National Critical Infrastructure Under Attack: Clop Ransomware National Critical Infrastructure Under Attack: Clop Ransomware On August...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Fall Foliage: JavaScript/OJS Edition I’ve been (mostly) keeping up with annual updates for my R/{sf} U.S....
A Pocket Guide to FAIR FAIR, short for Factor Analysis of Information Risk, is a risk...
How Governments Request Your Data From Service Providers A recently-released Surfshark report looked into global inquiries...
Nelnet breach affects 2.5M student loan accounts; Google releases emergency Chrome security update The new school...
10 Best IT Compliance Conferences in 2022 Networking, insights, news, and more! IT compliance conferences are...
What is Mayhem for API? Mayhem for API automates testing REST APIs by bringing the full...
Is your phone Safe For Scrollers (SFS)? Shan Boodram — certified sexologist, intimacy educator, podcast host,...
BSides Vancouver 2022 – Darren Thurston’s And Jenn Lemmen’s ‘Our Experiences Finding Missing People With TraceLabs...
Top Obstacles and 6 Best Practices for Cloud Data Backups | Eureka Security When looking at...
Kubernetes Security, Cost Avoidance and Policy Go Hand in Hand Kubernetes security continues to be one...
LogonBox SSPR 2.3.17 Introduction LogonBox is pleased to announce the immediate availability of LogonBox SSPR 2.3.17.This...
LognBox VPN 2.3.17 IntroductionLogonBox is pleased to announce the immediate availability of LogonBox SSPR 2.3.17.This release...
FBI Warning on Credential Stuffing & Residential Proxies is Good News – Bad News The FBI...
Channel 4 optimizes cybersecurity and boosts efficiency after partnering with Invicti Using Invicti for vulnerability scanning...
Top 5 Zero-Day Vulnerabilities of August Zero day vulnerabilities and exploits are unexpected, hence zero-day protection...
Password Reuse is Putting MSP’s at Risk Password hygiene is a huge priority for Managed Service...
Google Vulnerability Reward Program Focuses on Open Source Software Google’s bug bounty program will be expanded...
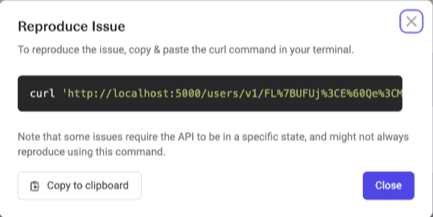
The Mayhem for API Difference – A ZAP – API Scan Comparison With the rapid development...
Using Backups to Turn the Tables on Ransomware When an enterprise gets hit with ransomware, the...
Cloud-Based File Systems as a Ransomware Defense Ransomware is an unfortunate and unavoidable fact of life...
California Regulators Hit Sephora with $1.2M Fine Regulators have roared back from a pandemic-induced stupor that...
Orgs Report Mixed Progress on Ransomware Defense A survey of 400 technology, financial and security leaders...
BSides Vancouver 2022 – Josh Dominguez’ ‘Tips And Advice For Your Early Journey In Cybersecurity’ Our...
United States Labor Day 2022 Construction workers sit on a New York City skyscraper girder in...
Identity Verification for Telehealth: A New Boon To The Medical Industry Telehealthcare Sector is one of...
Extra, Extra, VERT Reads All About It: Cybersecurity News for the Week of August 29, 2022...
How to address IoT security challenges? My first association with IoT was way back in 2016....
What is Flutter? Is Flutter a Good Business Prospective? Flutter makes it easier for developers to...
Paul’s Security Weekly #753. “Data Integrity Lights the Way: Security With the Decentralized Web” I joined...