US National Cybersecurity Strategy: What It Means for Digital Identity The Biden-Harris Administration recently released its...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Rise in “Ghost” Tankers Delivering Russian Oil to Asia Someone is buying up old decrepit tankers,...
BlackLotus Malware Hijacks Windows Secure Boot Process Researchers have discovered malware that “can hijack a computer’s...
Extend Access Governance for SAP Strategic partnership to address SAP access governance challengesDallas, Texas, March 8,...
How to Provision Serverless Resources with Terraform by HashiCorp As more and more companies migrate their...
Lockbit Ransomware Dominant Even as Overall Attack Rates Fall With victims from 23 countries, Lockbit continues...
How Coding Changed My Life The post How Coding Changed My Life appeared first on...
1Password Leverages SSO Service to Better Protect Secrets 1Password announced today general availability of a single...
3 Reasons Women Should Reskill to Work in Cybersecurity As women, from a young age, being...
Business Email Compromise: 3 Steps to Reduce Risk Email has been a popular delivery of malware...
Solving Cybersecurity Staff Churn Staff churn is a huge issue for the cybersecurity industry. Frustrations are...
USENIX Security ’22 – Simon Rohlmann, Christian Mainka, Vladislav Mladenov, Jörg Schwenk – ‘Oops… Code Execution...
OWASP API Security Top 10: Upcoming Changes You Need To Know About Check out these changes...
BlackMamba: Using AI to Generate Polymorphic Malware New Threats Emerging The introduction of ChatGPT last year...
White House cyber strategy: A love/hate story The post White House cyber strategy: A love/hate story...
Do You Want to Know a Secret? Just Take a Look Inside Top Finance Apps Financial apps...
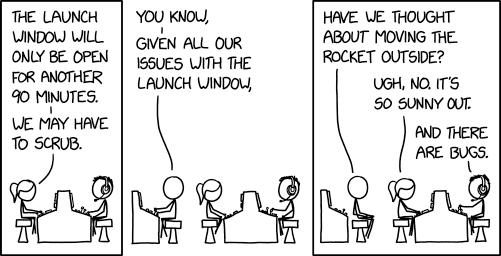
Randall Munroe’s XKCD ‘Launch Window’ via the comic artistry and dry wit of Randall Munroe, resident...
What the LastPass Hack Says About Modern Cybersecurity Online password managers are meant to help users...
App sec is addicted to vulnerabilities: Why supply chain security requires evolution As application security professionals...
Stop DDoS Attacks From Hurting Your Business Distributed denial of service (DDoS) attacks are a growing...
USENIX Security ’22 – Moritz Schloegel, Tim Blazytko, Moritz Contag, Cornelius Aschermann, and Julius Basler, Thorsten...
Grip secures SaaS identities and SSPM for identity fabric Grip is critical layer for securing today’s...
Hybrid Systems: AI and Humans Need Each Other for Effective Cybersecurity The sudden mainstreaming of chatbots...
How federal agencies can prevent evasive web threats 2023 is shaping up to be a transformative...
3 Things Businesses Need to Know About Safely Employing Contractors Many organizations are turning to consultants...
Dismantling the Ransomware Business Model Every day, coordinated crime groups are developing more advanced skills to...
Introducing The Complete Guide to SecDataOps and Vulnerability Management on AWS After going back and forth...
How to Secure Microsoft 365 in 2023 By a wide margin, Microsoft 365 is the world’s...
Women’s Day: Naomi Buckwalter & Megan Baker | Code Patrol podcast | Contrast Security Happy International...
USENIX Security ’22 – Seunghoon Woo, Hyunji Hong, Eunjin Choi, Heejo Lee – ‘MOVERY: A Precise...