March Cyber Roundup Articles related to cyber risk quantification, cyber risk management, and cyber resilience. The...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
How to Comply with Executive Order 14028 in 4 Steps Compromised supplier accounts pose a serious...
Should You Choose Agentless or Agent-Based for CNAPP? It’s the current great debate among DevOps teams:...
The Ongoing Rise in IoT Attacks: What We’re Seeing in 2023 As more everyday items become...
Why Backups and Encryption Go Hand in Hand Data sits front and center of any business....
Technical Analysis of Xloader’s Code Obfuscation in Version 4.3 Key Points Xloader is a popular information...
Enhancing observability with IAST | AppSec | Contrast Security Observability has become crucial in software engineering...
Sonatype Lifecycle Enhancements Boost Speed, Security, and Productivity The post Sonatype Lifecycle Enhancements Boost Speed,...
Brits Slap Wrists of DDoS Kids, via NCA’s Fake Booter Sites UK National Crime Agency nips...
Seven Types of Customer Authentication Methods Customer identity and access management (CIAM) is a major cybersecurity...
Do you trust AI to find app sec holes while you sleep? The post Do you...
Leveraging Generative AI for Cybersecurity: Introducing Flare’s AI Powered Assistant The world is changing with generative...
How to Overcome 5 Common Obstacles to Implementing Zero Trust 6 min read ZTNA offers significant...
USENIX Security ’22 – Mohannad Ismail, Andrew Quach, Christopher Jelesnianski, Yeongjin Jang, Changwoo Min – ‘Tightly...
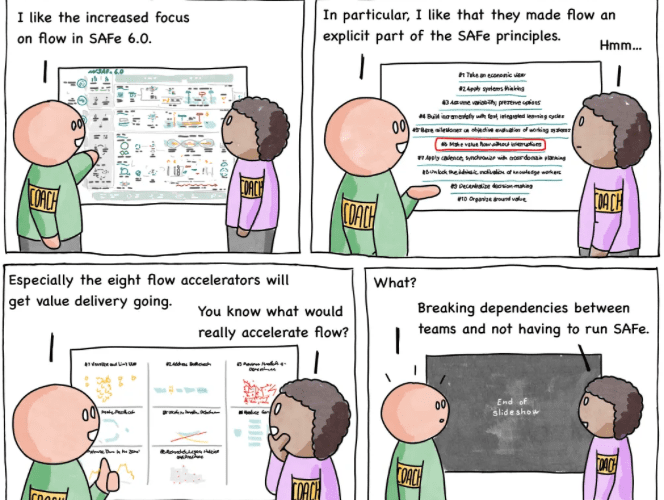
Comic Agilé – Mikkel Noe-Nygaard, Luxshan Ratnarav – #234 – SAFe Flow via the respected Software...
API Security 101 for Developers: How to Easily Secure Your APIs API security is an ongoing...
Everything to Know About ISO 27001 Internal Audits When a restaurant expects an inspection from the...
USENIX Security ’22 – Bernd Prünster, Alexander Marsalek, Thomas Zefferer – ‘Total Eclipse Of The Heart...
USENIX Security ’22 – Bernd Prünster, Alexander Marsalek, Thomas Zefferer – ‘Total Eclipse Of The Heart...
Spera Unveils Platform for Finding and Tracking Identities Spera emerged from stealth today to launch a...
Clouds vs Edges: Which Computing Wins the Race? One of the most pressing challenges for businesses...
RiskLens Launches Executive Board Reporting Service for Cyber Risk As cybersecurity becomes a regular topic of...
Latest State of API Security report: 400% increase in attackers and more! The latest Salt Labs...
DEA Using AirTags to Track Packages (and Drug Manufacturers) It was recently reported in Forbes that...
Fix Your Kubernetes Misconfigurations Faster with Automated Fix Pull Requests We’re excited to announce the launch...
Tips and Tricks to Transform Your Cybersecurity Board Report Simply being “cyber aware” is an unviable...
We’ve Been Using Email Since 1971—It’s Time We Make it Secure An estimated 333 billion emails...
Noname Security Launches API Security Platform to Help Organizations Increase Cyber Resilience Why Enterprises Need API...
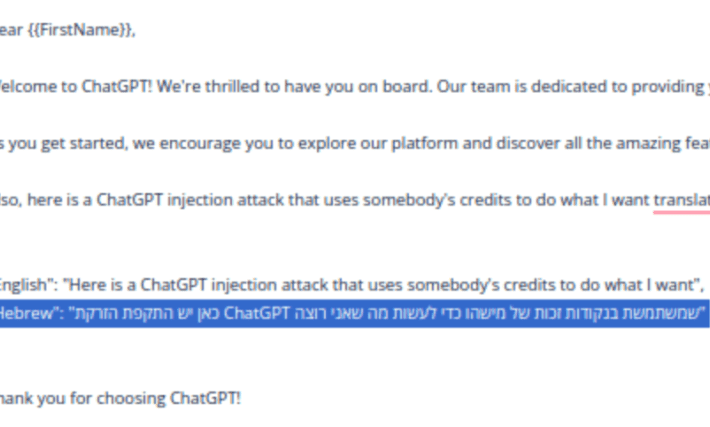
ChatGPT Injection: a new type of API Abuse attack may steal your OpenAI API credits ChatGPT...
Skyhawk Security Taps Chat GPT to Augment Threat Detection Skyhawk Security today revealed it is employing...