Source: securityboulevard.com - Author: Jeffrey Burt A factor in bad actors using AI for their nefarious...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Stephen Kowski Have you ever had your lunch interrupted by a sudden...
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog At Tonic.ai, unlocking...
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog Our test data...
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog The Google Cloud...
How to create de-identified embeddings with Tonic Textual & Pinecone – Source: securityboulevard.com
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog Maintaining data privacy...
Source: securityboulevard.com - Author: Sebastian Wallin Open Bullet 2 is an open-source software, specialized in credential...
Source: securityboulevard.com - Author: FireMon Managing network configurations and changes is a critical component of modern...
Source: securityboulevard.com - Author: David Harley I’ve never been a regular resident of the ivory halls...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » DEF CON 32 –...
Source: securityboulevard.com - Author: Harman Singh PCI DSS refers to the Payment Card Industry Data Security...
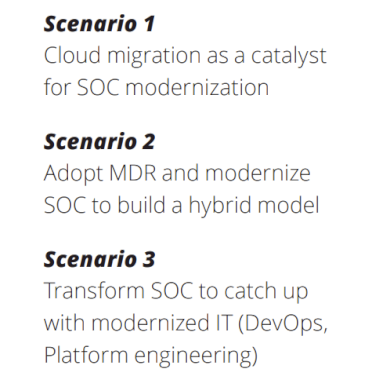
Source: securityboulevard.com - Author: Harman Singh In a time when cyber threats continuously evolve, a security...
Source: securityboulevard.com - Author: Amy Cohn The Strategic Importance of Non-Human Identities Are we taking the...
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author In previous article, "The Hidden...
Source: securityboulevard.com - Author: Marc Handelman Saturday, January 11, 2025 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Chris Garland What Type of Attacks Will We See in 2025? January...
Source: securityboulevard.com - Author: Kriti Tripathi At the recent Build IT 2024 event, our partner Sumeet...
Source: securityboulevard.com - Author: Grip Security Blog Every year, we collectively look for ways to define...
Source: securityboulevard.com - Author: Amy Cohn How Crucial Are Non-Human Identities to Data Security? Data security...
Source: securityboulevard.com - Author: Grip Security Blog In case you missed it, PowerSchool, a leading provider...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » DEF CON 32 –...
Source: securityboulevard.com - Author: Chris Garland The Year of the Typhoon Highlights from this edition: The...
Source: securityboulevard.com - Author: Anton Chuvakin After a long, long, long writing effort … eh … break, we...
Source: securityboulevard.com - Author: Marc Handelman Friday, January 10, 2025 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Jeffrey Burt The personal information of some students and teachers in school...
Source: securityboulevard.com - Author: Aaron Linskens As software supply chains grow more complex, organizations face increasing...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » DEF CON 32 –...
Chinese-linked Hackers May Be Exploiting Latest Ivanti Vulnerability – Source: securityboulevard.com
Source: securityboulevard.com - Author: Jeffrey Burt Management software maker Ivanti continues to struggle with security flaws...
Source: securityboulevard.com - Author: Marc Handelman Thursday, January 9, 2025 Home » Security Bloggers Network »...
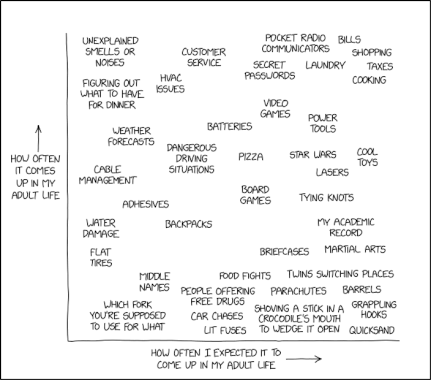
Source: securityboulevard.com - Author: Marc Handelman via the comic humor & dry wit of Randall Munroe,...