Source: securityboulevard.com - Author: rezilion Vulnerability management is difficult and not getting any easier. CISOs and...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Jeffrey Burt The threat group that claims to have been involved in...
Source: securityboulevard.com - Author: Michael Toback The Dawn of IoT: A Revolution in the Digital World...
Source: securityboulevard.com - Author: Avast Blog It’s not fun to think about: But if you should...
Source: securityboulevard.com - Author: Nak Koh Financial cards have been a cornerstone of our monetary transactions...
Source: securityboulevard.com - Author: Votiro Team By David NeumanSenior Analyst, TAG Cyber [email protected] Introduction Information is the...
Source: securityboulevard.com - Author: ISHIR | Software Development India As the relentless march of automation reshapes...
Source: securityboulevard.com - Author: Arani Adhikari In today’s digital landscape, cybersecurity incidents have become alarmingly common,...
Source: securityboulevard.com - Author: Fred Kost The ForgeRock Identity Platform has been awarded for excellence by...
Source: securityboulevard.com - Author: CyB3rBEA$T In today’s interconnected digital world, cyberattacks have become an ever-present threat...
Source: securityboulevard.com - Author: Marc Handelman Very Important - Follow available standards and guidelines (NIST, CIS,...
Source: securityboulevard.com - Author: Anthony Cusimano The possibility of their business falling victim to a cyberattack...
Source: securityboulevard.com - Author: Marc Handelman Very Important - Follow available standards and guidelines (NIST, CIS,...
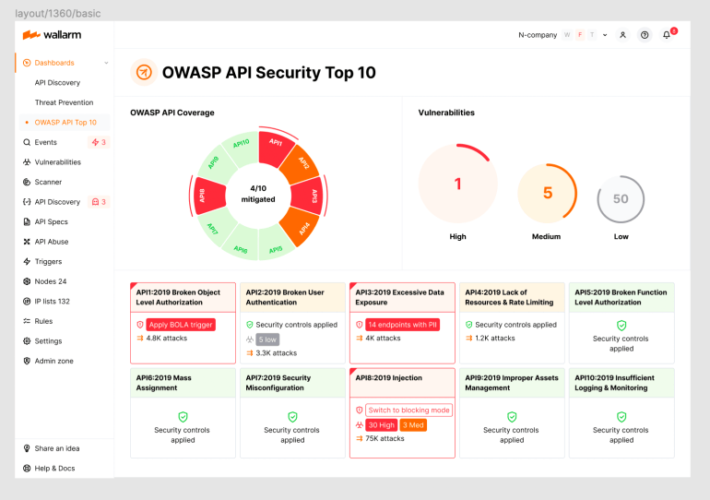
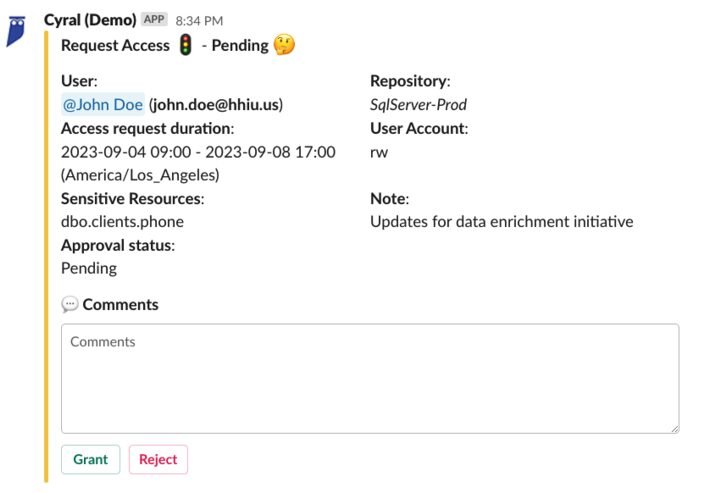
Source: securityboulevard.com - Author: wlrmblog Welcome to the 9th post in our weekly series on the...
Source: securityboulevard.com - Author: Bruce Schneier Claude (Anthropic’s LLM) was given this prompt: Please summarize the...
Source: securityboulevard.com - Author: Jeffrey Burt A data breach late last month of software development platform...
Source: securityboulevard.com - Author: Marc Handelman Very Important - Follow available standards and guidelines (NIST, CIS,...
Source: securityboulevard.com - Author: David Lindner, Director, Application Security Insight #1 Software Bills of Materials (SBOMs)...
Source: securityboulevard.com - Author: Marc Handelman Very Important - Follow available standards and guidelines (NIST, CIS,...
Source: securityboulevard.com - Author: Votiro Team Remote code execution (RCE) attacks within Word documents have long...
Source: securityboulevard.com - Author: Marc Handelman Very Important - Follow available standards and guidelines (NIST, CIS,...
Source: securityboulevard.com - Author: Ashish Nainwal In a 5G world, cybersecurity is needed more than ever...
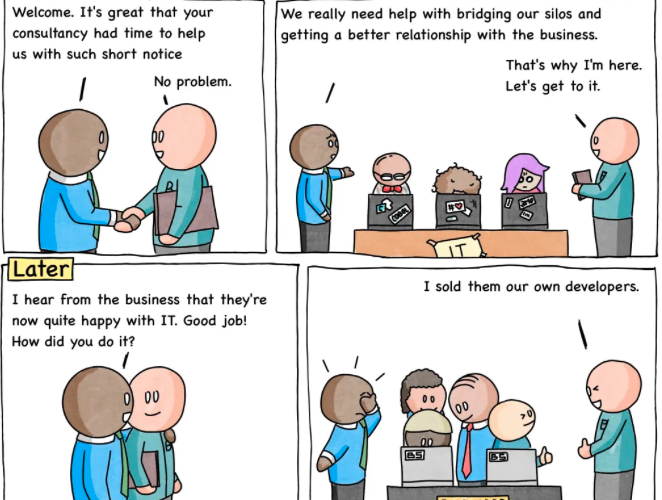
Source: securityboulevard.com - Author: Nathan Eddy Cybersecurity is often out of sync with business goals, according...
Source: securityboulevard.com - Author: Marc Handelman Very Important - Follow available standards and guidelines (NIST, CIS,...
Shifting Perspectives and Regulations Relating to Consent Management – Source: securityboulevard.com
Source: securityboulevard.com - Author: ForgeRock Guest Contributor Businesses have a certain responsibility to disclose how consumer...
Source: securityboulevard.com - Author: Bill Niester Fall is here in much of America, and amidst the...
Source: securityboulevard.com - Author: Marc Handelman Very Important - Follow available standards and guidelines (NIST, CIS,...
Source: securityboulevard.com - Author: Anthony Day Meet Rosie & Her Architecture Cloud costs are a common...
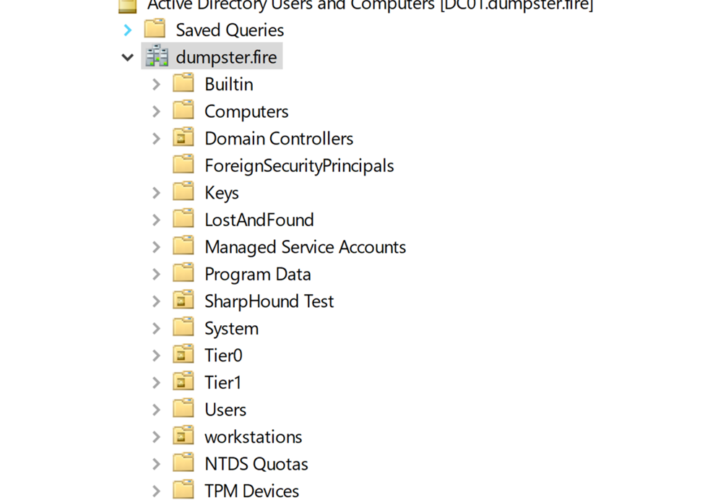
Source: securityboulevard.com - Author: Jonas Bülow Knudsen What is Tier Zero — Part 2 Round 2! This is Part...
Source: securityboulevard.com - Author: Marc Handelman Very Important - Follow available standards and guidelines (NIST, CIS,...