Source: securityboulevard.com - Author: Natalie Anderson Economic downturns often trigger cost-cutting and layoffs. And while it...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Avast Blog It’s a landmark shift when our children leave the house...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: BrianKrebs The U.S. government today announced a coordinated crackdown against QakBot, a...
Source: securityboulevard.com - Author: Riley-Ann Parker LogRhythm SIEM combined with CimTrak provides the ability to immediately...
Source: securityboulevard.com - Author: Arkose Labs SMS toll fraud is putting a severe financial burden on...
The Evolution of NDP: Finding Our Fit in the Technological Landscape – Source: securityboulevard.com
Source: securityboulevard.com - Author: Barrett Lyon The Evolution of NDP: Finding Our Fit in the Technological...
Source: securityboulevard.com - Author: Marc Handelman Yes, we have specific objectives for uptime and recovery Yes,...
Source: securityboulevard.com - Author: Richi Jennings It depends what you mean by “hack” (and by “Russia”).Trains...
Source: securityboulevard.com - Author: Kelsey Gast Industries worldwide have integrated artificial intelligence (AI) into their systems...
Source: securityboulevard.com - Author: Key points from our research: Around early-mid August, we noticed an increase...
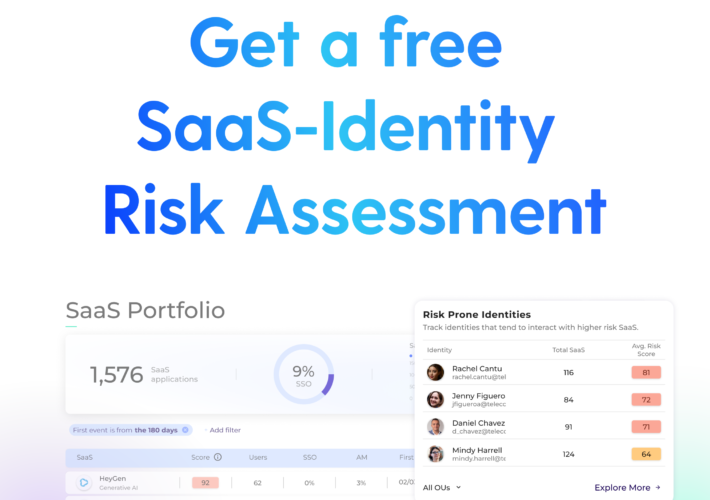
Source: securityboulevard.com - Author: Grip Security Blog Introduction In today’s digital age, where information flows seamlessly...
Source: securityboulevard.com - Author: Marc Handelman Yes, we have specific objectives for uptime and recovery Yes,...
Source: securityboulevard.com - Author: Jeffrey Burt About 80% of the cybersecurity incidents tracked by ReliaQuest during...
Source: securityboulevard.com - Author: Mimi Pham At TrustCloud, we’re on a mission to democratize compliance, so...
Source: securityboulevard.com - Author: Marc Handelman Yes, we have specific objectives for uptime and recovery Yes,...
Source: securityboulevard.com - Author: Esther Shein Generative AI is the technology of the moment, and is...
Source: securityboulevard.com - Author: Marc Handelman Yes, we have specific objectives for uptime and recovery Yes,...
Source: securityboulevard.com - Author: Jeffrey Burt Tor, the routing service that stresses anonymity and for almost...
Source: securityboulevard.com - Author: Rajan Sodhi As cloud computing continues to evolve, an intriguing new trend...
Source: securityboulevard.com - Author: Marc Handelman Yes, we have specific objectives for uptime and recovery Yes,...
Source: securityboulevard.com - Author: Lohrmann on Cybersecurity NIST has released a draft version 2.0 of the...
Source: securityboulevard.com - Author: Marc Handelman Yes, we have specific objectives for uptime and recovery Yes,...
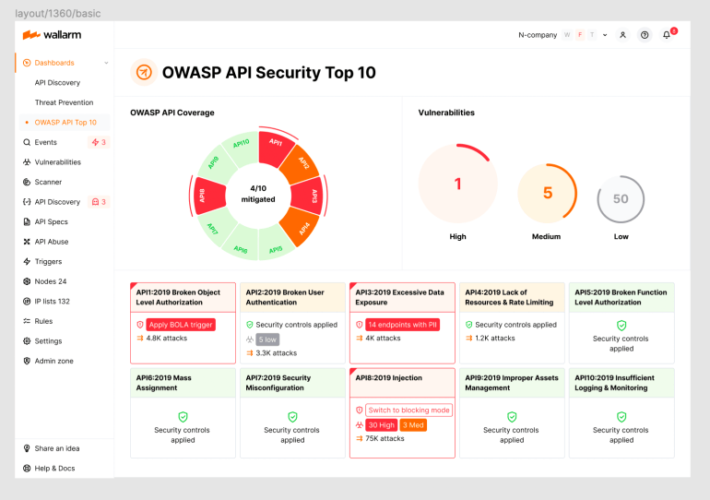
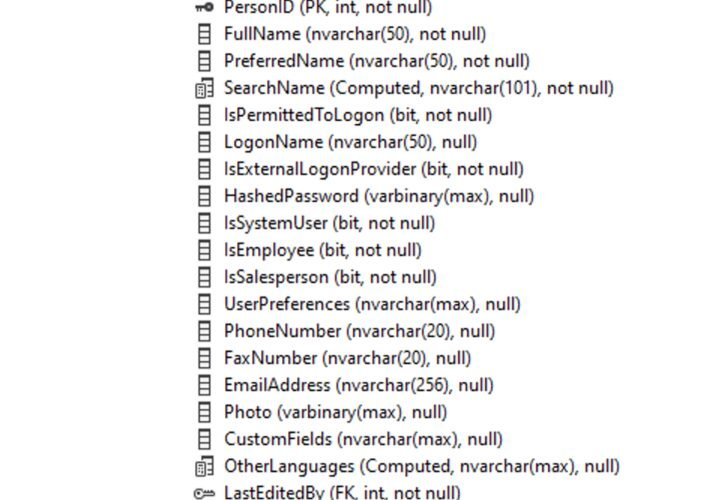
Source: securityboulevard.com - Author: wlrmblog Welcome to the 6th post in our weekly series on the...
Source: securityboulevard.com - Author: Keon Ramzani In the vast realm of cyber threats, where hackers and...
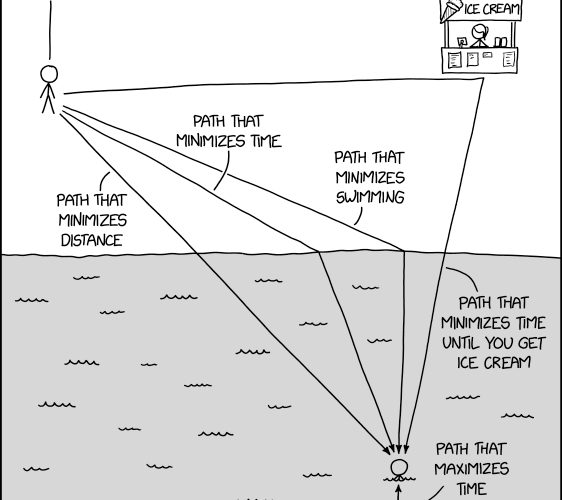
Source: securityboulevard.com - Author: Dylan Broxson Why Limit User Queries? We often run into customers wondering...
Source: securityboulevard.com - Author: Marc Handelman Yes, we have specific objectives for uptime and recovery Yes,...
Source: securityboulevard.com - Author: BrianKrebs Security consulting giant Kroll disclosed today that a SIM-swapping attack against...
Source: securityboulevard.com - Author: Marc Handelman Yes, we have specific objectives for uptime and recovery Yes,...
Source: securityboulevard.com - Author: Beverly Nevalga, Sr. Content Marketing Manager @ AppOmni In his presentation, Brendan...