Source: securityboulevard.com - Author: Jeffrey Burt The government of Iran appears to have severely restricted internet...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Marc Handelman Author/Presenter: Oscar Baechler, MA (Author @ Packt Publishing, Professor, Lake...
Source: securityboulevard.com - Author: Eric Olden Why OAuth Is Ideal for Agentic Identity Today—and How Maverics...
Source: securityboulevard.com - Author: Eric Olden AI agents aren’t theoretical anymore. They’re active in our enterprises—making...
Source: securityboulevard.com - Author: bacohido By Byron V. Acohido Last week at Microsoft Build, Azure CTO...
Why a Layered Approach Is Essential for Cybersecurity and Zero Trust – Source: securityboulevard.com
Source: securityboulevard.com - Author: Peter Senescu Today’s cybersecurity landscape is complex and unforgiving. Remote work, Saas,...
Source: securityboulevard.com - Author: Alison Mack Are You Leveraging NHIDR Capabilities for Advanced Cybersecurity? Managing Non-Human...
Source: securityboulevard.com - Author: Alison Mack Are Your Cloud Secrets as Secure as They Could Be?...
Source: securityboulevard.com - Author: Alison Mack How Secure is Your Cloud-Native Security? We can’t ignore the...
Source: securityboulevard.com - Author: Carole Winqwist GitGuardian announces a strategic partnership with GuidePoint Security to deliver...
Source: securityboulevard.com - Author: Marc Handelman Author/Presenter: Mariatta Wijaya (Python Core Developer) Our sincere appreciation to...
Source: securityboulevard.com - Author: Matthew Rosenquist The cybersecurity industry moves fast! The attackers are constantly adapting...
Source: securityboulevard.com - Author: Jeffrey Burt U.S. prosecutors want to take $7.74 million seized during an...
Source: securityboulevard.com - Author: ColorTokens Editorial Team Healthcare is in the midst of a technology-driven revolution....
Source: securityboulevard.com - Author: Rajan Sodhi When it comes to managing a data center’s infrastructure, the...
Source: securityboulevard.com - Author: Anton Chuvakin Output-driven SIEM — 13 years later Output-driven SIEM! Apart from EDR and SOC...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Sen Hastings (Software Dev And SBC Enthusiast) Our sincere...
Source: securityboulevard.com - Author: Dev Kumar Imagine you’re building a sophisticated apartment complex that needs to...
Source: securityboulevard.com - Author: Marc Handelman Tuesday, June 17, 2025 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: José Ibañez (CEO at Blind Penguin), Raissa Ibañez (Manager...
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author Here's the brutal truth: 90%...
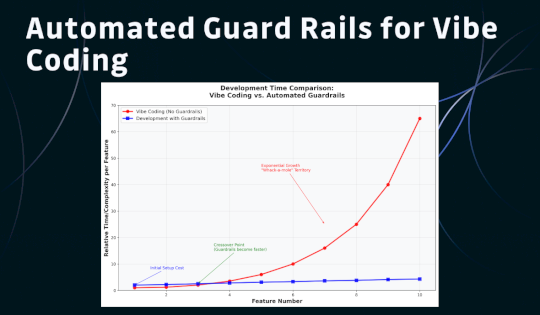
Source: securityboulevard.com - Author: Andy Rea There are countless warnings and horror stories about "vibe coding"—that...
Source: securityboulevard.com - Author: Alex Vakulov Mobile devices are now the primary gateway to the digital...
Source: securityboulevard.com - Author: Jeffrey Burt Several journalists with The Washington Post were targeted in a...
Source: securityboulevard.com - Author: Alison Mack Why is Advanced NHI Management Crucial for Driving Innovation? Where...
Source: securityboulevard.com - Author: Alison Mack Why is NHI Management Crucial for Growing Businesses? Growing businesses...
Source: securityboulevard.com - Author: Alison Mack Why does Digital Identity Control Matter in Cybersecurity? Do you...
Source: securityboulevard.com - Author: Matt Palmer Since 2021, I’ve been building Jersey Cyber Security Centre (JCSC)....
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Steven Shiau (Clonezilla Project Leader); Yu-Chin Tsai (Clonezilla NCHC...
Source: securityboulevard.com - Author: Lohrmann on Cybersecurity Lohrmann on Cybersecurity From vibe hacking to malware development...