Why Organizations Need to Care About Machine Identity Management Machine Identity Management (MIM) is an essential...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
USENIX Security ’22 – Timothy Trippel, Kang G. Shin, Alex Chernyakhovsky, Garret Kelly, Dominic Rizzo, Matthew...
50 Threat Hunting Hypothesis Examples Threat hunting is a proactive and critical aspect of cybersecurity that...
Almost Bare Bones WebR Starter App Let’s walk through how to set up a ~minimal HTML/JS/CS...
Hyperview Appoints Digital Infrastructure Leader Bill Kleyman to Advisory Board Award-winning data center, cloud, and digital...
Unveiling the Shadow AI: The Rise of AI Reliance in Cybersecurity Artificial Intelligence (AI) has been...
Top Changes in the OWASP API Security Top 10 2023RC The OWASP API project has recently...
Procurement Guide Offers Best Practices for Moving to Cloud The Center for Digital Government just released...
USENIX Security ’22 – Xiaochen Zou, Guoren Li, Weiteng Chen, Hang Zhang, Zhiyun Qian – ‘SyzScope:...
Hunting Emotet: How Behavioural Hunting Trumps IOC Detection Every Time As a threat hunter, I have...
USENIX Security ’22 – Shujiang Wu, Jianjia Yu, Min Yang, Yinzhi Cao – ‘Rendering Contention Channel...
A security use case for ChatGPT: Email Scam Robo Judge I have been noodling around with...
‘Extraordinary, Egregious’ Data Breach at House and Senate Capitol Trouble: Senators, representatives and staffers suffer PII...
Vendor Tips for the SIG Questionnaire Many companies understand the pain of constantly filling out extremely...
USENIX Security ’22 – Mohammadkazem Taram, Xida Ren, Ashish Venkat, Dean Tullsen – ‘SecSMT: Securing SMT...
Digital Trust Digest: This Week’s Must-Know News The Digital Trust Digest is a curated overview of...
Sick of that Security Questionnaire? Automation is the Answer Security questionnaires (SQs) are not fun. They’re...
Camelot Launches Cybersecurity Service Augmented by ML Camelot this week launched a Secure360 cybersecurity platform that...
Securing Software for Healthy, Energy-Efficient Smart Buildings Jason Christman, Vice President and CPSO of Johnson Controls,...
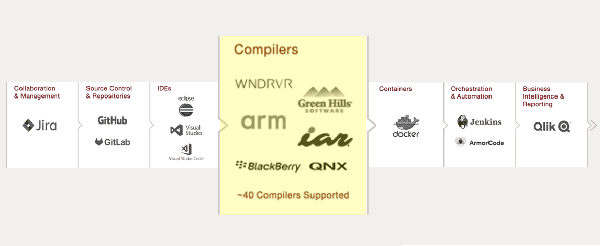
SAST Tools Must Support Your Embedded Operating Systems, Toolchains & Compilers – Chose Wisely Embedded software...
Reducing Risks and Threats with Continuous SaaS Compliance CISOs and GRC officers are quickly recognizing the...
Fighting Bots and Saving Costs in a Time of Shrinking Resources Being a Chief Information Security...
HPE Acquires Axis Security to Gain SSE Platform Hewlett-Packard Enterprise (HPE) has announced its intent to...
Addressing TSA’s Aviation Security Emergency Mandates for Airlines and Airports The Department of Homeland Security (DHS)...
Why software transparency is critical: Understanding supply chain security in a software-driven society By now the...
USENIX Security ’22 – Chaoshun Zuo, Zhiqiang Lin – ‘Playing Without Paying: Detecting Vulnerable Payment Verification...
Managing Cloud Compliance and Security Posture Why compliance and access security in the public cloud are...
Palo Alto Networks Adds Identity Module to Integrated SOC Platform Palo Alto Networks this week revealed...
International Women’s Day: Recognizing Contributions of RiskLens Women The theme of this year’s International Women’s Day...
“Team Jorge” Exposed for Disinformation Campaigns Targeting Presidential Elections There’s an interesting detail in the reports...