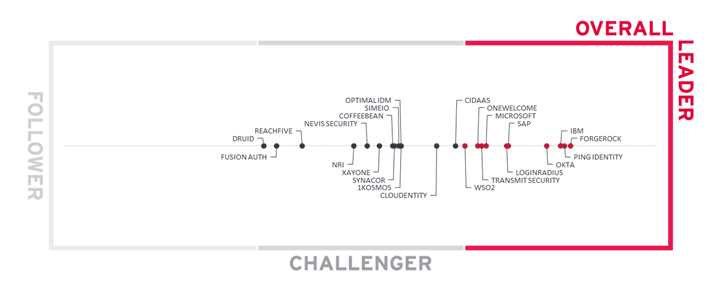
The Road to Passwordless is Paved with Orchestration A new report from KuppingerCole Names ForgeRock an...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
BSidesLV 2022 Lucky13 I Am The Cavalry (IATC) – Allan Friedman’s, Adam Kojak’s, Katie Bratman’s, Chris...
Security Advisory for OpenSSL Vulnerabilities CVE-2022-3602 & CVE-2022-3786 Background On 01-Nov-2022, OpenSSL published an advisory about...
SOVA – A New Android Banking Trojan Introduction How many people are aware of the new...
Complete Guide on Comodo Code Signing Certificate Comodo is a cybersecurity solutions provider helping businesses and...
Measuring Up: How to Architect a Systematic Security Program – Part 2 In Part 1 of...
See Tickets Breach Sheds Light on the Blind-Side of Web Security Despite its name, leading ticketing...
BSidesLV 2022 Lucky13 I Am The Cavalry (IATC) – Lily H. Newman’s, Joe Uchill’s, Suzanne Smalley’s...
Using Binary Analysis to Hunt Down OSS Vulnerabilities Having an SBOM and software inventory aids in...
Using Sysmon for Linux to Monitor Against MITRE ATT&CK Techniques There was a lot covered at...
Hacking with your Browser Today I rebuilt my Windows 7 partition. Amidst flurry of backing up...
Metasploit Buyout Today HD Moore and Rapid7 announced that Rapid7 has purchased the Metasploit Framework Project....
Network Pentest Lab Remember those good ole days in the sandbox? Where you threw stuff around...
New to reversing? The differences between IDA Pro, ImmDBG and OllyDBG Introduction In this blog post...
More API Inventory Auditing Necessary to Limit Incidents The API industry is booming. Development of application...
Hacking with your Browser Today I rebuilt my Windows 7 partition. Amidst flurry of backing up...
Metasploit Buyout Today HD Moore and Rapid7 announced that Rapid7 has purchased the Metasploit Framework Project....
Network Pentest Lab Remember those good ole days in the sandbox? Where you threw stuff around...
New to reversing? The differences between IDA Pro, ImmDBG and OllyDBG Introduction In this blog post...
Secure Software Development Compliance for OMB’s M-22-18 Memo | Code Patrol Podcast | Contrast Security Do...
A False Assumption of Trust in Business APIs Digital business is driving significant levels of growth...
More API Inventory Auditing Necessary to Limit Incidents The API industry is booming. Development of application...
SuperTravel Protects its Proprietary Data From Scraping With DataDome After testing multiple bot protection technologies, SuperTravel...
How to protect against CVE-2022-42889 | Text4Shell vulnerability protection | Contrast Security A new Common Vulnerability...
Hard Truths About Driving a Security Mindset Working in cybersecurity as a consultant can be eye-opening....
Secure Software Development Compliance for OMB’s M-22-18 Memo | Code Patrol Podcast | Contrast Security Do...
A False Assumption of Trust in Business APIs Digital business is driving significant levels of growth...
SuperTravel Protects its Proprietary Data From Scraping With DataDome After testing multiple bot protection technologies, SuperTravel...
How to protect against CVE-2022-42889 | Text4Shell vulnerability protection | Contrast Security A new Common Vulnerability...
Hard Truths About Driving a Security Mindset Working in cybersecurity as a consultant can be eye-opening....