Source: securityboulevard.com - Author: Alison Mack Why is a Comprehensive Cybersecurity Strategy Essential? A robust cybersecurity...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Alexa Sander Student mental well-being is continuing to worsen. 40% of school-aged...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – GroundFloor –...
Source: securityboulevard.com - Author: Brian Bensky The shift to cloud-native infrastructure has introduced a difficult dilemma...
Source: securityboulevard.com - Author: FireTail - AI and API Security Blog May 15, 2025 – Lina...
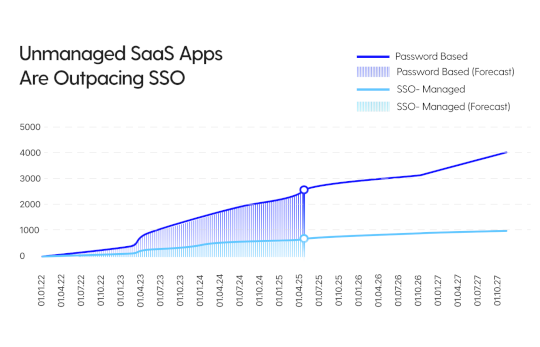
Source: securityboulevard.com - Author: Grip Security Blog Even the most mature enterprises encounter new, subtle, and...
Source: securityboulevard.com - Author: Alison Mack Are You Safe With Your Current Non-Human Identity Security? The...
Source: securityboulevard.com - Author: Alison Mack Can Continuous Improvement in NHIs Management Be the Key to...
Source: securityboulevard.com - Author: Alison Mack How Can We Cultivate Trust with Secure NHIs Practices? When...
Source: securityboulevard.com - Author: Alison Mack Why is Independent Secrets Management Crucial for Cybersecurity? How crucial...
Source: securityboulevard.com - Author: Devesh Patel Introduction: Why Your App Needs SCIM Yesterday Picture this: Your...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – GroundFloor –...
Source: securityboulevard.com - Author: Ankit Agarwal Make SSOJet’s API documentation accessible and easy to understand for...
Hacking the Hardware Brains of Computers is the Ultimate Cyberattack – Source: securityboulevard.com
Source: securityboulevard.com - Author: Matthew Rosenquist Compromising the hardware layer, especially the CPU, is the Holy...
Source: securityboulevard.com - Author: Marc Handelman Thursday, May 15, 2025 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Ben Smith Remote code execution vulnerability in a popular mobile device management...
Source: securityboulevard.com - Author: Alison Mack Are You Maximizing the Potential of Your IAM Strategies? Effective...
Source: securityboulevard.com - Author: Alison Mack Is Your Secrets Management Strategy Straining Your Budget? Organizations are...
Source: securityboulevard.com - Author: Alison Mack Why is the Strategic Management of NHIs Essential? How do...
Source: securityboulevard.com - Author: Alison Mack How Does Proactive Non-Human Identity Management Keep You Ahead? Cybersecurity,...
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author Have you ever received a...
Source: securityboulevard.com - Author: Tenable Security Response Team 5Critical 66Important 0Moderate 0Low Microsoft addresses 71 CVEs...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – GroundFloor –...
Source: securityboulevard.com - Author: Jody Brazil The recent failure of Skybox has left many companies without...
Source: securityboulevard.com - Author: Mary Yang The Security Gap JPMorgan Chase’s CISO Didn’t Mention — And Why It’s...
Source: securityboulevard.com - Author: Alison Mack How Critical is the Role of Non-Human Identities in Keeping...
Source: securityboulevard.com - Author: Alison Mack Are Your Cyber Security Measures Really Impenetrable? When it comes...
Source: securityboulevard.com - Author: Alison Mack Is Securing Non-Human Identities (NHIs) a Cybersecurity Game-Changer? Understanding the...
Source: securityboulevard.com - Author: Katie Bykowski How to Automate Vulnerability Management Processes Vulnerability lifecycle management is...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – GroundFloor –...