Source: securityboulevard.com - Author: Richi Jennings Warrant not needed if info bought from brokers.An 18-month-old secret...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: HYAS Hackers often spend weeks or months lurking on a target network...
Source: securityboulevard.com - Author: Flashpoint Intel Team June 2023 While most security vendors mainly focus on...
Source: securityboulevard.com - Author: Heidi Anderson Google’s web security service, reCAPTCHA, is seemingly ubiquitous on the...
Source: securityboulevard.com - Author: Michael Vizard Amazon Web Services (AWS) this week added a bevy of...
Source: securityboulevard.com - Author: Kanika Thapar As technology relentlessly progresses, we witness a continuous stream of...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
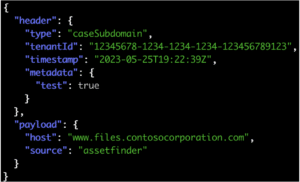
Source: securityboulevard.com - Author: emmaline Overview In a previous article titled Inspector or: How I Learned...
Source: securityboulevard.com - Author: Michael Vizard At the Google Cloud Security Summit, Google today announced that...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Tally Shea Reading Time: 4 minutes Identity management has taken on an...
Source: securityboulevard.com - Author: Gilad Barzilay We have exciting news to share! Salt Security is building...
Source: securityboulevard.com - Author: RiskLens Staff The explosion of artificial intelligence tools has led to massive...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Hyperproof Team Hyperproof integrates with dozens of services across cloud storage, project...
Source: securityboulevard.com - Author: Kaseya In a world where mobile devices reign supreme in the workplace,...
Source: securityboulevard.com - Author: Steve Winterfeld The next time there is a zero-day sweeping the internet,...
Source: securityboulevard.com - Author: scott.fie@sourcedefense.com By Source Defense The theft of payment card data from retail...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: HYPR Team Introduction Nearly every aspect of conducting business today begins with...
Source: securityboulevard.com - Author: Brenda Robb New BlackFog research: 61% of SMBs were victims of a...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Richi Jennings Patching alone won’t cut it.Barracuda Networks is on the hook...
Source: securityboulevard.com - Author: Esther Shein Software supply chain risks is an increasingly hot topic because...
Source: securityboulevard.com - Author: Lucas Seewald Introduction The financial sector, the powerhouse of our economy, is...
Source: securityboulevard.com - Author: Dwayne McDaniel If you have ever heard of Wilmington, North Carolina, it...
Source: securityboulevard.com - Author: Lauren Yacono Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Lohrmann on Cybersecurity For 25 years, cyber policies have evolved and grown...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Ivanwallarm In the digital landscape of 2023, Application Programming Interfaces (APIs) have...