Source: securityboulevard.com - Author: Mike Polatsek The Growing Need for Cybersecurity Awareness Training (SAT) In today’s...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Avoid The Hack! This is a news item roundup of privacy or...
Source: securityboulevard.com - Author: Rebecca Kappel Policy management is the sturdy scaffolding that supports governance, risk,...
Source: securityboulevard.com - Author: Maahnoor Siddiqui Cybersecurity and risk management are often treated as separate disciplines...
Source: securityboulevard.com - Author: Cyber Risk Quantification Measuring the Effectiveness of Cyber Security GRC TL;DR...
Source: securityboulevard.com - Author: John D. Boyle In competitive rowing, particularly in an eight with a...
Source: securityboulevard.com - Author: mykola myroniuk In this article 1. Introduction As an SAQ A-EP merchant,...
Source: securityboulevard.com - Author: Amy Cohn Why is Cloud Data Safety a Paramount Concern? With the...
Source: securityboulevard.com - Author: David Harley Over a decade ago, I was more than a little...
Source: securityboulevard.com - Author: Marc Handelman Saturday, February 15, 2025 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: John D. Boyle Generative AI continues its promises of revolutionizing industries and...
Source: securityboulevard.com - Author: Jon Clay If you are on social media, you’ve almost certainly received...
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author Today (February 14, 2025), the...
Source: securityboulevard.com - Author: Amy Cohn Why is Independent Control Over Cloud Data Necessary? Can organizations...
Source: securityboulevard.com - Author: Amy Cohn Is Adaptable Security the Future of Cybersecurity in Dynamic Cloud...
Source: securityboulevard.com - Author: Michael Vizard Delinea this week updated its platform for managing identities to...
Source: securityboulevard.com - Author: Max Aulakh When it comes to overall productivity platforms, collaboration tools, and...
Source: securityboulevard.com - Author: Marc Handelman Friday, February 14, 2025 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Jeffrey Burt A ransomware attack last fall on an unnamed software and...
Source: securityboulevard.com - Author: Richi Jennings Sen. Ron Wyden (D-Ore.) and Rep. Andy Biggs (R-Ariz.) got...
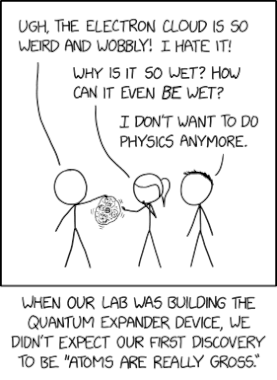
Source: securityboulevard.com - Author: Marc Handelman via the comic humor & dry wit of Randall Munroe,...
Source: securityboulevard.com - Author: Marc Handelman Friday, February 14, 2025 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Team Nuspire In the rapidly evolving landscape of cybersecurity, transformation isn’t just...
Source: securityboulevard.com - Author: Team Nuspire When you’re resilient to something, you don’t just endure; you...
Source: securityboulevard.com - Author: Marc Handelman Thursday, February 13, 2025 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Rajan Sodhi As data centers continue to serve as the backbone of...
Source: securityboulevard.com - Author: Aaron Linskens Artificial intelligence (AI) continues to revolutionize how businesses operate, with...
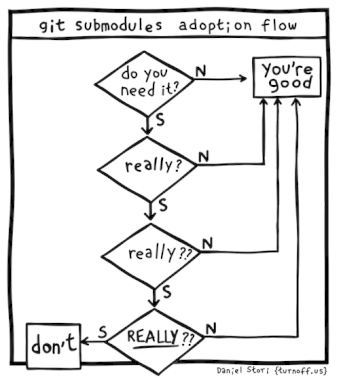
Source: securityboulevard.com - Author: Marc Handelman via the inimitable Daniel Stori at Turnoff.US! Permalink *** This...
Source: securityboulevard.com - Author: Michael Vizard Grip Security today extended its portfolio of tools for securing...
Source: securityboulevard.com - Author: John P. Mello Jr. Cybersecurity is often viewed from the point of...