Source: securityboulevard.com - Author: Brent Hansen In an era where technology is the cornerstone of the...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Audit Management Software: Why You Need It and How to Put it to Work – Source: securityboulevard.com
Source: securityboulevard.com - Author: Matt Kelly Managing audits is becoming more important, but it’s also more...
Source: securityboulevard.com - Author: BrianKrebs Domain names ending in “.US” — the top-level domain for the...
Source: securityboulevard.com - Author: Axiad September 1 is International Women in Cyber Day, a special day...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
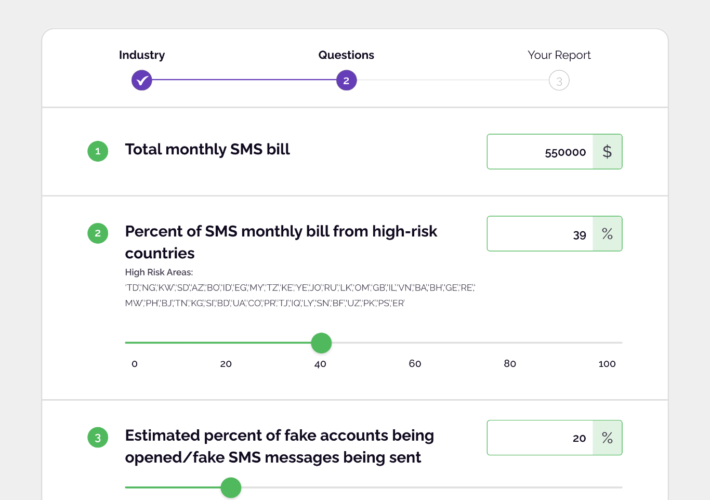
Source: securityboulevard.com - Author: Christina Luttrell As the COVID-19 pandemic raged, Adam Arena was getting rich....
Source: securityboulevard.com - Author: Lisa Vaas, Senior Content Marketing Manager, Contrast Security Friday, September 1, 2023...
Source: securityboulevard.com - Author: Dwayne McDaniel One theory about the Gateway Arch is that it is...
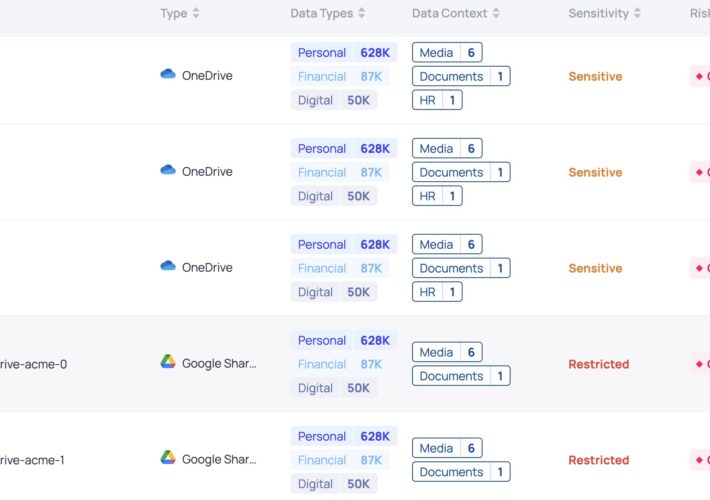
Source: securityboulevard.com - Author: Dave Stuart New cloud file share integrations mark a pivotal moment for...
Source: securityboulevard.com - Author: Jenn Jeffers While the primary goal of gig economy platforms is to...
Source: securityboulevard.com - Author: AJ Starita You don’t need us to tell you that open source...
Source: securityboulevard.com - Author: Jeffrey Burt A newly discovered cyber-espionage threat group for at least three...
Source: securityboulevard.com - Author: bacohido San Francisco, Calif., Aug. 30, 2023 — Every year over 340m...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Synopsys Editorial Team Security Boulevard The Home of the Security Bloggers Network...
Source: securityboulevard.com - Author: SafeBreach Financial services institutions (FSIs) have become an increasingly common target for...
Source: securityboulevard.com - Author: Richi Jennings After sneaking into Google and Samsung app stores, “GREF” APT...
Source: securityboulevard.com - Author: James Hauswirth August 31, 2023 In 2013, I began training in the...
Source: securityboulevard.com - Author: Rajan Sodhi Leading DCIM software provider leverages RF Code CenterScape software to...
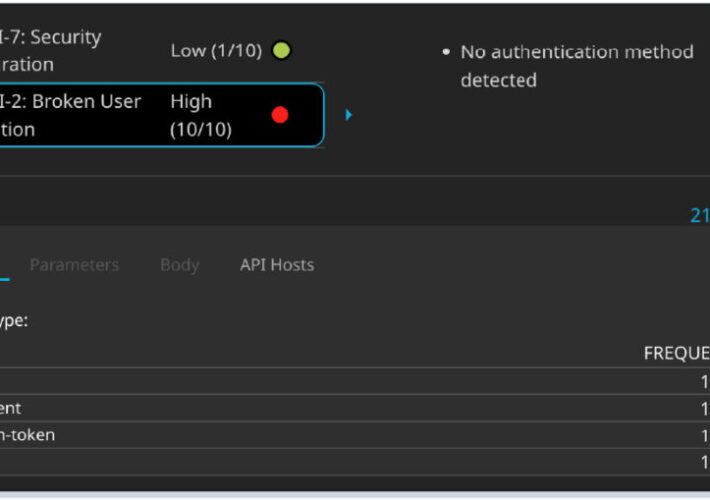
Source: securityboulevard.com - Author: Salt Technical Engineering The neon lights of Black Hat and DEF CON,...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Richi Jennings Operation Duck Hunt shoots to kill big botnet.Qakbot is dead....
Source: securityboulevard.com - Author: Jeffrey Burt The leak 11 months ago of the builder for the...
Source: securityboulevard.com - Author: Chris Pierson Doxxing poses a severe threat to its victims, leading to...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, August 30, 2023 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: FireMon Network security has become a top priority for enterprises to safeguard...
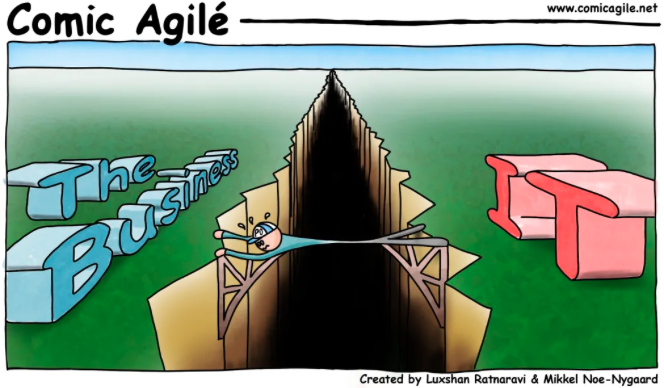
Source: securityboulevard.com - Author: Adam Lopez By Adam Lopez, Director of Solutions Engineering Strengthening Cybersecurity Defenses...
Source: securityboulevard.com - Author: Katie Fritchen This article was originally published in Hackernoon on 8.30.23 by...
Source: securityboulevard.com - Author: Noam Dotan Cloud environments and the applications running on them present an...