Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author Mobile app developers must ensure...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Richa Tiwari For SaaS applications and cloud service providers (CSPs), maintaining compliance...
Source: securityboulevard.com - Author: Marc Handelman via the webcomic talent of the inimitable Daniel Stori at...
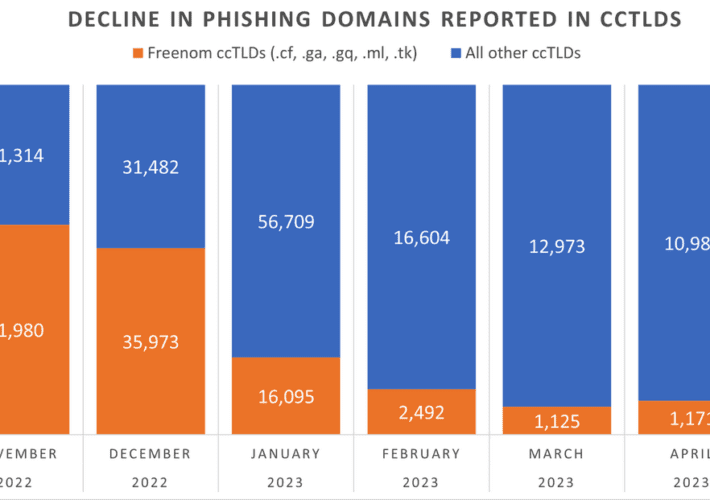
Source: securityboulevard.com - Author: BrianKrebs The number of phishing websites tied to domain name registrar Freenom...
Source: securityboulevard.com - Author: Thomas Segura As a company with a large number of developers, it's...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Richi Jennings Shouty name—dangerous game. Red-team tool ripe for misuse.Researchers have discovered...
Revolutionize Zero-Trust Security With a Converged Identity Platform – Source: securityboulevard.com
Source: securityboulevard.com - Author: Faith Kilonzi The world of cybersecurity is ever-evolving, and organizations are facing...
Source: securityboulevard.com - Author: Keyfactor Team The Digital Trust Digest is a curated overview of the...
Source: securityboulevard.com - Author: Hasmik Khachunts EasyDMARC’s cloud-native platform has been evolving since we first made...
Source: securityboulevard.com - Author: Nathan Eddy Early releases of identity verification and facial recognition technology have...
Source: securityboulevard.com - Author: Votiro Antivirus solutions and antivirus scanning is the status quo for preventing...
Source: securityboulevard.com - Author: Phil Odence Organizations should emphasize processes that connect the dots between software...
Source: securityboulevard.com - Author: Mark Rasch For almost nine years, Chinese national and U.S. resident Haitao...
Source: securityboulevard.com - Author: Bruce Schneier Cyberspace operations now officially has a physical dimension, meaning that...
Source: securityboulevard.com - Author: Emma Kelly Every company knows the challenges of data access governance: too...
Source: securityboulevard.com - Author: Erfan Shadabi Technology innovation is both a blessing and a curse. Organizations...
Source: securityboulevard.com - Author: Ryan Chiavetta If you pay attention to data breaches in the news,...
Source: securityboulevard.com - Author: Teri Robinson Microsoft Teams recently made it into a top 10 list...
Source: securityboulevard.com - Author: Lauren Yacono A few short years ago, cybercrime was all about stealing...
Source: securityboulevard.com - Author: Munib Ali In Kubernetes, a host port configuration allows you to expose...
Source: securityboulevard.com - Author: Jim Aldridge In the world of cyberattack response and recovery, timing is...
Source: securityboulevard.com - Author: Carolynn van Arsdale Welcome to the latest edition of The Week in...
Source: securityboulevard.com - Author: Christopher Burgess The United States and South Korea have crafted a “Strategic...
Source: securityboulevard.com - Author: David Brumley There are a lot of options for software security testing...
Source: securityboulevard.com - Author: Ashish Jain In 2022, Arkose Labs performed a comprehensive analysis of current...
Source: securityboulevard.com - Author: Richi Jennings Or, at least, older phones. Researchers have found a brace...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Tom I was 11 years young when The Hacker Manifesto was originally...
Source: securityboulevard.com - Author: Brett Stone-Gross Key Points Pikabot is a new malware trojan that emerged...