Source: securityboulevard.com - Author: Keyfactor Team Very few events can impact a business on so many...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Natalie Anderson At an event headlined by a roundtable discussion with none...
Source: securityboulevard.com - Author: Jay Roxe, Chief Marketing Officer, HYPR As I was walking around Identiverse...
Source: securityboulevard.com - Author: Harold Byun, Chief Product Officer @ AppOmni As the pioneer in SaaS...
Source: securityboulevard.com - Author: Tamara Bailey, Content Marketing Specialist @ AppOmni SAN FRANCISCO – June 21,...
Source: securityboulevard.com - Author: bacohido Santa Clara, Calif. – June 21, 2023 – Axiad, a leading...
Source: securityboulevard.com - Author: Veronica Haggar DevOps pioneer and author John Willis and cybersecurity leader Shira...
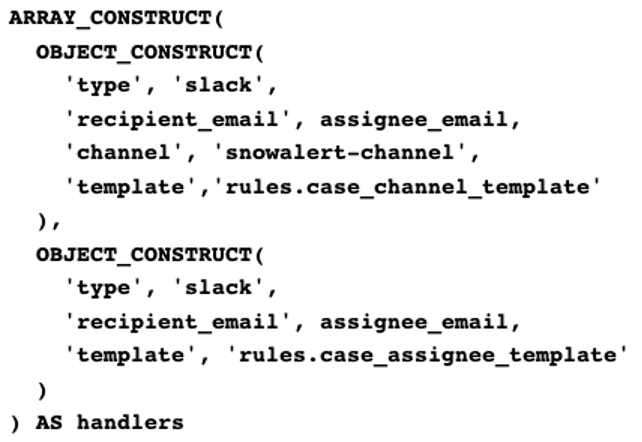
Source: securityboulevard.com - Author: Dwayne McDaniel Richmond, Virginia, has a vibrant and storied history. While Edgar...
Source: securityboulevard.com - Author: Cavelo Blog Data classification is an important part of any cybersecurity program....
Source: securityboulevard.com - Author: Richi Jennings Time and again this month, “Russian” hackers bring down Microsoft...
Source: securityboulevard.com - Author: Abhimanyu Maheswari SMS Fraud: Brace for the Bill Many businesses today underestimate...
Source: securityboulevard.com - Author: Dana Epp Imagine this. You’ve been working on a target for some...
Source: securityboulevard.com - Author: Yiftach Keshet During my time here at Silverfort, I was tasked with...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Cofense Over the past year, the Cofense Intelligence team saw a whopping...
Source: securityboulevard.com - Author: Joel Barbara In early June, the team met in Athens, Greece, for...
Source: securityboulevard.com - Author: Mark Allers In order to understand Next-Gen File Integrity Monitoring (NGFIM), we...
Source: securityboulevard.com - Author: ltabo How to Securely Introduce Explicit AUTHORITY-CHECKS into Custom RFC-Enabled Function Modules...
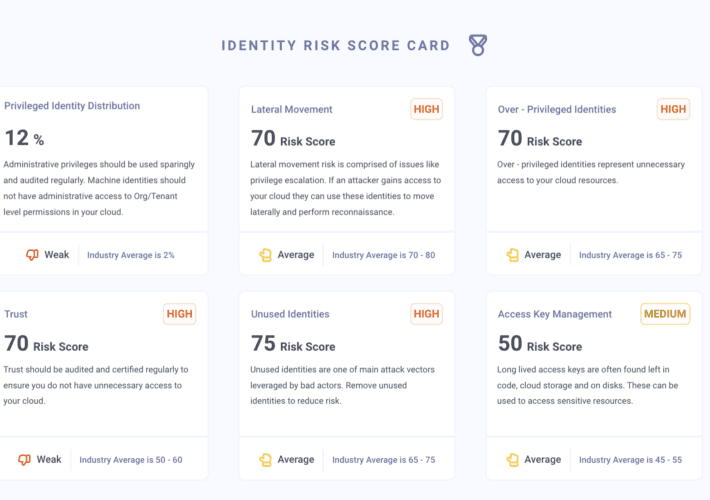
Source: securityboulevard.com - Author: Grip Security Blog A crucial component of protecting your organization, identity access...
Source: securityboulevard.com - Author: Michael Vizard Checkmarx has disclosed how cybercriminals can hijack S3 storage bucket...
Source: securityboulevard.com - Author: Dwayne McDaniel Most folks managing or working within a DevOps organization are...
Source: securityboulevard.com - Author: ninikhew Securing valuable intellectual assets with intellectual property security is an unfortunate...
Source: securityboulevard.com - Author: Richi Jennings John-Oliver-pics protest won’t change Reddit policy, but will ransom demand...
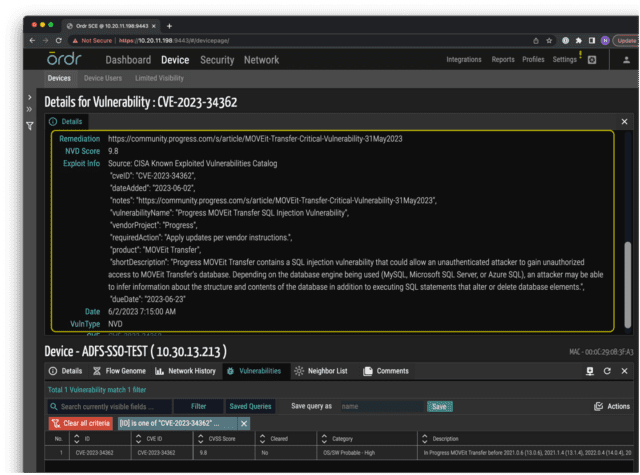
Source: securityboulevard.com - Author: Pandian Gnanaprakasam Coauthors: Srinivas Loke, Gowri Sunder Ravi Progress Software, which makes...
Source: securityboulevard.com - Author: Tally Shea Reading Time: 6 minutes When it comes to insufficient cloud...
Source: securityboulevard.com - Author: John Gary Maynard III If your company uses software under a license...
Source: securityboulevard.com - Author: Teri Robinson Two months after noticing suspicious activity in its systems, PharMerica...
Source: securityboulevard.com - Author: Cyber Risk Quantification Cyber risk quantification (CRQ) can be an invaluable tool....
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: anecdotes Blog How having a Compliance data infrastructure can help scale for...