Is your cloud ready for CCPA? New Year’s resolutions aren’t the only thing you should be...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
The Year in Review and 2023 Predictions In our last episode of the year, we discuss...
AppsMas: Onapsis Platform 2022 Highlights AppsMas: Onapsis Platform 2022 Highlights ltabo Fri, 12/23/2022 – 12:43 SAP...
Top 10 Risks in Cyber Security Increasing cyber security threats continue creating problems for companies and...
Cyber Themed Drink Ideas to Help You Get in the Holiday Spirit Most of us look...
Best of 2022: 25+ Vulnerable websites to practice your ethical hacking skills Vulnerable websites are built...
Best of 2022: npm Libraries ‘colors’ and ‘faker’ Sabotaged in Protest by Their Maintainer—What to do...
The Top 23 Security Predictions for 2023 (Part 1) After a year full of data breaches,...
USENIX Security ’22 – Yijing Liu, Yan Jia, Qingyin Tan, and Zheli Liu, Luyi Xing ‘How...
Insurance and Regulations May Be the Biggest Security Drivers of 2023 | Lookout When talking about...
Randall Munroe’s XKCD ‘Cold Complaints’ via the comic artistry and dry wit of Randall Munroe, resident...
PGP vs. sigstore: A Recap of the Match at Maven Central At Sonatype, a great presentation...
An update on international data privacy protection The 38 member countries of the Organization for Economic...
How to Use an HTTP Archive (HAR) With Mayhem Learn how to fuzz an API without...
Report Surfaces Top Vulnerabilities of 2022 Rezilion, a vulnerability management platform provider, shared a list of...
Critical Microsoft Code-Execution Vulnerability A critical code-execution vulnerability in Microsoft Windows was patched in September. It...
Best of 2022: The Role of AI in Cybersecurity It’s clear that AI can be a...
Infostealer Malware Threat Grows as MFA Fatigue Attacks Spread Information stealer malware flourished on underground criminal...
Moving Containers: Uncovering Challenges. Finding Solutions. Get expert tips and best practices for securing containers in...
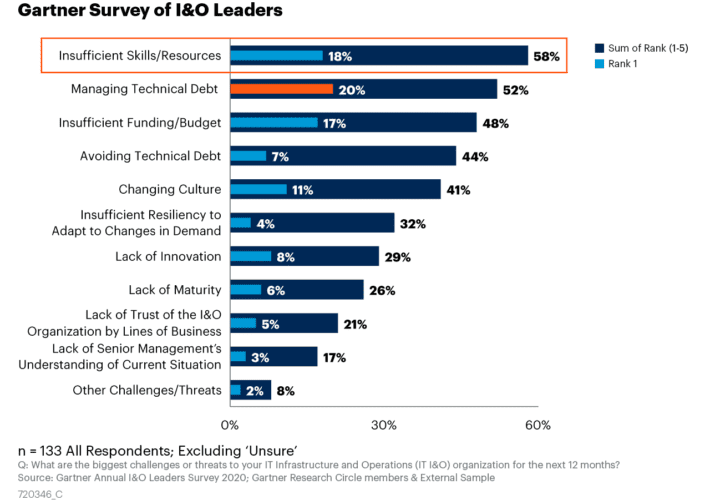
How to Address the Skills Gap Crisis with DCIM Software Data centers are essential components of...
Lacework Stiffens Cloud Security Posture Management Lacework has added additional cloud security posture management (CSPM) capabilities...
LogRhythm Partners with SentinelOne to Accelerate Prevention, Detection and Response for Enterprise Environments New integration empowers...
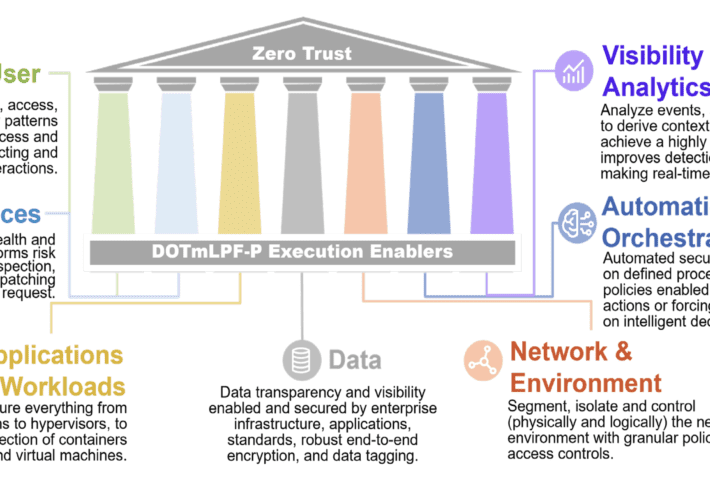
ForgeRock and the new DoD Zero Trust Strategy On November 7, 2023, the United States Department...
Analysts Rate Tesla Mediocre Car Not Even Worth $20 Stock: “too unreliable for widespread use” A...
Exposing the “Data Leaks” Paradise – An Analysis In a world dominated by a countless number...
Ostrich Cyber-Risk Welcomes Chip Whitmer as Vice President of Software Development Ostrich Cyber-Risk Appoints Chip Whitmer as...
Specific IoT and OT security predictions for North America for 2023 The year 2023 will see...
DoD supply chain lessons learned A July 2022 survey of 300 U.S. Department of Defense (DoD)...
This year’s hottest tech: Related privacy concerns The holiday season is upon us, and many of...
Know Your Gamer: The Need for Identity Verification in the Gaming Industry 2023 Isn’t it time...