Source: securityboulevard.com - Author: Jeffrey Burt Former CISA director Chris Krebs, who has come under attack...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Pushpendra Mishra What is a White-Labeled XDR Platform? XDR stands for Extended...
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author What happens when your growing...
Source: securityboulevard.com - Author: Dwayne McDaniel Halifax has always been a city built on readiness. Its...
Source: securityboulevard.com - Author: Michael Wright The industry is evolving yet again. With the CA/Browser Forum’s...
Source: securityboulevard.com - Author: Amy Cohn Why is Cloud Security of Paramount Importance? It’s a well-acknowledged...
Source: securityboulevard.com - Author: Amy Cohn Are Interactions in Your Digital Environment Truly Secure? Cybersecurity has...
Source: securityboulevard.com - Author: Christine Falokun The constant battle between cybersecurity and automated threats has led...
Source: securityboulevard.com - Author: Robert L. Mitchell The National Institute of Standards and Technology’s latest guidance,...
BSidesLV24 – Common Ground – Security for AI Basics – Not by ChatGPT – Source: securityboulevard.com
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – Common Ground...
Source: securityboulevard.com - Author: Scott Fiesel by Source Defense When attackers are clever enough to name...
Source: securityboulevard.com - Author: Mudra Goyal We’re thrilled to announce that ColorTokens has been named a...
Source: securityboulevard.com - Author: Marc Handelman Friday, April 18, 2025 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Andy Suderman Migrating from on-premises infrastructure to the cloud is an important...
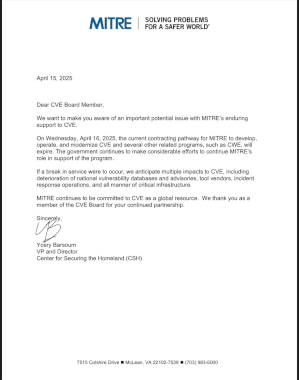
Source: securityboulevard.com - Author: Mend.io Communications As many of you may know, MITRE’s DHS contract to...
Source: securityboulevard.com - Author: Jeffrey Burt A cybersecurity specialist with the U.S. National Labor Relations Board...
Source: securityboulevard.com - Author: Shriram Sharma Security Operations Centers (SOCs) are under siege. The sheer volume...
Source: securityboulevard.com - Author: Bar-El Tayouri Introduction AI security threats are evolving at roughly the same...
Source: securityboulevard.com - Author: Tenable Security Response Team Concerns about the future of the MITRE CVE...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – Common Ground...
Source: securityboulevard.com - Author: Marc Handelman Thursday, April 17, 2025 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Brian Fox Yesterday’s headlines have sent ripples through the cybersecurity and software...
Source: securityboulevard.com - Author: MixMode Threat Research MixMode Threat ResearchMixMode Threat Research is a dedicated contributor...
Source: securityboulevard.com - Author: Bruce Schneier Mitre’s CVE’s program—which provides common naming and other informational resources...
Source: securityboulevard.com - Author: Tenable Research MITRE’s CVE program has been an important pillar in cybersecurity...
Source: securityboulevard.com - Author: Carly_Engelbrecht ADAMnetworks is excited to announce Wyo Support to the family of...
Source: securityboulevard.com - Author: Amy Cohn Why is Cloud Data Security vital for Modern Businesses? Cloud...
Source: securityboulevard.com - Author: Amy Cohn Where interactions between software, applications, and API components are crucial...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, April 16, 2025 Home » Security Bloggers Network »...
Source: securityboulevard.com - Author: Votiro One truth remains constant in the race to develop powerful AI...