Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – IATC –...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Stevie Caldwell “The best-laid plans of mice and men often go awry.”...
Source: securityboulevard.com - Author: Thomas Sheehan One thing not often thought of is the lowly crash...
Source: securityboulevard.com - Author: Sekhar Poola Network infrastructure serves as the backbone of every organization’s IT...
Source: securityboulevard.com - Author: Kriti Tripathi The Channel Partners Conference & Expo, co-located with the MSP...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – IATC –...
Source: securityboulevard.com - Author: Pushpendra Mishra In today’s evolving digital landscape, cyber threats are becoming increasingly...
Source: securityboulevard.com - Author: Amy Cohn How Crucial are Non-Human Identities Compliance Metrics? Could you imagine...
Source: securityboulevard.com - Author: Amy Cohn Why Should Staff Be Trained on Non-Human Identities Compliance? Imagine...
Source: securityboulevard.com - Author: Amy Cohn How Can Non-Human Identities Improve Access Control Compliance? Is it...
Source: securityboulevard.com - Author: Neil Cohen Multi-modal AI has taken a major leap forward this year,...
Source: securityboulevard.com - Author: David Holmes Forrester just published its 2025 Web application Firewall Wave. As...
Source: securityboulevard.com - Author: Contrast Marketing Just because you work in a security operations center (SOC)...
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog Unstructured data ingestion...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – IATC –...
Source: securityboulevard.com - Author: Katie Fritchen ManagedMethods Helps Compass’s IT Team Save Time While Keeping Data...
Source: securityboulevard.com - Author: Chris Garland Backdoored Juniper networking devices are at the center of two...
Source: securityboulevard.com - Author: Gerry Gebel Trends in identity security for 2025 Managing multiple IDPs becomes...
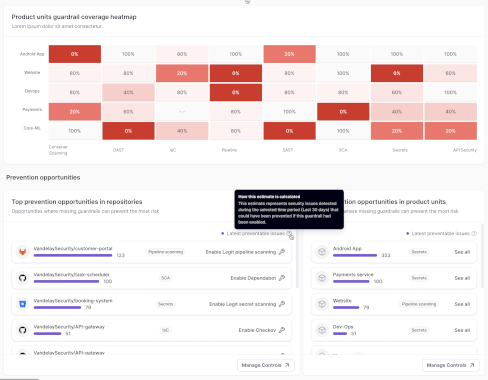
Source: securityboulevard.com - Author: Dan Mandel Get details on Legit’s new capabilities that allow AppSec teams...
Source: securityboulevard.com - Author: Amy Cohn Why Compliance Frameworks are Crucial for NHIs? Could the answer...
Source: securityboulevard.com - Author: Amy Cohn Is Your NHI Management GDPR Compliant? It isn’t just humans...
Source: securityboulevard.com - Author: Alon Yavin Now that AI reasoning capabilities are blasting and becoming accessible,...
Source: securityboulevard.com - Author: Michael Vizard Broadcom today updated its VMware vDefend platform to add additional...
Source: securityboulevard.com - Author: Laura Bruck At Constella, we’ve spent years analyzing how cybercriminals execute attacks...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – IATC –...
Source: securityboulevard.com - Author: adam_frans ADAMnetworks Licensed Technology Partner (LTP) Program Empowering MSPs, MSSPs & MDR...
Source: securityboulevard.com - Author: Veriti Research As the new Snow White movie arrives in theaters with...
Source: securityboulevard.com - Author: Rick Journalists aren’t usually invited to online chats about US war plans....
Source: securityboulevard.com - Author: cybernewswire FinTech and Communications Leader, IDT Corporation partners with AccuKnox to deploy...
Source: securityboulevard.com - Author: Dan White The domain name system (DNS) is an essential component of...