Source: securityboulevard.com - Author: Teri Robinson Move over, Michael Corleone and Tony Soprano, there’s a new...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: cybernewswire Miami, Aug. 28, 2025, CyberNewswire — Halo Security, a leading provider...
Source: securityboulevard.com - Author: Grip Security Blog The spotlight has finally swung toward the integration layer,...
Source: securityboulevard.com - Author: Marc Handelman Creator, Author and Presenter: Mike Privette Our deep appreciation to...
Source: securityboulevard.com - Author: FireMon Qué revela FireMon Insights sobre los riesgos de las políticas de...
Source: securityboulevard.com - Author: Scott Small At this year’s Black Hat USA conference, Scott Small, Director...
Source: securityboulevard.com - Author: Grip Security Blog SaaS security is like running from a bear. You...
Source: securityboulevard.com - Author: cybernewswire Miami, United States, August 28th, 2025, CyberNewsWire Halo Security, a leading...
Source: securityboulevard.com - Author: Marc Handelman Creators, Authors and Presenters: Danny Lazarev, Erez Harush Our deep...
Source: securityboulevard.com - Author: Jeffrey Burt Intelligence agencies in the United States and more than a...
Source: securityboulevard.com - Author: Alison Mack Why is Secrets Management a Strategic Imperative? Why are global...
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog The process of...
Source: securityboulevard.com - Author: Marc Handelman Creators, Authors and Presenters: Rohit Bansal, Zach Pritchard Our deep...
Source: securityboulevard.com - Author: Prasenjit Sarkar In our previous report, “The Coding Personalities of Leading LLMs,”...
Source: securityboulevard.com - Author: Francis Guibernau Introduction Warlock is a ransomware strain operating under the Ransomware-as-a-Service...
Source: securityboulevard.com - Author: Carly_Engelbrecht Summary “The Defenders Log” Episode 1 features host David Redekop and...
Source: securityboulevard.com - Author: Michael Vizard DigiCert revealed today that over the last month it has...
Source: securityboulevard.com - Author: Marc Handelman via the cosmic humor & dry-as-the-desert wit of Randall Munroe,...
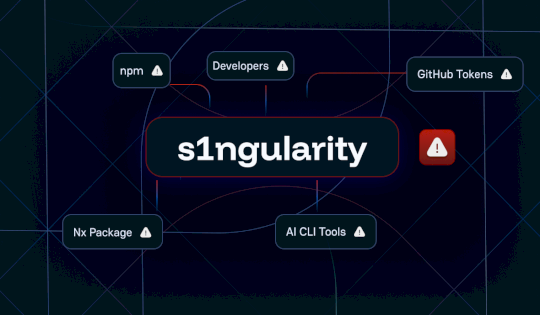
Source: securityboulevard.com - Author: Guillaume Valadon This supply chain attack combines credential theft, environmental sabotage, and...
Source: securityboulevard.com - Author: Michael Vizard Broadcom today added a slew of cybersecurity updates, including a...
Source: securityboulevard.com - Author: Matthew Rosenquist Microsoft recently introduced a new framework designed to assess...
Source: securityboulevard.com - Author: Scott Caveza Citrix has released patches to address a zero-day remote code...
Source: securityboulevard.com - Author: Marc Handelman via the comic artistry and dry wit of Randall Munroe,...
Source: securityboulevard.com - Author: cybernewswire Dover, Del., Aug. 25, 2025, CyberNewswire—Attaxion announces the addition of the...
Source: securityboulevard.com - Author: Jeffrey Burt A GOP congressman from Arizona has filed legislation to allow...
Source: securityboulevard.com - Author: George McGregor To protect against Man-in-the-Middle (MitM) attacks in mobile, you need...
Source: securityboulevard.com - Author: richard-r.stewart@thalesgroup.com What is Single Sign-On (SSO) richard-r.stew… Fri, 08/22/2025 - 16:53 Single...
Source: securityboulevard.com - Author: Jeffrey Burt Noah Michael Urban, a 20-year-old Florida man, was sentenced for...
Source: securityboulevard.com - Author: Michael Vizard A survey of 400 cybersecurity professionals from organizations with more...
Source: securityboulevard.com - Author: The CISO Perspective Learn how to implement Zero Trust Architecture in practice....