caldwell Keeping up to date with critical vulnerabilities related to Kubernetes...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author Remember the days when getting...
Source: securityboulevard.com - Author: Satyam Tyagi Peter Shor revolutionized public-key infrastructure (PKI) using concepts that trace...
Source: securityboulevard.com - Author: Jeffrey Burt A telehealth platform company used by health care firms to...
Source: securityboulevard.com - Author: service Understanding Cyber Threats During the Holiday Season Understanding Cyber Threats During...
Source: securityboulevard.com - Author: Marc Handelman Sunday, December 22, 2024 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Marc Handelman Saturday, December 21, 2024 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: mykola myroniuk If you are a security, compliance, and privacy professional, it’s...
Source: securityboulevard.com - Author: Tony Bradley In today’s interconnected world, the integrity of software has never...
Source: securityboulevard.com - Author: Amy Cohn Understanding the Significance of Non-Human Identities “How secure are your...
Source: securityboulevard.com - Author: Amy Cohn Why Does Secrets Rotation Matter in Today’s Cyberspace? In the...
Source: securityboulevard.com - Author: Amy Cohn Every organization aims to meet its ever-evolving cybersecurity needs. Is...
Source: securityboulevard.com - Author: Amy Cohn How High is Your Trust in Cloud Security? In the...
Source: securityboulevard.com - Author: Amy Cohn Are You Prepared for the Rising Trends in API Security...
Source: securityboulevard.com - Author: Tony Bradley As artificial intelligence evolves, its impact on cybersecurity and the...
Source: securityboulevard.com - Author: Marc Handelman Friday, December 20, 2024 Home » Security Bloggers Network »...
Will AI Drive Efficiency and Budget Growth? Risks, Rewards & Reality – Source: securityboulevard.com
Source: securityboulevard.com - Author: Maycie Belmore The adoption of artificial intelligence (AI) in cybersecurity continues to...
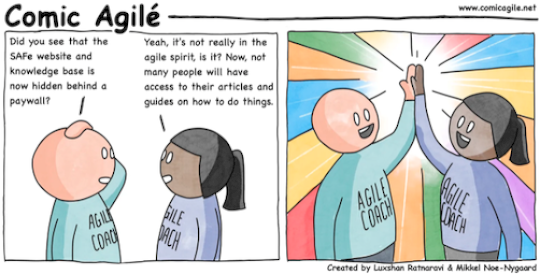
Comic Agilé – Mikkel Noe-Nygaard, Luxshan Ratnaravi – #317 – Paywall – Source: securityboulevard.com
Source: securityboulevard.com - Author: Marc Handelman via the respected Software Engineering expertise of Mikkel Noe-Nygaard and the lauded Software Engineering / Enterprise...
Source: securityboulevard.com - Author: Contrast Marketing Three years ago, Log4Shell was the worst holiday gift ever...
Source: securityboulevard.com - Author: Kevin Gosschalk As a cybersecurity executive, your job is clear: protect business...
Source: securityboulevard.com - Author: pmiquel Diamond Bank is a community bank with 14 branches and thousands...
Source: securityboulevard.com - Author: Marc Handelman Friday, December 20, 2024 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Impart Security Blog Today, we are thrilled to announce that Impart is...
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author Security Assertion Markup Language (SAML)...
Source: securityboulevard.com - Author: Paul Horn As organizations recognize the immense value and criticality of your...
Source: securityboulevard.com - Author: Marc Handelman Thursday, December 19, 2024 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: hmeyers December 19, 2024 The holiday season brings out the best in...
Source: securityboulevard.com - Author: Legit Security Privilege escalation is a critical cybersecurity threat in which a...
Source: securityboulevard.com - Author: Legit Security As software development accelerates, the need to identify threats and...
Source: securityboulevard.com - Author: Legit Security Kubernetes, also known as K8s, is a powerful platform for...