Source: securityboulevard.com - Author: Alison Mack Is Your Organization Cyber Resilient with Adaptable NHIs? Are you...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: FireMon Skybox gibt es nicht mehr, aber Ihre Compliance-Fristen, Audit-Verpflichtungen und Sicherheitsrisiken...
Source: securityboulevard.com - Author: FireMon Die Netzwerksicherheit hat für Unternehmen oberste Priorität, um ihre sensiblen Daten...
Source: securityboulevard.com - Author: FireMon Arrêt de Skybox mais les délais de conformité, les obligations d’audit...
Source: securityboulevard.com - Author: Dancho Danchev Dear blog readers, This is Dancho. I’ve spent the past...
Source: securityboulevard.com - Author: FireMon La sécurité des réseaux est devenue une priorité absolue pour les...
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog In this blog...
Source: securityboulevard.com - Author: FireMon La seguridad de red se ha convertido en una prioridad clave...
Why agent fabrics and registries are central to AI identity security – Source: securityboulevard.com
Source: securityboulevard.com - Author: Eric Olden The age of agentic AI is here — and it’s...
Source: securityboulevard.com - Author: Mike Polatsek Introduction: The AI Cybersecurity Crisis The cybersecurity landscape has fundamentally...
Source: securityboulevard.com - Author: Alison Mack Is Securing Non-Human Identities (NHIs) the Key to User Satisfaction?...
Source: securityboulevard.com - Author: Alison Mack How Can NHI Management Unlock Advanced Security Capabilities? Ever considered...
Source: securityboulevard.com - Author: Alison Mack Will Rising Cybercrimes Warrant a More Innovative Approach to NHI...
Source: securityboulevard.com - Author: Dan Kaplan 1) Token Abuse Token misuse remains one of the most...
Source: securityboulevard.com - Author: Marc Handelman Author/Presenter: Dillon Franke Our sincere appreciation to OffensiveCon by Binary...
Source: securityboulevard.com - Author: Rajan Sodhi Effective digital infrastructure management remains crucial as colocation data centers...
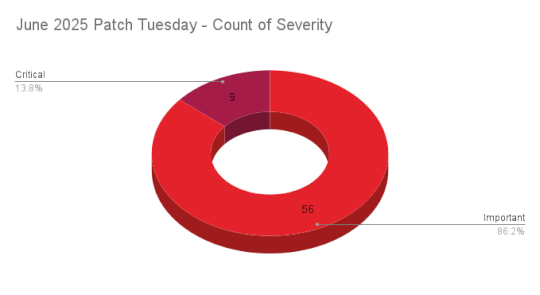
Source: securityboulevard.com - Author: Research Special Operations 9Critical 56Important 0Moderate 0Low Microsoft addresses 65 CVEs, including...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, June 11, 2025 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author The identity industry stands at...
Source: securityboulevard.com - Author: Eric Olden We are entering the age of agentic AI — systems...
Source: securityboulevard.com - Author: Andy Suderman With the rise of AI across every industry, the buzzwords...
Source: securityboulevard.com - Author: Jeffrey Burt The BadBox botnet campaign, which came into the public eye...
Source: securityboulevard.com - Author: Casey Joyce Unauthorized account sharing is a pervasive threat to digital platforms....
Source: securityboulevard.com - Author: Mend.io Communications AI red teaming is the process of simulating adversarial behavior...
Source: securityboulevard.com - Author: Marc Handelman Author/Presenter: Joernchen Our sincere appreciation to OffensiveCon by Binary Gecko,...
Source: securityboulevard.com - Author: hotnops Recently, Microsoft changed the way the Entra Connect Connect Sync agent...
Source: securityboulevard.com - Author: Marc Handelman Tuesday, June 10, 2025 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Lisa Martin At this year’s RSAC Conference, one theme loomed large: AI...
Source: securityboulevard.com - Author: Alison Mack What is the Critical Core of NHI Management? Non-Human Identities...
Source: securityboulevard.com - Author: Alison Mack Can Enhanced NHI Safety Bring You Peace of Mind? The...