Source: securityboulevard.com - Author: Deborah Erlanger What is the EU AI Act? The EU AI Act...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Alison Mack How Can NHIs Serve as the Crucial Backbone in Overall...
Source: securityboulevard.com - Author: Alison Mack Is Proactive NHI Management Our Best Bet Against Cyber Threats?...
Source: securityboulevard.com - Author: Alison Mack Why Is Secrets Management Crucial for Your Cloud Environment? Do...
Source: securityboulevard.com - Author: Alison Mack Why are Machine Identities Crucial to Cybersecurity Strategies? How often...
Source: securityboulevard.com - Author: Audian Paxson Let’s talk about the real story behind Google’s DMARC maze,...
Source: securityboulevard.com - Author: Marc Handelman Author/Presenter: Carl Richell (CEO and Founder, System76, Inc.) Our sincere...
Source: securityboulevard.com - Author: Rajveer Singh Introduction Keeping your applications secure while offering a smooth user...
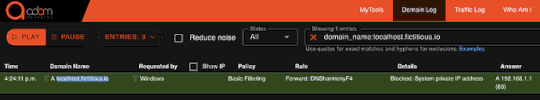
Source: securityboulevard.com - Author: David After this week’s attention to META and Yandex localhost abuses, it...
Source: securityboulevard.com - Author: cybernewswire Paris, Jun. 3, 2025, CyberNewswire–Arsen, the cybersecurity startup known for defending...
Source: securityboulevard.com - Author: Marc Handelman Author/Presenter: Nikolay Sivko (Co-Founder And CEO At Coroot) Our sincere...
Source: securityboulevard.com - Author: Mend.io Team What is Shadow AI? Shadow AI refers to the unauthorized...
Source: securityboulevard.com - Author: Richi Jennings Pundits accuse Zuckerberg’s latest app of having a “dark pattern,”...
Source: securityboulevard.com - Author: Vy Chen A Wake-Up Call for HR in the Age of Deepfakes...
Zero-Click Flaw in Microsoft Copilot Illustrates AI Agent, RAG Risks – Source: securityboulevard.com
Source: securityboulevard.com - Author: Jeffrey Burt A critical vulnerability found in Microsoft’s Copilot puts a focus...
Source: securityboulevard.com - Author: Mary Henry Kubernetes is powerful, but managing it in-house can be a...
Source: securityboulevard.com - Author: Marc Handelman Author/Presenter: Sam Groveman (Research Associate) Our sincere appreciation to LinuxFest...
Source: securityboulevard.com - Author: Eric Olden Let’s break down how identity must evolve across the key...
Source: securityboulevard.com - Author: Michael Lyborg How to Develop a Cybersecurity Strategy in 7 Steps Developing...
Source: securityboulevard.com - Author: Alison Mack Is Assured Compliance Your Ultimate Goal? Consider Effective NHI Management...
Source: securityboulevard.com - Author: Alison Mack Does Non-Human Identity Management Hold the Key to Effective Cybersecurity?...
Source: securityboulevard.com - Author: Marc Handelman Author/Presenter: Jon “maddog” Hall (Board Chair Emeritus: Linux Professional Institute,...
Source: securityboulevard.com - Author: Eric Olden As enterprises embrace AI agents to automate decisions and actions...
Source: securityboulevard.com - Author: Francis Guibernau On December 18, 2023, the Cybersecurity and Infrastructure Security Agency...
Source: securityboulevard.com - Author: Krupa Patil Recently, Google announced that starting August 1, 2025, the Google...
Source: securityboulevard.com - Author: Contrast Marketing If your tools can’t see what’s happening inside your apps...
Source: securityboulevard.com - Author: Marc Handelman Friday, June 13, 2025 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Mudra Goyal The Legacy Security Dilemma: Essential, Irreplaceable — and Exposed Despite...
Source: securityboulevard.com - Author: FireMon Skybox non c’è più, ma le scadenze di conformità, gli obblighi...
I pericoli della gestione fai-da-te dei criteri di sicurezza di rete – Source: securityboulevard.com
Source: securityboulevard.com - Author: FireMon La sicurezza della rete è diventata una priorità assoluta per le...