Source: securityboulevard.com - Author: John Gallagher The Internet of Things (IoT), also referred to as Cyber-Physical...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Promo » Cybersecurity » BSides...
Source: securityboulevard.com - Author: Max Aulakh Government cybersecurity and information security frameworks are a constant work...
Source: securityboulevard.com - Author: FireMon On February 24, 2025, Skybox Security officially shut down operations, leaving...
Source: securityboulevard.com - Author: Jeffrey Burt AI agents are the latest rage in the fast-moving AI...
Source: securityboulevard.com - Author: Krupa Patil Google’s second-generation Chromecast and Chromecast Audio devices have been facing...
Source: securityboulevard.com - Author: Amy Cohn Could API Automation Be The Missing Piece In Your NHI...
Source: securityboulevard.com - Author: Amy Cohn Why are Security Considerations Essential for Non-Human Identities Automation? The...
Source: securityboulevard.com - Author: Amy Cohn How Can Automated NHI Auditing Enhance Your Cybersecurity Strategy? Is...
Source: securityboulevard.com - Author: Claude Mandy AI Copilots and Agentic AI (those capable of independently taking...
Source: securityboulevard.com - Author: Ayelen Torello On March 12, 2025, The Federal Bureau of Investigation (FBI),...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Promo » Cybersecurity » BSides...
Source: securityboulevard.com - Author: Tova Dvorin On March 12, 2025, the Cybersecurity and Infrastructure Security Agency...
Source: securityboulevard.com - Author: Enzoic 2024 Enzoic AD Lite Password Auditor Report In an era where...
Source: securityboulevard.com - Author: Marc Handelman Friday, March 14, 2025 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Chris Garland Microsoft Threat Intelligence has issued new reporting about tactics being...
Source: securityboulevard.com - Author: Axio In the latest episode of Axio’s Executive Insight Series, CEO Scott...
Source: securityboulevard.com - Author: Amy Cohn How can we boost NHI provisioning speed while maintaining security?...
Source: securityboulevard.com - Author: Amy Cohn What Do Non-Human Identities Bring to the Table in DevOps?...
Source: securityboulevard.com - Author: Amy Cohn Should We Be Concerned About the Security of Dynamic NHIs...
Source: securityboulevard.com - Author: cybernewswire San Jose, Calif., Mar. 12, 2025, CyberNewswire — Aptori, a leader...
Source: securityboulevard.com - Author: Maycie Belmore What is an AI SOC? A Security Operations Center (SOC)...
Source: securityboulevard.com - Author: Marc Handelman Home » Promo » Cybersecurity » BSides Exeter 2024 –...
Source: securityboulevard.com - Author: Richi Jennings Outage outrage was a Ukrainian cyberattack, implies our favorite African...
Source: securityboulevard.com - Author: Votiro Generative AI (GenAI) and agentic AI are revolutionizing how businesses harness...
Source: securityboulevard.com - Author: Marc Handelman Thursday, March 13, 2025 Security Boulevard The Home of the...
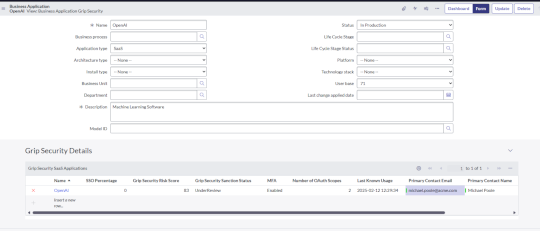
Source: securityboulevard.com - Author: Grip Security Blog Managing IT assets is already a complex challenge, but...
Source: securityboulevard.com - Author: Contrast Marketing Companies that sell software that can be used or downloaded...
Source: securityboulevard.com - Author: cybernewswire Boston, Mass., Mar. 11, 2025, CyberNewswire — GitGuardian, the security leader...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, March 12, 2025 Home » Promo » Cybersecurity »...