Source: securityboulevard.com - Author: BrianKrebs In large metropolitan areas, tourists are often easy to spot because...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Ben Hirschberg Kubernetes has become the de facto platform for orchestrating containerized...
Source: securityboulevard.com - Author: Matt Weir “Tools?” scoffed Kalisti, “Tools are for people who have nothing...
Source: securityboulevard.com - Author: Team Nuspire Security teams continue to rely on the Common Vulnerability Scoring...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: bacohido Boston, Mass, Aug. 22, 2023 – airSlate, a leader in document workflow automation...
Source: securityboulevard.com - Author: Jeffrey Burt The person responsible for developing the dangerous CraxsRAT malware that...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: bacohido Phone number spoofing involves manipulating caller ID displays to mimic legitimate...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Jeffrey Burt The high-profile Cuba ransomware group is abusing a security flaw...
Source: securityboulevard.com - Author: Richi Jennings Fix for CVE-2023-40477 now available.Good old WinRAR has a serious...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Lohrmann on Cybersecurity Surveys show that most Americans think online security is...
Source: securityboulevard.com - Author: Matt Weir This year I didn’t compete in the Defcon Crack Me...
Source: securityboulevard.com - Author: Smit Kadakia RMM tools are the easy targets for cyber attackers, and...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
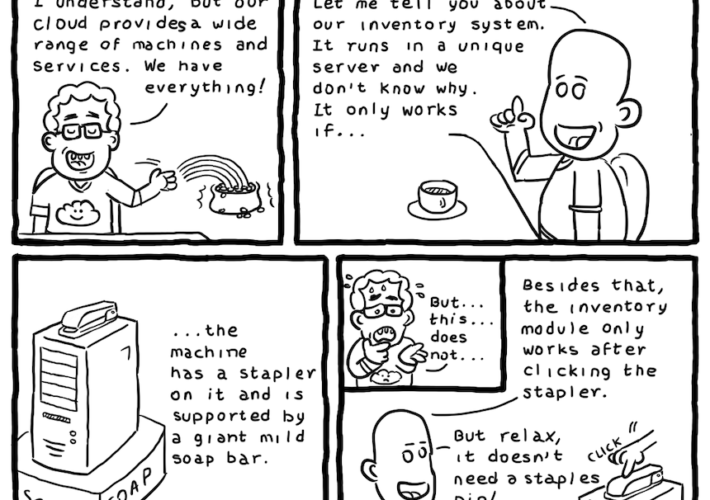
Source: securityboulevard.com - Author: wlrmblog Welcome to the 5th post in our weekly series on the...
Source: securityboulevard.com - Author: Shelley Leveson, Director of Content Marketing, HYPR The Payment Card Industry Security...
Source: securityboulevard.com - Author: Team Solvo In today’s rapidly evolving digital landscape, where businesses are increasingly...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Yuzuka Akasaka The risk of cyber threats has become an everyday reality...
Source: securityboulevard.com - Author: Michael Vizard IBM has extended its alliance with Cloudflare to employ machine...
Source: securityboulevard.com - Author: Jeffrey Burt The Play ransomware operators who took credit for the attack...
Source: securityboulevard.com - Author: Danielle Cook With KubeCon approaching fast (yes, November will be here before...
Source: securityboulevard.com - Author: Laura Case, Director of Product Management The acceleration of AI, machine learning,...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: wlrmblog We recently hosted a compact and very engaging panel discussion about...
Source: securityboulevard.com - Author: Kathryn Schneider The internet is abuzz with talk of the potential of...