How Cybercriminals Will Exploit the Fear Surrounding SVB’s Collapse The collapse of Silicon Valley Bank (SVB)...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Announcing Our 2023 Product of the Year Award: What It Means for Our Customers | Eureka...
Detecting CVE-2023-23397: How to Identify Exploitation of the Latest Microsoft Outlook Vulnerability
Detecting CVE-2023-23397: How to Identify Exploitation of the Latest Microsoft Outlook Vulnerability Microsoft recently released patches...
Ethics in AI: The Missing Code As part of its push toward artificial intelligence, Microsoft laid...
Guild Education Gives Salt an A+ for API Protection Keeping our customers’ data safe so that...
How to Protect Your Company in a ChatGPT World With the potential to be as game-changing...
The Week in Security: YoroTrooper steals credentials in Europe, AI-created videos spread malware Welcome to...
COURT DOC: Justice Department Investigation Leads to Takedown of Darknet Cryptocurrency Mixer that Processed Over $3...
The Risks of Using ChatGPT to Write Client-Side Code Since OpenAI released its AI chatbot software...
USENIX Security ’22 – Kinan Dak Albab, Rawane Issa, Mayank Varia, Kalman Graffi – ‘Batched Differentially...
The Evolution of Ransomware and how to Protect Against it Ransomware is a form of malicious...
Breadth of Data: Why it Matters The last decade has seen tremendous growth in the availability...
Botnet Protection For more than a decade, Constella Intelligence–formerly 4iQ–has been hunting, collecting, and curating breach...
How to Measure Your Risk Monitoring Activities This article was originally featured in ASIS International Ideally,...
The Comprehensive Value of Investing in Both Cybersecurity and Cyber Insurance With ransomware attacks, social engineering,...
Fidelis Cybersecurity’s Network Detection and Response (NDR) with Data Loss Prevention (DLP) and Deception Provides Several...
The Downside to March Madness – a Busted Bracket and a Data Breach Back in the...
USENIX Security ’22 – Varun Madathil, Alessandra Scafuro, István András Seres, Omer Shlomovits, Denis Varlakov –...
Thwarting Threats in Healthcare: The Art of Threat Hunting In the healthcare industry, protecting patient data...
Taylor Swift Tour: Let’s Analyze Cyber Risk for a Ticket Company Taylor Swift starts The Eras...
Benefits of Real-Time Bot Detection For those unaware, the bot revolution is happening right before our...
Phishing for Financial Fears Over the last 4 days (as of the writing of this blog)...
Deep web vs. dark web: What businesses should know about both The everyday internet presents a...
Palo Alto Networks Uses Machine Learning to Reduce SASE Costs Palo Alto Networks today revealed it...
Raising Awareness of Connected Device Security October is officially cybersecurity awareness month, originally designated back in...
Data Protection Strategy for Resource-Strapped IT Teams IT teams are increasingly asked to do more with...
Protecting Your Organization’s Digital Identity: A Guide to Managed Attribution Managed attribution has become a powerful...
(Ab)using Adobe Acrobat Sign to distribute malware Bad actors have been distributing malware through email for...
Cyber Risk Quantification based on the MITRE ATT&CK® Framework Articles related to cyber risk quantification, cyber...
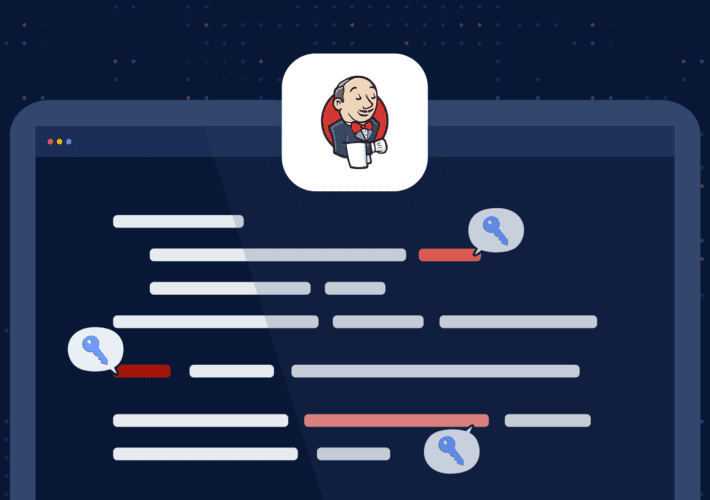
How to Handle Secrets in Jenkins DevOps engineers must handle secrets with care. In this series,...