Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog Guest post: the following...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
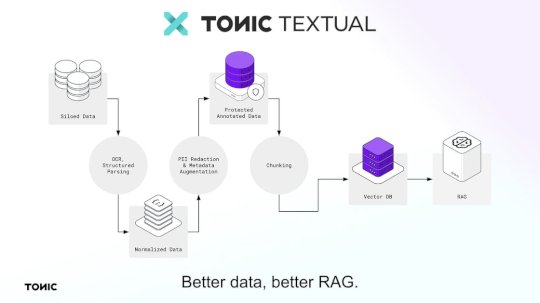
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog We’re excited to...
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog We’re excited to...
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog We’re excited to...
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog We’re excited to...
Source: securityboulevard.com - Author: Marc Handelman Thursday, January 16, 2025 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Dancho Danchev Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Dancho Danchev Dear blog readers, This is Dancho. How to use this...
Source: securityboulevard.com - Author: Maycie Belmore Equipping your security operations center (SOC) team with the right...
Source: securityboulevard.com - Author: cybernewswire Silver Spring, MD, Jan. 15, 2025, CyberNewswire — Aembit, the non-human...
Source: securityboulevard.com - Author: cybernewswire Tel Aviv, Israel, Jan. 15, 2025, CyberNewswire — Sweet Security, a...
Source: securityboulevard.com - Author: cybernewswire Prague, Czech Republic, Jan. 15, 2025, CyberNewswire — Quantum computing is...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, January 15, 2025 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Jeffrey Burt The FBI, with the help of French law enforcement and...
Protecting the software supply chain: Insights from our expert panel – Source: securityboulevard.com
Source: securityboulevard.com - Author: Aaron Linskens As software grows increasingly complex, ensuring the security of your...
Source: securityboulevard.com - Author: Marc Handelman via the comic humor & dry wit of Randall Munroe,...
Source: securityboulevard.com - Author: Richi Jennings “We will hold all these companies accountable,” rants state attorney...
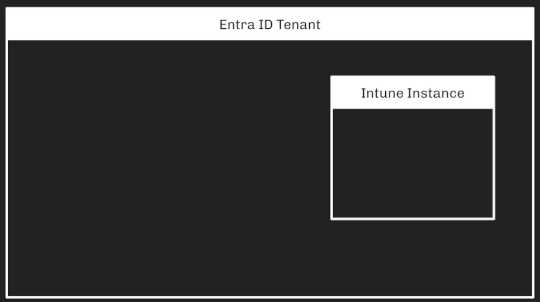
Source: securityboulevard.com - Author: Andy Robbins Intune Attack Paths — Part 1 Prior Work Several people have recently produced...
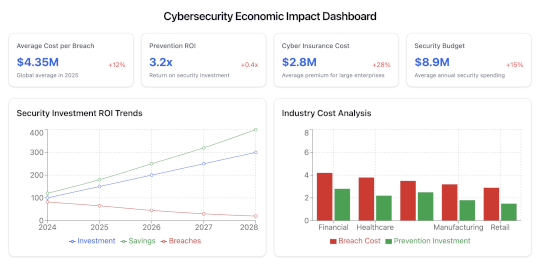
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author The cybersecurity landscape is entering...
Source: securityboulevard.com - Author: Digital Defense by Fortra CVE/Advisory Title Tag Microsoft Severity Rating Base Score...
Source: securityboulevard.com - Author: Contrast Marketing Attacks on individual applications were down month to month in...
Source: securityboulevard.com - Author: Amanda Alvarez Find out why unknown build assets is a growing problem...
Source: securityboulevard.com - Author: Scott Caveza Fortinet patched a zero day authentication bypass vulnerability in FortiOS...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, January 15, 2025 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Tenable Security Response Team 10Critical 147Important 0Moderate 0Low Microsoft addresses 157 CVEs...
Source: securityboulevard.com - Author: Team Nuspire As we stand on the threshold of 2025, the cybersecurity...
Source: securityboulevard.com - Author: Marc Handelman via the comic humor & dry wit of Randall Munroe,...
Source: securityboulevard.com - Author: Votiro Data is in perpetual motion within organizations, continuously crossing various networks...
Source: securityboulevard.com - Author: Kevin Sapp Managing identities is no longer limited to employees logging into...
Source: securityboulevard.com - Author: George V. Hulme The U.S. Department of Health and Human Services (HHS)...