Source: securityboulevard.com - Author: BrianKrebs The Russian government today handed down a treason conviction and 14-year...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Cyborg Security Threat Overview – CVE-2023-36884 CVE-2023-36884 is a newly discovered critical...
Source: securityboulevard.com - Author: Tom Dixon Unleashing Intelligence: Transforming NetFlow and Flow Log Data into Actionable...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Richi Jennings Thinly veiled attempt to track you and make more ad...
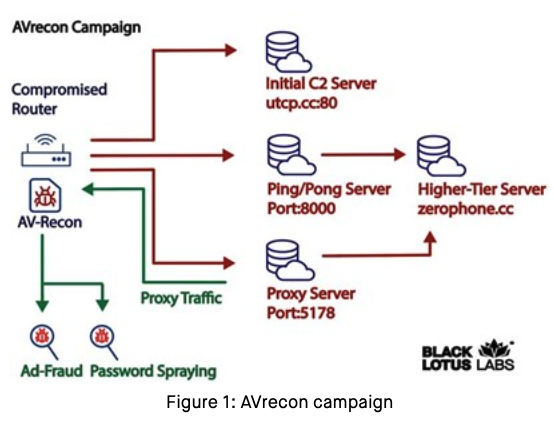
Source: securityboulevard.com - Author: BrianKrebs Researchers this month uncovered a two-year-old Linux-based remote access trojan dubbed...
Source: securityboulevard.com - Author: Jeffrey Burt Less than two weeks after WormGPT hit the scene as...
Source: securityboulevard.com - Author: Charlotte Freeman Hot Topics Who and What is Behind the Malware Proxy...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Natalie Anderson Picture this: your company falls victim to a cyber-attack, resulting...
Source: securityboulevard.com - Author: SafeBreach Cybersecurity programs have shifted from building impenetrable fortresses to protect networks...
Source: securityboulevard.com - Author: Michael Vizard Netskope today published a report that finds source code is...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Heidi Anderson How to Choose the Best CAPTCHA Software With one out...
Source: securityboulevard.com - Author: Jeffrey Burt The average cost to an organization hit with a data...
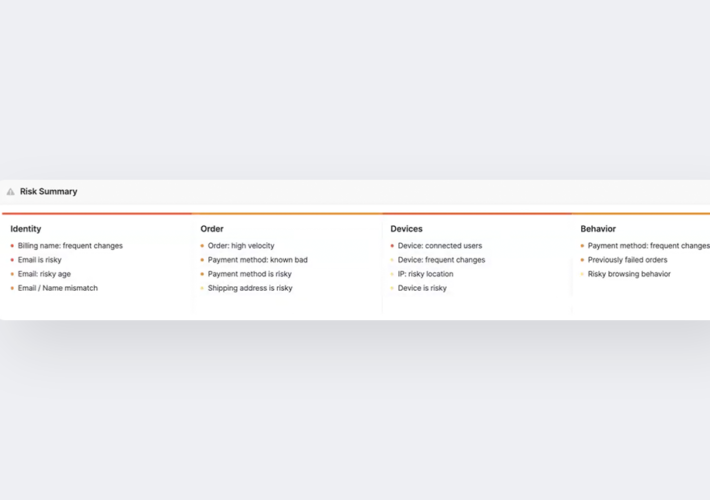
Source: securityboulevard.com - Author: Coby Montoya Machine learning-based fraud decision engines are sometimes viewed as mysterious...
Source: securityboulevard.com - Author: Jeffrey Burt Google is rolling out a red team charged with testing...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Mackenzie Jackson In GitGuardian's first digital conference, CodeSecDays, security leaders from multiple...
Source: securityboulevard.com - Author: Ericka Chickowski As artificial intelligence (AI) captivates the hearts and minds of...
Source: securityboulevard.com - Author: Patrick Bedwell Netography Fusion Enhancements Give SOC, NOC, and AIOps Teams Faster...
Source: securityboulevard.com - Author: Richi Jennings Satya and Pooh, Sitting in a Tree, K.I.S.S.I.N.G.The nasty hack...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Josh Smith, Strategic Alliance Manager @ AppOmni Five Critical Steps to Securing...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Lohrmann on Cybersecurity Maine paused the use of ChatGPT and other generative...
Source: securityboulevard.com - Author: Matt Palmer Last week I spoke for Jersey Cyber Security Centre (...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Avoid The Hack! Waterfox came into the browser scene in 2011, coming...
Source: securityboulevard.com - Author: wlrmblog In early June 2023, OWASP released the final version of the...