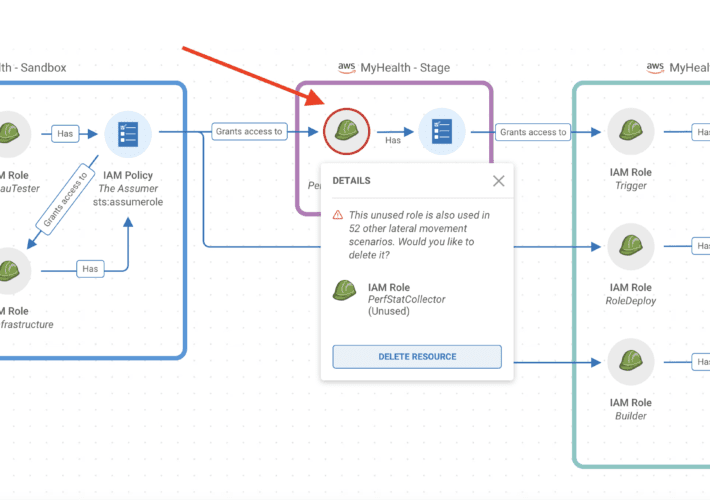
Source: securityboulevard.com - Author: Tally Shea Reading Time: 7 minutes Let’s establish the problem: practitioners are...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Richi Jennings Content warning: Abuse, stalking, controlling behavior.LetMeSpy is a hacking tool...
Source: securityboulevard.com - Author: Marc Handelman Hot Topics Reduce Risk Efficiently & Save Time with Prioritized...
Source: securityboulevard.com - Author: Robert Hilson We don’t like to toot our own horn here at...
Source: securityboulevard.com - Author: Craig Wright Introduction Let me paint a picture for you. You’re on...
Source: securityboulevard.com - Author: Liz Coolman If you are managing development teams using Kubernetes, you need...
Source: securityboulevard.com - Author: Pushpendra Mishra Seceon, the pioneer of the first cybersecurity platform that augments and...
Source: securityboulevard.com - Author: Cavelo Blog As your business becomes increasingly reliant on vendors, suppliers and...
Source: securityboulevard.com - Author: Or Weis Web development has undergone dramatic changes since its inception. However,...
Source: securityboulevard.com - Author: Anudeep Parhar What’s the secret to overcoming common roadblocks when implementing Zero...
Source: securityboulevard.com - Author: Scytale The Essential 8 Maturity Model is quickly rising in rank and...
Source: securityboulevard.com - Author: LeaksID We had a conversation with Sergey Voynov, CEO of G-71, regarding...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Richa Tiwari Whether your org is about to begin its journey for...
Source: securityboulevard.com - Author: Ben Hirschberg We are thrilled to announce that ARMO, the makers of...
Source: securityboulevard.com - Author: Leigh Dow In a world that is more connected than ever, cybersecurity...
Source: securityboulevard.com - Author: emmaline On January 21, 2023 at ShmooCon 2023, Praetorian open-sourced Gato (Github...
Source: securityboulevard.com - Author: Perry Carpenter Cybersecurity and compliance are two of the most daunting aspects...
Source: securityboulevard.com - Author: Lisa Vaas, Senior Content Marketing Manager, Contrast Security Floor & Decor —...
Source: securityboulevard.com - Author: Richi Jennings NYOB accuses TeleSign, Proximus and BICS of misusing phone users’...
Source: securityboulevard.com - Author: Aaron Linskens In today’s fast-paced software development landscape, organizations face rising challenges...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Sushant Rao, SVP of Marketing Data masking and data encryption are two...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Michael Vizard Tines has added a case management tool to its no-code...
Source: securityboulevard.com - Author: Guest Post Almost every website, app, and user platform now requires usernames...
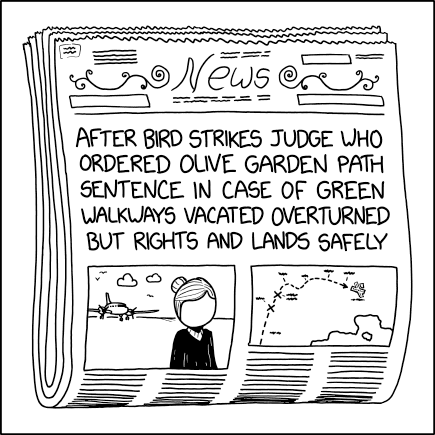
Source: securityboulevard.com - Author: John Gary Maynard III In a typical software piracy case, a software...
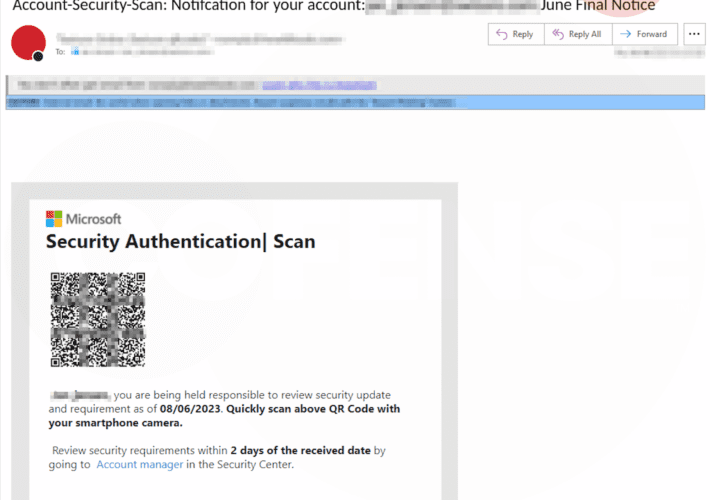
Source: securityboulevard.com - Author: Cofense Author: Kian Buckley Maher SEG Bypassed: Microsoft The Cofense Phishing Defense Center (PDC)...
Source: securityboulevard.com - Author: ZeroFox Team Today’s interconnected digital landscape has enabled organizations to unlock new...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...