Source: securityboulevard.com - Author: Dan Page Here at Ignyte, we talk a lot about the major...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Alison Mack Why Should Professionals Consider NHI for Security Needs? Is your...
Source: securityboulevard.com - Author: Alison Mack Is Your Investment in Advanced NHIs Justifiable? Investing in advanced...
Source: securityboulevard.com - Author: Alison Mack How Does Cloud Compliance Translate Into Team Satisfaction? Are you...
Source: securityboulevard.com - Author: Dev Kumar If you’re responsible for cybersecurity at your organization, there’s a...
Source: securityboulevard.com - Author: Roman Kadinsky, Cofounder, President & COO, HYPR As the transition period for...
Source: securityboulevard.com - Author: Marc Handelman Author/Presenter: Hazel Weakly (Nivenly Foundation; Director, Haskell Foundation; Infrastructure Witch...
Source: securityboulevard.com - Author: Richi Jennings Pretty girls plus investment fraud equals forfeiture recovery (eventually).U.S. federal agencies have...
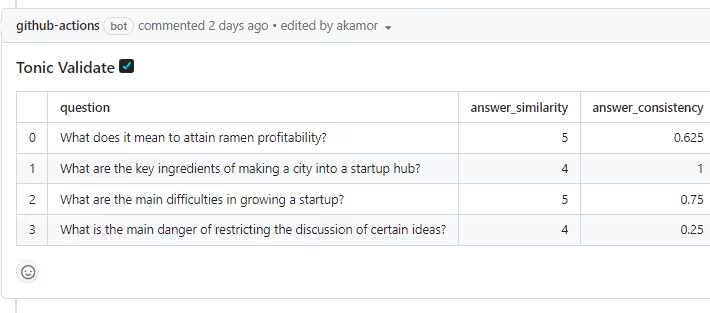
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog Tonic Validate is...
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog Tonic.ai offers a...
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog Tonic Validate is...
Source: securityboulevard.com - Author: Bart A month or so ago a friend of mine received the...
Source: securityboulevard.com - Author: Yohann Sillam Remote attackers can trigger an avalanche of internal ESI requests,...
Source: securityboulevard.com - Author: Chetan Saxena Imagine if every doctor had an invisible assistant, one that...
Source: securityboulevard.com - Author: Eric Olden Agentic User Flow: A New Identity Model in Action Human...
Source: securityboulevard.com - Author: Eric Olden AI agents have evolved from passive tools into proactive actors—making...
Source: securityboulevard.com - Author: Impart Security Blog The recent disclosure of EchoLeak by Aim Labs marks...
Source: securityboulevard.com - Author: Eric Olden Artificial intelligence is no longer just about passive assistants or...
Source: securityboulevard.com - Author: Eric Olden AI agents have crossed a threshold. They’re no longer just...
Source: securityboulevard.com - Author: Alison Mack Can Optimism Shape the Future of Secrets Management? Secrets management...
Source: securityboulevard.com - Author: Marc Handelman Author/Presenter: Angela Fischer (Jupiter Broadcasting Co-Owner) Our sincere appreciation to...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Rajan Sodhi Imagine you’re at the helm of a ship navigating through...
Source: securityboulevard.com - Author: Krupa Patil Today’s financial systems are highly digital and deeply interconnected. That’s...
Source: securityboulevard.com - Author: cybernewswire Miami, June 18, 2025, CyberNewswire — Halo Security today announced that...
Source: securityboulevard.com - Author: Dev Kumar Managing identities and access has become one of the most...
Source: securityboulevard.com - Author: Alexa Sander In a recent webinar, two expert K-12 technology leaders—Glen Drager,...
Source: securityboulevard.com - Author: Alison Mack Uncover the Hidden Power of Secrets Rotation Have you ever...
Source: securityboulevard.com - Author: Enzoic Preventing Credential Stuffing Introduction In 2023, personal genomics company 23andMe suffered...
Source: securityboulevard.com - Author: FireMon Online threats are everywhere, and no organization is safe from them....