How to Distinguish Bot vs. Human Traffic Not so long ago, bots were considered a modern-day...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Microsoft Outlook Remote Hash Vulnerability (CVE-2023-23397) The post Microsoft Outlook Remote Hash Vulnerability (CVE-2023-23397) appeared first...
USENIX Security ’22 – Xudong Pan, Mi Zhang, Beina Sheng, Jiaming Zhu, Min Yang – ‘Hidden...
Linking Lit’s Lightweight Web Components And WebR For Vanilla JS Reactivity See it live before reading!...
A Former FBI Agent’s Thoughts: National Cybersecurity Strategy The government just released its new National Cybersecurity...
Robert M. Lee’s & Jeff Haas’ Little Bobby Comic – ‘WEEK 422’ via the respected security...
[New Live Series] Dev Chat with Dan Conn: Beware of Malware The post [New Live...
Women’s History Month at RiskLens: More Voices For Women’s History Month, we are asking RiskLens staff...
Investing in People Doesn’t Take AI Investing in People Doesn’t Take AI AI is not an...
Automate your DevSecOps to take the pressure off triage Tools like Code Dx that support automation...
Software supply chain security practices are maturing — but it’s a work in progress Many software...
USENIX Security ’22 – Agnieszka Dutkowska-Zuk, Austin Hounsel, Amy Morrill, Andre Xiong, Marshini Chetty, Nick Feamster...
Embracing Biometric Identity Verification: A Look at Belgium and Kuwait Telecoms The country’s telecom authority has...
DNSSEC is the Key to a Healthy Future for the Internet The future of internet connectivity...
Identity Fabric: Why it’s Important for Identity Security Understand what an identity fabric is and its...
Six Ways to Foster a Security Mindset in Engineering Teams Human error can be found at...
Why You Should Opt Out of Sharing Data With Your Mobile Provider A new breach involving...
How Hackers are Exploiting Cloud Organizations | Eureka Security Protect your organization from data breaches in...
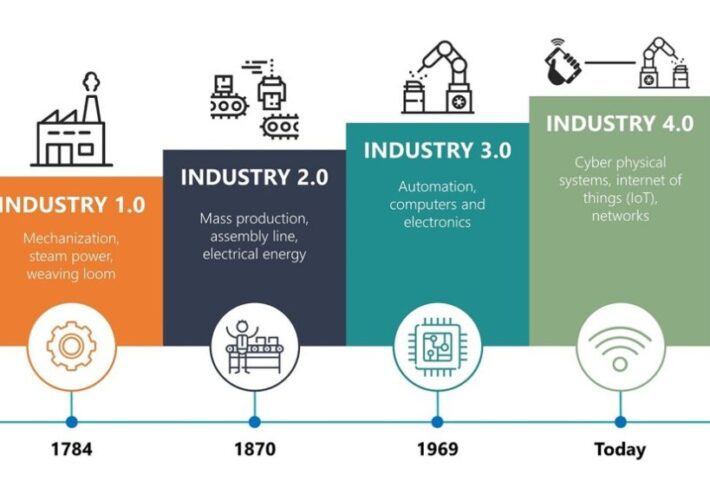
Industry 4.0 vs. Smart Factory: What Will the Future Look Like? It isn’t easy to imagine...
USENIX Security ’22 – ‘Security At The End Of The Tunnel: The Anatomy Of VPN Mental...
The AI Risk Landscape: How ChatGPT Is Shaping the Way Threat Actors Work Flashpoint assesses that...
How to Ensure Your Development Complies With SOC 2 Discover what you need to know from...
Roseville, Calif., CIO Brings Global Background to Local Gov Hong Sae is the CIO for the...
Who Wants to Fuel Independent and High Quality OSINT/Cybercrime and Threat Intelligence Research? Accepting BitCoin Donations...
URGENT ACTION RECOMMENDED – Microsoft Outlook Vulnerability (CVE-2023-23397) Summary: Microsoft disclosed a Microsoft Outlook Vulnerability (an...
COURT DOC: US Federal Agents Arrest Alleged Administrator of Breach Forums “pompompurin” On March 17, 2023,...
What’s New in Cyolo 4.0 2 min read Cyolo 4.0 has officially arrived! Discover all the...
USENIX Security ’22 – Mohsen Minaei, Mainack Mondal, Aniket Kate – ‘Empirical Understanding Of Deletion Privacy:...
USENIX Security ’22 – David G. Balash, Xiaoyuan Wu, Miles Grant, Irwin Reyes, Adam J. Aviv...
No More Missed Opportunities: Maximizing Your Threat Hunting Efforts Threat hunting has become an essential component...







![[New Live Series] Dev Chat with Dan Conn: Beware of Malware](https://ciso2ciso.com/wp-content/uploads/2023/03/blog-ThisweekinMalware-3-100-100-lMAk57-710x500.jpeg)