Source: securityboulevard.com - Author: Assura Team Ever wondered how safe your digital life really is? Prepare...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Lohrmann on Cybersecurity If you are looking for a deep-dive strategy book...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
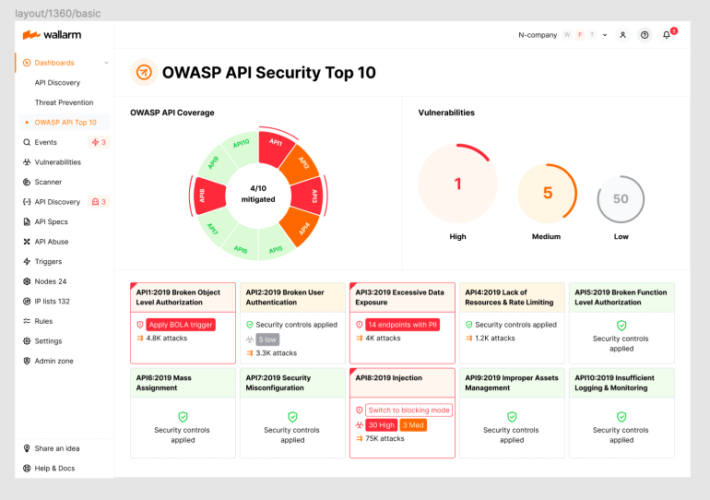
Source: securityboulevard.com - Author: wlrmblog Welcome to the 2nd post in our weekly series on the...
Source: securityboulevard.com - Author: Keon Ramzani In the last several years, consumer identity protection offers have...
Source: securityboulevard.com - Author: Rajan Sodhi Data center infrastructure management (DCIM) is the process of monitoring,...
Source: securityboulevard.com - Author: Jeffrey Burt Threat actors are using bogus advertisements for IT tools on...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Tejas Ranade GRC programs are often viewed as cost centers. But, they...
Source: securityboulevard.com - Author: Cameron Delfin In an increasingly digitalized world, the significance of cybersecurity cannot...
Source: securityboulevard.com - Author: Jeffrey Burt US Senator Ron Wyden (D-OR) is asking government enforcement agencies...
Android Foils AirTag Stalkers and Thieves — While Apple Does Nothing – Source: securityboulevard.com
Source: securityboulevard.com - Author: Richi Jennings “Unknown Tracker Detected,” your phone screams. What now?An Apple AirTag that’s...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: David Lindner, Director, Application Security Insight #1 A recent report by Cohesity...
Source: securityboulevard.com - Author: Avast Blog Summer is at its height, and it’s a good time...
Source: securityboulevard.com - Author: Votiro Team Organizations often confuse the concept of being compliant with being...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Martin Roesch Netography: Getting Beyond the ‘Black Box’ Approach to DDoS By...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Sift Trust and Safety Team In the six months since ChatGPT launched...
Source: securityboulevard.com - Author: Paul Roberts Two weeks after the IT management firm JumpCloud announced that...
Source: securityboulevard.com - Author: Arkose Labs Fraud is a pervasive threat to any organization’s viability and...
Source: securityboulevard.com - Author: Chris Garland Every year, Congress passes the National Defense Authorization Act (NDAA),...
Source: securityboulevard.com - Author: Kate Tenerowicz Welcome to the latest edition of The Week in Security,...
Source: securityboulevard.com - Author: Jane Lee TrustCon is THE place to be for trust and safety...
Source: securityboulevard.com - Author: Ethan Bresnahan On July 26, the Securities and Exchange Commission voted to...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Jeffrey Burt The massive box office brought in by the “Barbie” movie...
Source: securityboulevard.com - Author: Paul Asadoorian Whether you are new to Linux or a seasoned Linux...