Source: securityboulevard.com - Author: Neko Papez It’s hard to imagine a time when the web browser...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Sue Poremba Is there a more talked about topic than AI right...
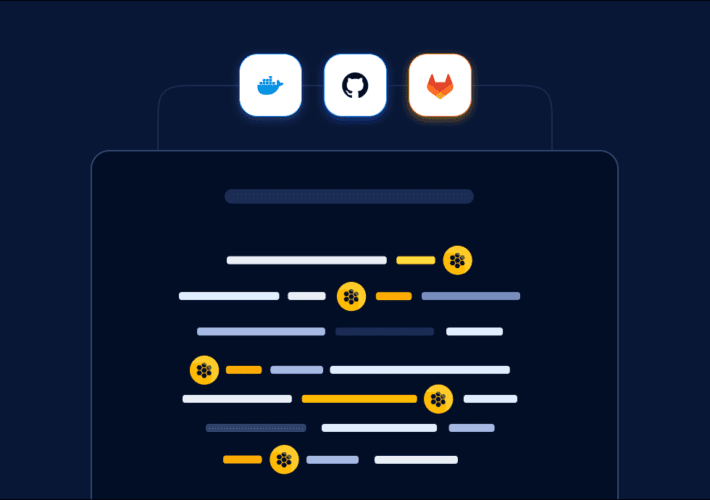
Source: securityboulevard.com - Author: Lucija Valentić Executive Summary ReversingLabs researchers recently discovered more than a dozen...
Source: securityboulevard.com - Author: Michelle Ofir Geveye The goal of audit testing procedures in financial reporting...
Source: securityboulevard.com - Author: Marc Handelman Hot Topics Comic Agilé - Mikkel Noe-Nygaard, Luxshan Ratnarav -...
Source: securityboulevard.com - Author: Guest Expert Sponsorships Available Keshav Malik Keshav is a full-time Security Engineer...
Source: securityboulevard.com - Author: Richi Jennings Or just get it off the internet, stat.Fortinet FortiOS security...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Richi Jennings MITRE has published this year’s list of vulnerability categories. The list...
Source: securityboulevard.com - Author: Ray Overby Data breaches have reached record highs in recent years. In...
Source: securityboulevard.com - Author: Jacqueline Lebo The Russian-speaking CL0P ransomware gang is on a tear exploiting...
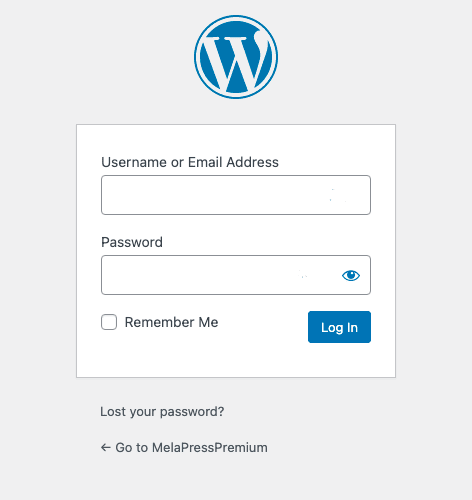
Source: securityboulevard.com - Author: Joel Barbara Changing the WordPress login URL is a security practice recommended...
Source: securityboulevard.com - Author: John Gary Maynard III Many commercial disputes are launched with a demand...
Source: securityboulevard.com - Author: Merton Notrem, Compliance Success Manager, Scytale We get it – just when...
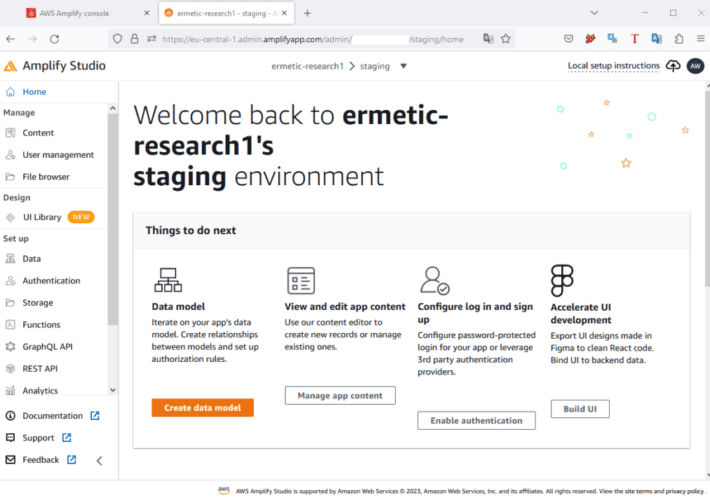
Source: securityboulevard.com - Author: Ermetic Team Ermetic researchers recently discovered a specific combination of AWS service...
Source: securityboulevard.com - Author: Khushboo Chahal Introduction Organizations across industries face a common challenge – the...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
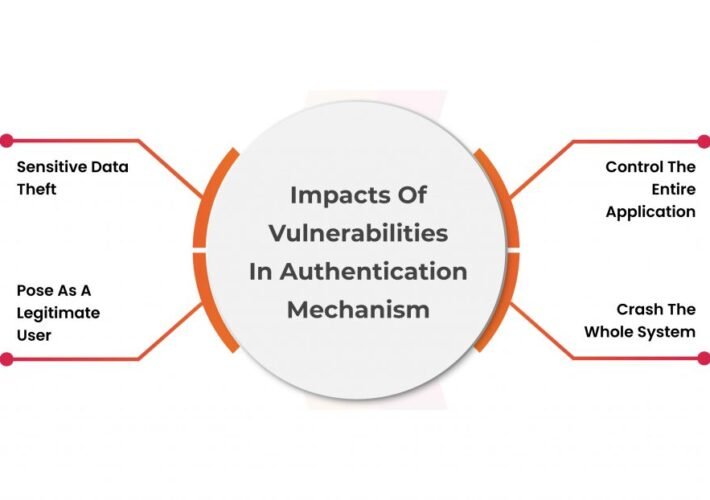
Source: securityboulevard.com - Author: Riddika Grover Authentication bypass vulnerability is a security defect that enables a...
Source: securityboulevard.com - Author: Prayukth K V Looking ahead of CEA guidelines to secure the power...
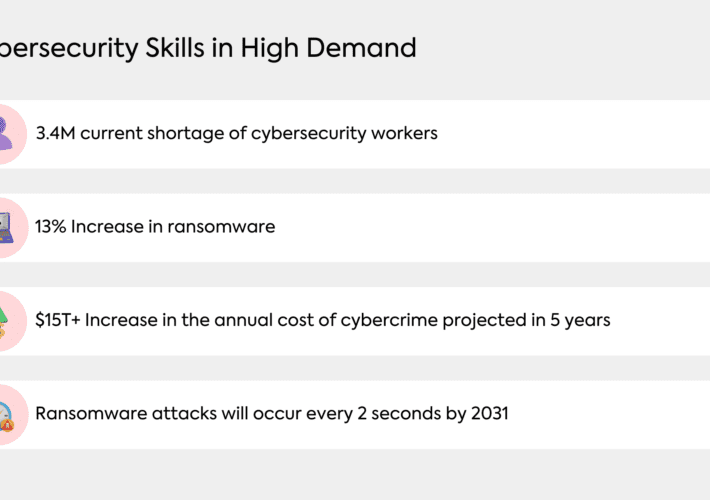
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author The digital age has transformed...
Source: securityboulevard.com - Author: ReasonLabs Your social security number (SSN) is one of the most crucial...
Source: securityboulevard.com - Author: Spanning Cloud Apps Due to the increased shift to a hybrid business model...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Patrice Boffa A Testament to Our Customer Success Team’s Dedication We are...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: BrianKrebs If you’ve ever owned a domain name, the chances are good...
Source: securityboulevard.com - Author: SSLWiki Chrome’s “Padlock Icon” is to be replaced by “Tune Icon” in...
Source: securityboulevard.com - Author: Michelle Ofir Geveye What is Vulnerability Management? Vulnerability management is a critical...
Source: securityboulevard.com - Author: Bruce Schneier Police are already using self-driving car footage as video evidence:...
Source: securityboulevard.com - Author: Tom Eston Several major organizations, including British Airways and the BBC, fell...














![BSidesSF 2023 – Nika Korchok Wakulich – MTV Reboot — My Super Sweet 16-Bit Malware ~ *MS-DOS Edition* ~ [TSR Remix] – Source: securityboulevard.com](https://ciso2ciso.com/wp-content/uploads/2023/07/67876/bsidessf-2023-nika-korchok-wakulich-mtv-reboot-my-super-sweet-16-bit-malware-ms-dos-edition-tsr-remix-source-securityboulevard-com-710x500.jpg)