Source: securityboulevard.com - Author: karthik As organizations continue to shift toward digital-first operations, the demand for...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Rebecca Kappel What is a SIEM? SIEM solutions enable enterprises to monitor...
Source: securityboulevard.com - Author: Tim Bach, SVP of Security Engineering, AppOmni The Cybersecurity and Infrastructure Security...
Source: securityboulevard.com - Author: Sunil Muralidhar As we close out 2024, we look back on what...
Source: securityboulevard.com - Author: Assura Team As organizations increasingly rely on digital infrastructure, the stakes have...
Source: securityboulevard.com - Author: Rebecca Kappel In today’s dynamic cybersecurity landscape, organizations face an ever-evolving threat...
Source: securityboulevard.com - Author: Security Insights Team CVSS base scores and temporal scores are not the...
Source: securityboulevard.com - Author: NSFOCUS Overview Recently, NSFOCUS CERT detected that Adobe issued a security announcement...
Source: securityboulevard.com - Author: Amy Cohn Why is Integrating IAM Crucial for Your Security Policies? As...
Source: securityboulevard.com - Author: Amy Cohn How Effective is Your Modern Secrets Management Strategy? Have you...
Source: securityboulevard.com - Author: Amy Cohn What Does Securing Your Cloud-Native Solutions Mean? Cloud-native solutions are...
Source: securityboulevard.com - Author: Amy Cohn Does the thought of data breaches keep you up at...
Source: securityboulevard.com - Author: Marc Handelman NASA Astronaut Jessica Meir’s Hanukkah Wishes from the International Space...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: mykola myroniuk In our last post, we discussed the powerful, yet potentially...
Source: securityboulevard.com - Author: Yunes Tarada Reading Time: 7 min Attention users! Gmail has officially started...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » DEF CON 32 –...
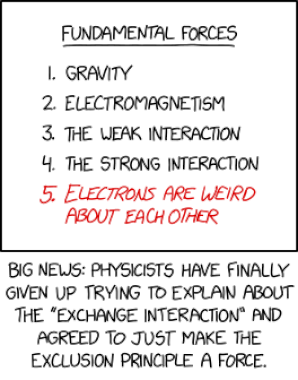
Source: securityboulevard.com - Author: Marc Handelman via the comic humor & dry wit of Randall Munroe,...
Source: securityboulevard.com - Author: Marc Handelman Tuesday, December 24, 2024 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Mike Larkin Yesterday’s discovery of the xz backdoor was an accident. But...
Source: securityboulevard.com - Author: Ahona Rudra As we close out 2024, PowerDMARC stands stronger than ever....
Source: securityboulevard.com - Author: Yunes Tarada DNS vulnerabilities are often overlooked in cybersecurity strategies, despite DNS...
Source: securityboulevard.com - Author: Alison Furneaux Many industry regulations require or promote cybersecurity risk assessments to...
Source: securityboulevard.com - Author: Puja Saikia Vulnerability-based attacks are growing. Undoubtedly, these attacks are hackers’ favorite...
Source: securityboulevard.com - Author: Assura Team As the year comes to a close, State, Local, and...
Source: securityboulevard.com - Author: Amy Cohn Is the Quest for Stability an Uphill Battle in Cybersecurity?...
Source: securityboulevard.com - Author: Marc Handelman Monday, December 23, 2024 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: mykola myroniuk Hey everyone, let’s talk about something we all encounter every...
Source: securityboulevard.com - Author: Marc Handelman Permalink *** This is a Security Bloggers Network syndicated blog...
Source: securityboulevard.com - Author: Marc Handelman Our sincere appreciation to DEF CON, and the Authors/Presenters for...