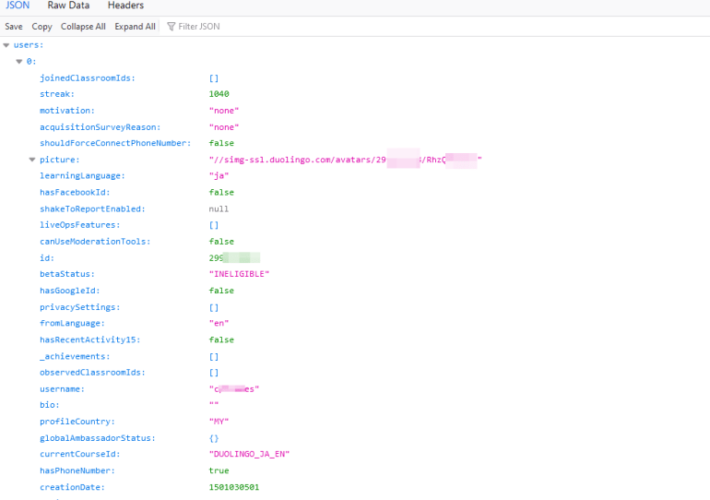
Source: securityboulevard.com - Author: Tim Erlin It’s been reported that 2.6 million user records sourced from...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
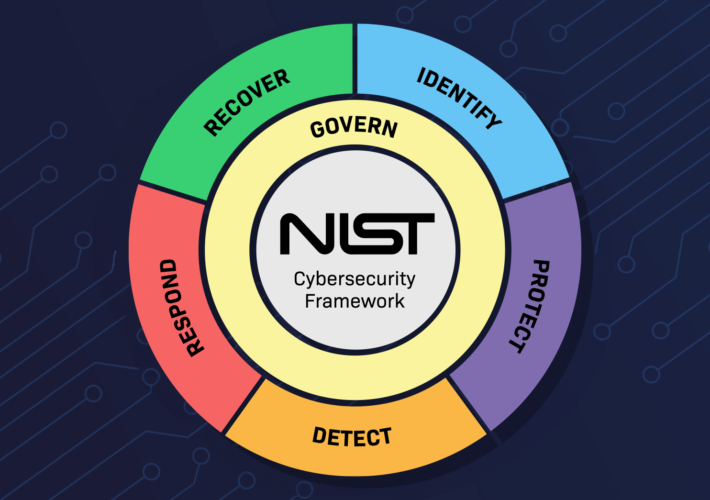
Source: securityboulevard.com - Author: Chris Griffith NIST CSF 1.1 to 2.0 is a significant update reflecting...
Source: securityboulevard.com - Author: Michael Vizard Versa Networks this week revealed it has extended its secure...
Source: securityboulevard.com - Author: Jeffrey Burt Bad actors are using a full-featured phishing toolkit to target...
Source: securityboulevard.com - Author: David Lindner, Director, Application Security Yes, we have specific objectives for uptime...
Source: securityboulevard.com - Author: Marc Handelman Yes, we have specific objectives for uptime and recovery Yes,...
Source: securityboulevard.com - Author: Avast Blog Yes, we have specific objectives for uptime and recovery Yes,...
Source: securityboulevard.com - Author: Jason Kent Attending many of the HackerSummerCamp activities involves attending a bunch...
Source: securityboulevard.com - Author: SafeBreach Research shows many companies now own and operate more than 60...
Source: securityboulevard.com - Author: Marc Handelman Yes, we have specific objectives for uptime and recovery Yes,...
Source: securityboulevard.com - Author: Deepfactor Deepfactor Release 3.3 Overview In Release 3.3 of Deepfactor Developer Security,...
Source: securityboulevard.com - Author: Team Nuspire Nuspire’s latest threat report, which analyzes threat data from Q2...
Source: securityboulevard.com - Author: Richi Jennings Arion Kurtaj and anon minor: Part of group that hacked...
Source: securityboulevard.com - Author: Marc Handelman Yes, we have specific objectives for uptime and recovery Yes,...
Source: securityboulevard.com - Author: Joel Wong The cybersecurity industry is riddled with challenges like how to...
Source: securityboulevard.com - Author: Jeffrey Burt The U.S. government is taking a big swing at two...
Source: securityboulevard.com - Author: Jeffrey Burt Software-as-a-service (SaaS) applications have become foundational to enterprises that use...
Source: securityboulevard.com - Author: John Phantis Since its beginning, ForgeRock has been focused on enabling people...
Source: securityboulevard.com - Author: Marc Handelman Yes, we have specific objectives for uptime and recovery Yes,...
Source: securityboulevard.com - Author: Mike Larkin Another August, another Hacker Summer Camp. The annual gathering of...
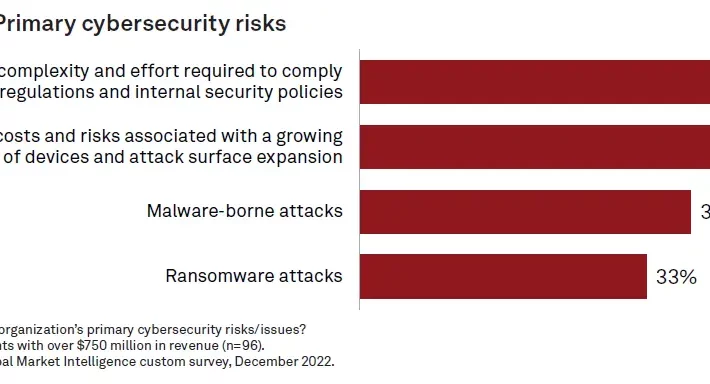
Source: securityboulevard.com - Author: Jeffrey Burt Enterprise security teams are having problems keeping pace with the...
Source: securityboulevard.com - Author: HYAS HYAS Chief Commercial Officer (CCO), Mike Barker, has a broad and...
Source: securityboulevard.com - Author: Aleksander W. Jarosz Multiple New Campaigns in 2023 Demonstrate The Malware Family...
Source: securityboulevard.com - Author: Marc Handelman Yes, we have specific objectives for uptime and recovery Yes,...
Source: securityboulevard.com - Author: Michael Vizard HP Inc. today published a report detailing how the tactics...
Source: securityboulevard.com - Author: HYPR Team Authentication security remains a significant vulnerability in most organizations’ security...
Source: securityboulevard.com - Author: Chris Garland Yes, we have specific objectives for uptime and recovery Yes,...
Source: securityboulevard.com - Author: Avast Blog If you’re anything like me, every few days you look...
Source: securityboulevard.com - Author: Marc Handelman Yes, we have specific objectives for uptime and recovery Yes,...
Source: securityboulevard.com - Author: Rajan Sodhi Product Update: Version 4.0 As we enter the new era...