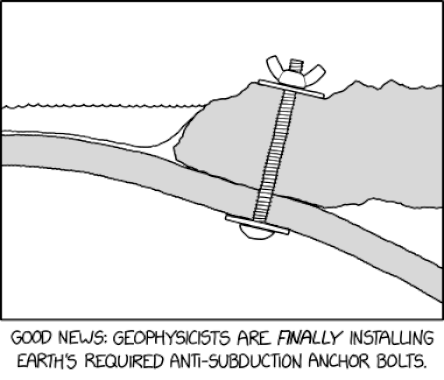
Source: securityboulevard.com - Author: Marc Handelman via the comic humor & dry wit of Randall Munroe,...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Contrast Marketing The majority — 11 out of 15 — of the...
Source: securityboulevard.com - Author: Brittany Bodane, Product Marketing Manager, AppOmni Edited on: April 22, 2025. Originally...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – Common Ground...
Source: securityboulevard.com - Author: Amy Cohn Is Secrets Scanning the Key to Assured Security? The alarming...
Source: securityboulevard.com - Author: Amy Cohn How Does Efficient IAM Support DevOps Teams? If you’re part...
Source: securityboulevard.com - Author: Amy Cohn Why do Financial Services Require Advanced Privileged Access Management (PAM)?...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – Common Ground...
Source: securityboulevard.com - Author: Marc Handelman Tuesday, April 22, 2025 Security Boulevard The Home of the...
Upwind Adds Ability to Detect API Threats to Cloud Security Platform – Source: securityboulevard.com
Source: securityboulevard.com - Author: Michael Vizard Upwind has added an ability to detect threats to application...
Source: securityboulevard.com - Author: Marc Handelman Our sincere appreciation to BSidesLV, and the Presenters/Authors for publishing...
Source: securityboulevard.com - Author: Mitchell Johnson With great power comes great responsibility. *** This is a...
Source: securityboulevard.com - Author: Robert Huber Each Monday, the Tenable Exposure Management Academy provides the practical,...
Source: securityboulevard.com - Author: Katie Fritchen Early Cloud Monitor adopter uses real-time insights to stop VPN...
Source: securityboulevard.com - Author: Amy Cohn Why Is Least Privilege Fundamental to Creating Safe Environments? Data...
Source: securityboulevard.com - Author: Amy Cohn Why is Management of Protected NHIs Essential? Protected Non-Human Identities...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – Common Ground...
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author The search landscape is undergoing...
Source: securityboulevard.com - Author: Amy Cohn Why is Value-Driven Secrets Management Essential in Today’s Cybersecurity Landscape?...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – Common Ground...
Source: securityboulevard.com - Author: Amy Cohn Can Advanced NHIDR Keep Your Cloud Environment Secure? Enriched with...
Source: securityboulevard.com - Author: Amy Cohn Understanding the Vitality of Non-Human Identities in Healthcare Data Protection...
Source: securityboulevard.com - Author: Amy Cohn Why Is Secrets Security Essential in Today’s Digital Landscape? Is...
Source: securityboulevard.com - Author: Amy Cohn Why Should Organizations Prioritize Proactive Secrets Rotation? Where digital connectivity...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – Common Ground...
Source: securityboulevard.com - Author: Max Aulakh Here at Ignyte, we talk a lot about various overarching...
Source: securityboulevard.com - Author: Grip Security Blog As a product management leader with years of experience...
Source: securityboulevard.com - Author: Sonatype RSA Conference (RSAC) brings together cybersecurity practitioners from across the globe...
Source: securityboulevard.com - Author: Scott Caveza, Ben Smith Proof-of-concept code has been released after researchers disclosed...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – Common Ground...