Aite-Novarica Names Radware’s Bot Manager Solution Best-In-Class The Aite Matrix: Leading Bot Detection and Management Provders...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
KubeCrash Spring 2023 is Here! Learn From Crash Courses on Cloud Native KubeCon EU is just...
USENIX Security ’22 – Fangming Gu, Qingli Guo, Lian Li, Zhiniang Peng, Wei Lin, Xiaobo Yang,...
Building smarter DevSecOps with Intelligent Orchestration Intelligent Orchestration takes the complexity out of DevSecOps by delivering...
Private Malware for Sale: A Closer Look at AresLoader In December 2022, a private loader named...
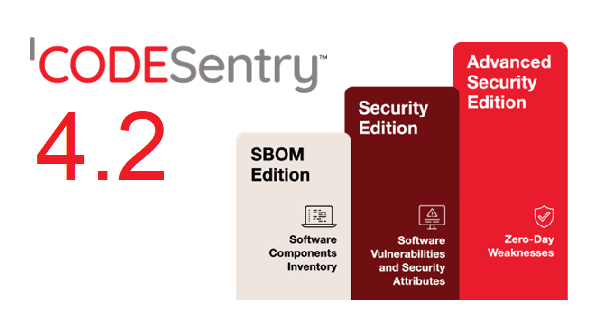
Announcing CodeSentry 4.2 with New Editions and Component Search GrammaTech’s leading binary Software Composition Technology (SCA)...
New Report “State of Cloud Threat Detection and Response” Cloud D&R Report (2023) One of the mysteries...
Your Guide to Secure Code Signing: Four Steps to Get Started Without code signing – or...
#LifeAtLogRhythm Spotlight – Diversity, Equity, and Inclusion (DEI) Collective It’s time for round two of our...
Shared Responsibility Model: What It Means for Cloud Security The shared responsibility model is a cloud...
Marriott Hosts “I love Hitler” Rally in Washington DC Marriott has a long and sordid history...
The State of the Security Team The success of the cybersecurity team requires support across the...
5 Tactical Tips For Security Teams Using AWS Security teams face new and unique challenges as...
Find More Secrets with Nosey Parker v.0.12.0 On March 2, 2023, we issued some updates to...
6 Ways to Vet Your Next ASM Vendor Attack surface management (ASM) is a critical security...
USENIX Security ’22 – Shravan Srinivasan, Alexander Chepurnoy, Charalampos Papamanthou, Alin Tomescu, Yupeng Zhang – ‘Hyperproofs:...
ZTNA and the Death of the Network Perimeter Tony Bradley Editor-in-Chief at TechSpective Zero...
New National Cybersecurity Strategy: What Do You Need to Know? The White House released a new...
Personal data [G Temp] The post Personal data [G Temp] appeared first on Click Armor. The...
Key Security Wins 2022: Securing the Future Security is becoming more and more important and this...
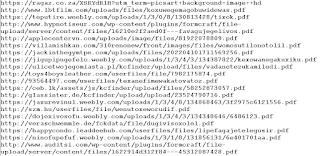
Clustering Phishing Campaign’s Rogue and Fraudulent and Malicious Hosting Infrastructure Pointing to Massive IPFS Web 3.0...
USENIX Security ’22 – Jiaheng Zhang , Tiancheng Xie, Thang Hoang, Elaine Shi, Yupeng Zhang –...
Autonomous Vehicles Need No Drugs Or Drink To Be Bad Drivers Humans often get cited for...
USENIX Security ’22 – Ning Luo, Samuel Judson, Timos Antonopoulos, Ruzica Piskac, Yale University; Xiao Wang...
National Cybersecurity Strategy | Contrast Security Time for the gloves to come off, the U.S. government...
Digital Trust Digest: This Week’s Must-Know News The Digital Trust Digest is a curated overview of...
Exposing the “PDF Botnet” – An OSINT Analysis Dear blog readers, I’ve recently stumbled upon a...
Randall Munroe’s XKCD ‘Fanservice’ via the comic artistry and dry wit of Randall Munroe, resident at...
Cowbell Adds Free Cybersecurity Services for Insurance Policy Holders Cowbell this week added a free 24/7...
Defeating Malvertising-Based Phishing Attacks Malvertising Enters a New Age While Google grapples with the potential threat...

















![Personal data [G Temp]](https://ciso2ciso.com/wp-content/uploads/2023/03/Click-Armor-Blog-Photos-2-VXSYNs-710x500.png)