Source: securityboulevard.com - Author: Alison Mack Are We Maximizing Our Security Investments? Organizations must justify their...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Alison Mack Why is Security Certainty a Necessity in Today’s Cybersecurity Landscape?...
Source: securityboulevard.com - Author: Christine Falokun Open Banking is transforming the way consumers manage their finances,...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – PasswordsCon –...
Source: securityboulevard.com - Author: Apurva Dave AI identity is not yet a fully formed concept. We...
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog As we step...
Source: securityboulevard.com - Author: Michael Vizard A survey of 2,058 security leaders finds nearly half of...
Source: securityboulevard.com - Author: FireTail - AI and API Security Blog May 21, 2025 – Lina...
Source: securityboulevard.com - Author: Rajesh Khazanchi Over the past few months, I’ve spoken with CISOs across...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – GroundFloor –...
Source: securityboulevard.com - Author: Alison Mack How Can You Make Cybersecurity Budget Allocations Effective? How do...
Source: securityboulevard.com - Author: Alison Mack Is Choosing Cloud Security a Complex Task? From financial services...
Source: securityboulevard.com - Author: FireMon Today’s enterprises have embraced digital evolution. Business deals are conducted in...
Source: securityboulevard.com - Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – GroundFloor –...
Source: securityboulevard.com - Author: psilva SLASH YOUR MTTR! Join Us for a Live Webinar on Faster...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, May 21, 2025 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Mark Klinchin Microsegmentation has become a foundational component of enterprise security and...
Source: securityboulevard.com - Author: MixMode Threat Research MixMode Threat ResearchMixMode Threat Research is a dedicated contributor...
Source: securityboulevard.com - Author: Mend.io Communications Application security testing (AST) is the process of identifying and...
Source: securityboulevard.com - Author: Oskar Zeino-Mahmalat, Paul Gerste Welcome back to the second part of our...
Source: securityboulevard.com - Author: Alison Mack Does your Organization Struggle with Compliance? If so, you’re not...
Source: securityboulevard.com - Author: Alison Mack Feeling Overwhelmed By the Complexity of Cybersecurity? Are you one...
Source: securityboulevard.com - Author: Alison Mack Understanding the Realm of Non-Human Identities in Cloud Security Is...
Source: securityboulevard.com - Author: Alison Mack Why is Identity Theft Prevention a Vital Component of Good...
Source: securityboulevard.com - Author: Grip Security Blog The rise of SaaS has unlocked new ways to...
Source: securityboulevard.com - Author: Scott Fiesel by Source Defense Don’t Trust Your Online Revenue Channel to...
Source: securityboulevard.com - Author: Contrast Labs Customers using Application Detection and Response (ADR) technology blocked a...
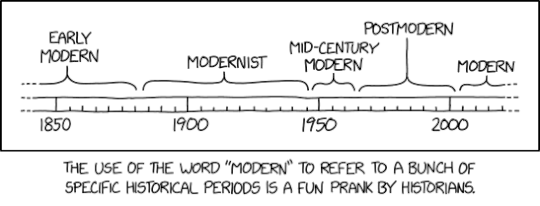
Source: securityboulevard.com - Author: Marc Handelman via the inimitable Daniel Stori at Turnoff.US! Permalink *** This...
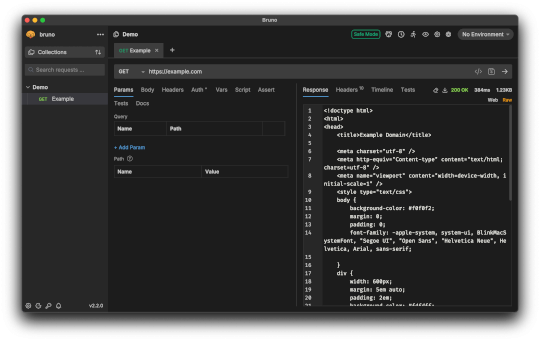
Source: securityboulevard.com - Author: Aaron Linskens Docker remains a cornerstone of modern development environments, helping teams...
Source: securityboulevard.com - Author: bacohido By Byron V. Acohido Stephen Klein didn’t just stir the pot....