Source: securityboulevard.com - Author: Dwayne McDaniel When President Biden signed Executive Order 14028 on Improving the...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author The Bluesky AT Protocol is...
Source: securityboulevard.com - Author: Avoid The Hack! This is a news item roundup of privacy or...
Source: securityboulevard.com - Author: Bruce Schneier President Biden has signed a new cybersecurity order. It has...
Source: securityboulevard.com - Author: Priyadarshi Prasad “God seems to know not only what we do but...
Source: securityboulevard.com - Author: Artyom Buchkov In the rapidly evolving iGaming industry, platforms such as online...
Source: securityboulevard.com - Author: Deborah Erlanger What is the Information Security Manual (ISM)? The Information Security...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » DEF CON 32 –...
Source: securityboulevard.com - Author: psilva Adam Ant, AD Rock, Alan Parsons, Aldo Nova, Alex Lifeson, Andrew...
Source: securityboulevard.com - Author: Amy Cohn Are Businesses Truly Prepared for Today’s Cybersecurity Challenges? With the...
Source: securityboulevard.com - Author: Amy Cohn What Role Does Proactive Handling of Cloud Identities Play in...
Source: securityboulevard.com - Author: Amy Cohn Is Your PAM Strategy as Secure as You Think? It’s...
Source: securityboulevard.com - Author: Marc Handelman Saturday, January 18, 2025 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Harman Singh What is Cyber Essentials? Cyber Essentials scheme is a UK...
Source: securityboulevard.com - Author: Veriti Research As the political landscape heats up, so does the activity...
Source: securityboulevard.com - Author: Grainne McKeever The ticketing industry is under constant threat from malicious bots,...
Source: securityboulevard.com - Author: Anton Chuvakin image by Meta.AI lampooning humanless SOC My former “colleagues” have...
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog Safeguarding sensitive information...
Source: securityboulevard.com - Author: Kevin Mata Generative AI is reshaping cybersecurity by providing advanced threat detection,...
Source: securityboulevard.com - Author: bacohido By Jonathan Gill President Biden’s detailed executive order relating to cybersecurity...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » DEF...
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author Grok AI continues to evolve...
Source: securityboulevard.com - Author: hmeyers January 17, 2025 Gary Perkins, CISO at CISO Global Cybersecurity may...
Source: securityboulevard.com - Author: Jeffrey Burt President Biden’s last-minute, expansive cybersecurity executive order, which touches everything...
Source: securityboulevard.com - Author: Richi Jennings Joseph Robinette Biden Jr. (pictured) hits the emergency “do something” button.Yesterday’s Biden...
Source: securityboulevard.com - Author: Andrew Hendry The March 2025 PCI DSS 4.0 compliance deadline is just...
Source: securityboulevard.com - Author: Marc Handelman Friday, January 17, 2025 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Michael Vizard Cohesity has extended its Cyber Event Response Team (CERT) service...
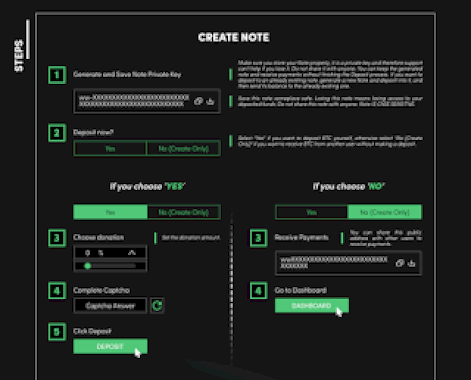
Source: securityboulevard.com - Author: Dancho Danchev Dear blog readers, In this post I’ll provide some actionable...
Source: securityboulevard.com - Author: Dancho Danchev Dear blog readers, In this post I’ll provide some actionable...