Source: securityboulevard.com - Author: Amy Cohn Why is Secrets Rotation Crucial for Cloud Security? Are you...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Amy Cohn Are You Confident in Your Cloud-Native Security? Navigating cybersecurity can...
Source: securityboulevard.com - Author: Amy Cohn Is Your Organization Paying Enough Attention to Non-Human Identities? Organizations...
Source: securityboulevard.com - Author: Andrew Hendry Imagine your website humming with activity, traffic soaring, and your...
Source: securityboulevard.com - Author: Manish Mehta Article Your IT department can be a valuable ally in...
Source: securityboulevard.com - Author: Kirsten Gibson TL;DR Insurance companies host large amounts of sensitive data (PII,...
Source: securityboulevard.com - Author: Marc Handelman Thursday, January 23, 2025 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Rebecca Kappel One of the most pivotal decisions an organization faces is...
Source: securityboulevard.com - Author: John Bowers The UK National Cyber Security Centre (NCSC), the country’s technical...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, January 22, 2025 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Maycie Belmore Welcome to the “Life in the Swimlane” blog series. Here...
Source: securityboulevard.com - Author: Anton Chuvakin This is my completely informal, uncertified, unreviewed and otherwise completely...
Source: securityboulevard.com - Author: Marc Handelman via the comic humor & dry wit of Randall Munroe,...
Filtered to Perfection: Votiro’s Two-Layer Approach to Cybersecurity – Source: securityboulevard.com
Source: securityboulevard.com - Author: Votiro The Coffee-Making Process Meets Cybersecurity It’s early morning and you’re gearing...
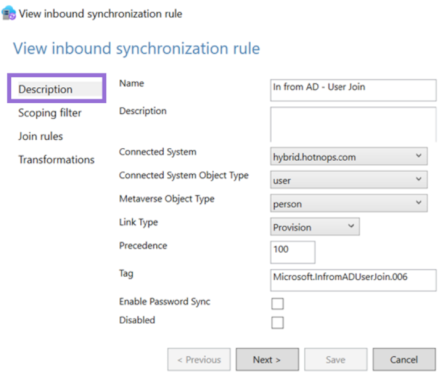
Source: securityboulevard.com - Author: hotnops Now that we know how to add credentials to an on-premises...
Source: securityboulevard.com - Author: Enzoic A Candid Conversation with Enzoic’s CTO The digital landscape is evolving,...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, January 22, 2025 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Dwayne McDaniel If developers all share one thing in common, it is...
Source: securityboulevard.com - Author: Legit Security The European Union (EU)’s General Data Protection Regulation (GDPR) isn’t...
Source: securityboulevard.com - Author: Legit Security AI code generation is changing how developers approach their work....
Source: securityboulevard.com - Author: Legit Security Every time a customer swipes their credit card, they trust...
Source: securityboulevard.com - Author: Legit Security The rule of least privilege, also known as the principle...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, January 22, 2025 Home » Security Bloggers Network »...
Start the year by protecting your privacy— A stalkerware quick check – Source: securityboulevard.com
Source: securityboulevard.com - Author: Avast Blog Home » Security Bloggers Network » Start the year by...
Source: securityboulevard.com - Author: Richi Jennings The Protecting Americans from Foreign Adversary Controlled Applications Act shouldn’t...
Source: securityboulevard.com - Author: Tanuj Mitra Cyber breaches in healthcare are chronic conditions that can linger...
Source: securityboulevard.com - Author: Marc Handelman Tuesday, January 21, 2025 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Jeffrey Burt The U.S. Treasury Department has sanctioned a Chinese national for...
Source: securityboulevard.com - Author: Grip Security Blog Remember when we used ChatGPT to create cybersecurity haiku,...
Source: securityboulevard.com - Author: George McGregor All the key players in cyber-security make predictions at the...









![How to Handle Secrets at the Command Line [cheat sheet included] – Source: securityboulevard.com](https://ciso2ciso.com/wp-content/uploads/2025/01/156035-how-to-handle-secrets-at-the-command-line-cheat-sheet-included-source-securityboulevard-com.jpg)















