Source: securityboulevard.com - Author: George V. Hulme While AI/ML and automation promise to help streamline and...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Deepen Desai As we step into 2025, the cyberthreat landscape is once...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » DEF CON 32 –...
Source: securityboulevard.com - Author: Paul Gerste With more and more code generated by humans and AI,...
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author Imagine you run a growing...
Source: securityboulevard.com - Author: Guy Bejerano Author: Guy Bejerano, CEO & Co-Founder, SafeBreach Happy new year!...
Source: securityboulevard.com - Author: Mariusz Michalowski Configuration drift occurs when systems deviate from their intended settings...
Source: securityboulevard.com - Author: Victor Ronin I struggled to find widely adopted terminology to describe this....
Source: securityboulevard.com - Author: Marc Handelman Wednesday, January 8, 2025 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Jeffrey Burt As the Green Bay Packers gear up for their first-round...
Source: securityboulevard.com - Author: Satnam Narang Ivanti disclosed two vulnerabilities in its Connect Secure, Policy Secure...
Source: securityboulevard.com - Author: Richi Jennings Running an obsolete OS, on obsolete hardware, configured with obsolete settings.A...
Source: securityboulevard.com - Author: Enzoic A New Chapter for Immediate, Cross-Organizational Security In today’s hyper-connected society, personal accounts...
Source: securityboulevard.com - Author: Marc Handelman via the comic humor & dry wit of Randall Munroe,...
Source: securityboulevard.com - Author: Avast Blog Home » Security Bloggers Network » Time for a new...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, January 8, 2025 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Daniel Churches I recently caught up with Karissa Breen, the founder of...
Source: securityboulevard.com - Author: psilva The numbers are staggering—2024 has seen over 200,000 layoffs across 1,200...
Source: securityboulevard.com - Author: psilva After being let go from F5 in May 2023, I started...
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author Imagine waking up one morning...
Source: securityboulevard.com - Author: Amy Cohn Are Organizations Fully Grasping the Importance of API Security? It...
Source: securityboulevard.com - Author: Amy Cohn Why Is Identity Access Management (IAM) Crucial in Cloud Security?...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » DEF CON 32 –...
Source: securityboulevard.com - Author: Todd R. Weiss In the world of cybersecurity, compliance is a no-brainer....
Source: securityboulevard.com - Author: Marc Handelman Tuesday, January 7, 2025 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Michael Vizard Exabeam today added a bevy of capabilities to its New-Scale...
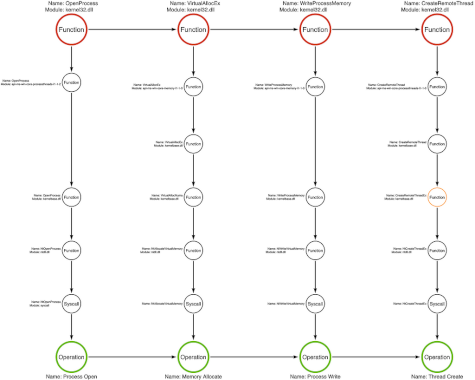
Source: securityboulevard.com - Author: Jared Atkinson On Detection: Tactical to Functional Seven Ways to View API...
Source: securityboulevard.com - Author: Impart Security Blog What happens when cutting-edge technology meets the reality of...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » DEF CON 32 –...
Source: securityboulevard.com - Author: Scott Fiesel by Source Defense In a recent high-profile incident covered by...