Source: securityboulevard.com - Author: Marc Handelman via the respected Software Engineering expertise of Mikkel Noe-Nygaard and the lauded Software Engineering / Enterprise...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Legit Security Cybersecurity compliance goes beyond just meeting regulations. The point of...
Source: securityboulevard.com - Author: Legit Security Imagine a thief silently slipping into your home and copying...
Source: securityboulevard.com - Author: Amy Cohn Is Your Cloud Environment Truly Secure and Free? Have you...
Source: securityboulevard.com - Author: Amy Cohn Why is IAM Crucial in Delivering Value to Modern Businesses?...
Source: securityboulevard.com - Author: Amy Cohn The Benefits of Harnessing Advanced Secrets Rotation How can companies...
Source: securityboulevard.com - Author: Nathan Eddy Security researchers have uncovered serious vulnerabilities in DeepSeek-R1, the controversial...
Source: securityboulevard.com - Author: Alexa Sander This article was originally published in EdTech Magazine on 02/03/25...
Source: securityboulevard.com - Author: Andy Suderman Many organizations used VMware Tanzu when they were seeking to...
Source: securityboulevard.com - Author: Ax Sharma A counterfeit ‘Truffle for VS Code’ extension, published on the...
Source: securityboulevard.com - Author: Lauren Yacono Before exploring how to mitigate the human factors in cybersecurity,...
Source: securityboulevard.com - Author: Cody Thomas A new Mythic add-on for Windows Agents Mythic provides flexibility to...
Source: securityboulevard.com - Author: Trail of Bits By Kelly Kaoudis and Evan Sultanik This blog post...
Source: securityboulevard.com - Author: David Holmes The Age of AI Is Upon Us The current pace...
Secure by Design and Secure by Default: Why you need both for AppSec – Source: securityboulevard.com
Source: securityboulevard.com - Author: John P. Mello Jr. The relationship between the two software security initiatives...
Source: securityboulevard.com - Author: Marc Handelman Tuesday, February 4, 2025 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Grip Security Blog The Cyberhaven breach is more than just an isolated...
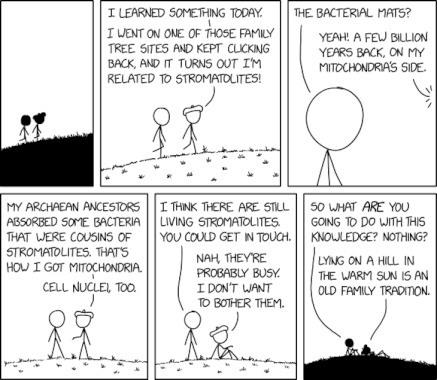
Source: securityboulevard.com - Author: Marc Handelman via the comic humor & dry wit of Randall Munroe,...
Source: securityboulevard.com - Author: Michael Vizard A survey of 150 security decision makers in the U.S.,...
Source: securityboulevard.com - Author: Evan Powell Mitre Att&ck as Context Introduction: A common theme of science fiction...
Source: securityboulevard.com - Author: George V. Hulme This week, AttackIQ acquired DeepSurface to broaden its vulnerability...
Source: securityboulevard.com - Author: Sebastian Wallin The latest wave of artificial intelligence (AI) improvements significantly improved...
Source: securityboulevard.com - Author: Cynthia Marble Article How to strengthen your executive protection program to address...
Source: securityboulevard.com - Author: Jeffrey Burt A 22-year-old Canadian man is accused of stealing almost $65...
Source: securityboulevard.com - Author: Michael Vizard Orca Security has extended the reach of its agentless cloud...
Source: securityboulevard.com - Author: mykola myroniuk In this article Are you an SAQ A merchant figuring...
Source: securityboulevard.com - Author: Impart Security Blog One of the most complex aspects of running a...
Source: securityboulevard.com - Author: Richi Jennings Stop using this healthcare equipment, say Cybersecurity & Infrastructure Security...
Source: securityboulevard.com - Author: Marc Handelman via the comic humor & dry wit of Randall Munroe,...
Source: securityboulevard.com - Author: FireMon The Health Insurance Portability and Accountability Act (HIPAA) mandates a stringent...