Source: securityboulevard.com - Author: Sift Trust and Safety Team As we wrap up the first week...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Mimi Pham Effectively utilizing a risk register allows your organization to anticipate...
Source: securityboulevard.com - Author: Jithin Nair Background: MOVEit is a managed file transfer software produced by...
Source: securityboulevard.com - Author: Marc Handelman Hot Topics Digital Trust & Safety Roundup: New product features,...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author A robust and effective Identity...
Source: securityboulevard.com - Author: Nadav Noy Continuous Integration/Continuous Deployment (CI/CD) pipelines have become crucial to modern...
Source: securityboulevard.com - Author: Michael Vizard Cyera this week revealed it integrated its namesake data security...
Source: securityboulevard.com - Author: David Lindner, Director, Application Security Insight #1 ” Treat AI-generated code as...
Source: securityboulevard.com - Author: Filip Verloy, Noname Security & Graham Rowe, Avord UK Avord, a cybersecurity...
Source: securityboulevard.com - Author: Michael Vizard Sentra this week introduced a tool that automatically redacts personally...
Source: securityboulevard.com - Author: Dwayne McDaniel On June 6, Verizon unveiled its 2023 Data Breach Investigations...
Source: securityboulevard.com - Author: Sara Sokorelis Organizations predominately use centralized identity management systems to regulate how...
Source: securityboulevard.com - Author: Dan Tomaszewski Many managed service providers (MSPs) avoid specializing in several verticals,...
Source: securityboulevard.com - Author: Nathan Eddy The need to secure digital identities is one of the...
Source: securityboulevard.com - Author: GuardRails To successfully implement DevSecOps, IT leaders must effectively communicate its benefits...
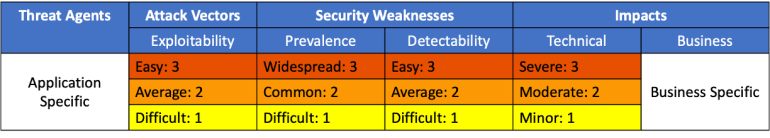
Source: securityboulevard.com - Author: Riddika Grover Let’s unveil the hidden threats to Organizations. In the current...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Marc Handelman Hot Topics Comic Agilé - Mikkel Noe-Nygaard, Luxshan Ratnarav -...
Source: securityboulevard.com - Author: Spanning Cloud Apps Disasters, such as cyberthreats, data loss and downtime, are...
Source: securityboulevard.com - Author: Jenn Jeffers Fraud is a major concern for businesses of all sizes...
Source: securityboulevard.com - Author: Richi Jennings Sextortionists stealing your innocent pictures to make AI nudes.The Federal...
Source: securityboulevard.com - Author: Cyborg Security In the expansive realm of cybersecurity, the nuanced yet intertwined...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Eureka Security Today’s cloud-based environments are complex and consist of various components...
Source: securityboulevard.com - Author: Thomas Stoesser Tech innovation moves pretty fast. But as the landscape continues...
Source: securityboulevard.com - Author: Lauren Yacono Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: wlrmblog As you know by now, the final version of the OWASP...
Source: securityboulevard.com - Author: Mike Spinney Northern Maine Medical Center. Fort Kent, Maine. Fort Kent is...
Source: securityboulevard.com - Author: Kell van Daal Recently PyPI suspended new user sign-ups as well as...