Source: securityboulevard.com - Author: Siddharth Deb Airlines and travel industry operators, badly impacted during the Covid...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Sift Trust and Safety Team Account takeover attacks are one of the...
Source: securityboulevard.com - Author: Michael Vizard An analysis of cyberattack patterns published by Cado Security, a...
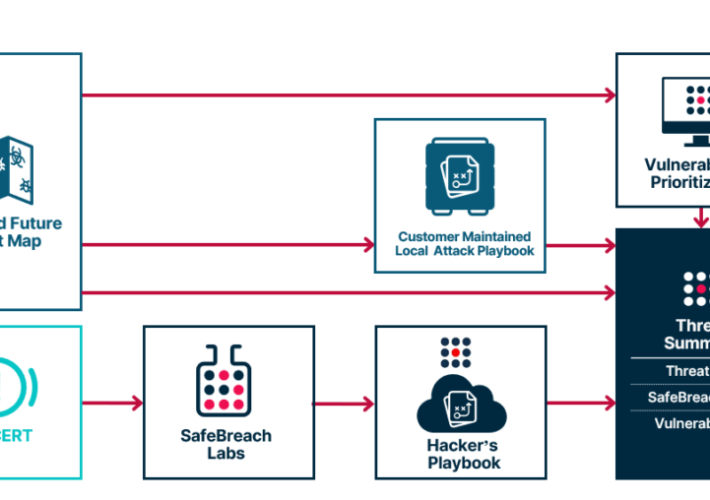
Source: securityboulevard.com - Author: SafeBreach Modern enterprises have adopted more offensive measures to protect their organizations...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
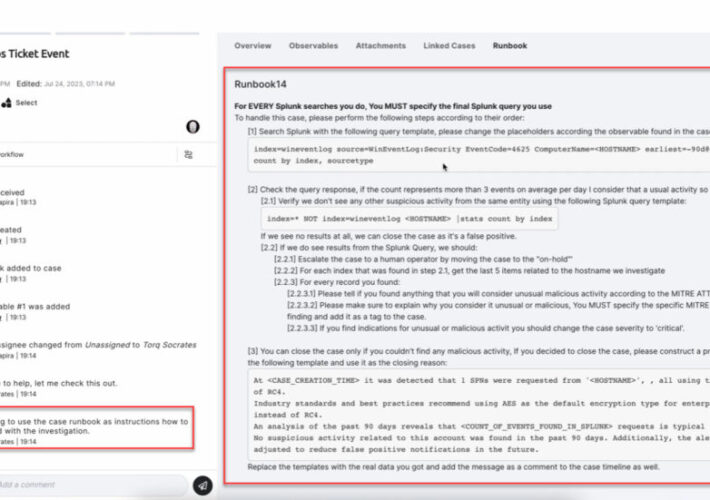
Source: securityboulevard.com - Author: Michael Vizard Torq today announced it is injecting additional generative artificial intelligence...
Source: securityboulevard.com - Author: Kimberly Rose Every decision and action that affects your business is only...
Source: securityboulevard.com - Author: Will Schroeder In our previous post, we talked about the problem of...
Source: securityboulevard.com - Author: Richi Jennings Dark web AI models that can phish and write malware...
Source: securityboulevard.com - Author: Erin Crapser TrustCloud is thrilled to announce a partnership with VanRein Compliance,...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, August 2, 2023 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Jeffrey Burt There are a number of components that make up a...
Source: securityboulevard.com - Author: Michael Vizard Balbix today added a tool that makes it simpler for...
Source: securityboulevard.com - Author: LimaCharlie's Blog Recon Infosec is a growing managed security services provider run...
Source: securityboulevard.com - Author: Votiro Have you ever considered the risk of potential hidden threats while...
Source: securityboulevard.com - Author: Bill Graham On July 12, 2023, the White House issued an implementation...
Source: securityboulevard.com - Author: bacohido Cambridge, Mass. – Aug. 1, 2023 – Devo Technology, the cloud-native security...
Source: securityboulevard.com - Author: Michael Vizard A study published today found 79% of certificates on the...
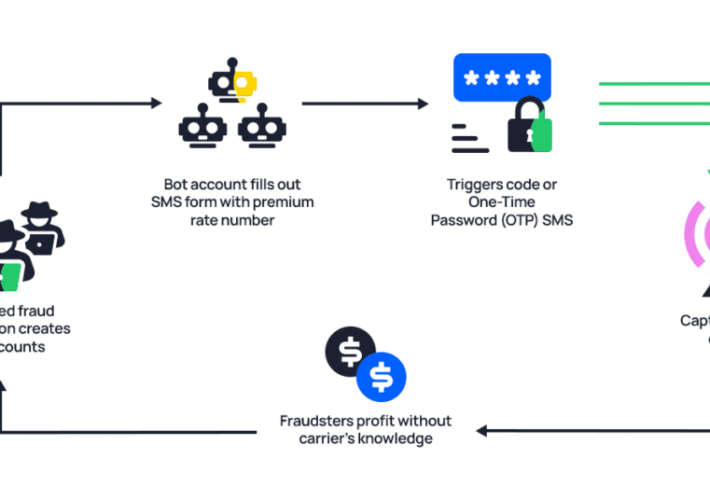
Source: securityboulevard.com - Author: Jenn Jeffers Human-Assisted CAPTCHA-Cracking Now at Play in Bot Attacks Human solvers...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Kayne McGladrey Big news: after over a year of delays, the SEC...
Source: securityboulevard.com - Author: Michael Vizard ARIA Cybersecurity Solutions, an arm of CSPi, has launched a...
Source: securityboulevard.com - Author: Jason Kent The Australian Signals Directorate’s Australian Cyber Security Centre (ACSC), U.S....
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Peter Klimek One of the most promising developments in the fight against...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Esther Shein Premier cybersecurity conference Black Hat USA 2023 is coming up...
Source: securityboulevard.com - Author: Natalie Anderson Monthly Release Notes for July Looking to learn about Apptega’s...
Source: securityboulevard.com - Author: Alexa Bleecker SMS has become a popular channel to engage customers, verify...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...