Source: securityboulevard.com - Author: Itzik Alvas. Co-founder & CEO, Entro While you might know your secrets...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Netography Team Launching Tomorrow: CyberPsych Podcast with Dr. Stacy Thayer I have...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Zia Hotaki Phishing Threats Are Increasing in Scale and Sophistication Phishing remains...
Source: securityboulevard.com - Author: Srini Addepalli Shared Processes for Packet-level Security Technologies Networking and security technologies...
Source: securityboulevard.com - Author: Pushpendra Mishra Seceon, the pioneer of the first cybersecurity platform that augments and automates...
Source: securityboulevard.com - Author: Michael Toback Introduction Endpoint security is a critical component of a comprehensive...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Jenn Sherman It’s been a few weeks now since Carahsoft’s FedRAMP Headliner...
Source: securityboulevard.com - Author: Jeffrey Burt Ransomware groups are shrinking the time between attacks on the...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Daniella Balaban Email-based attacks spiked almost 500% in the first half of...
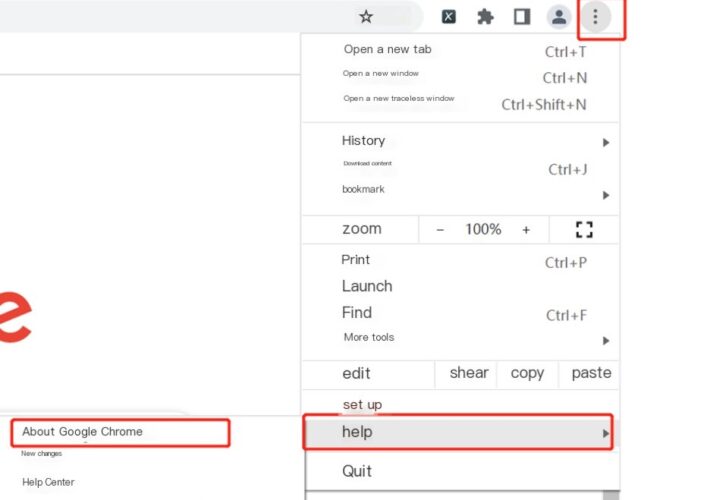
Source: securityboulevard.com - Author: NSFOCUS Overview Recently, NSFOCUS CERT found that Google officially fixed a zero-day...
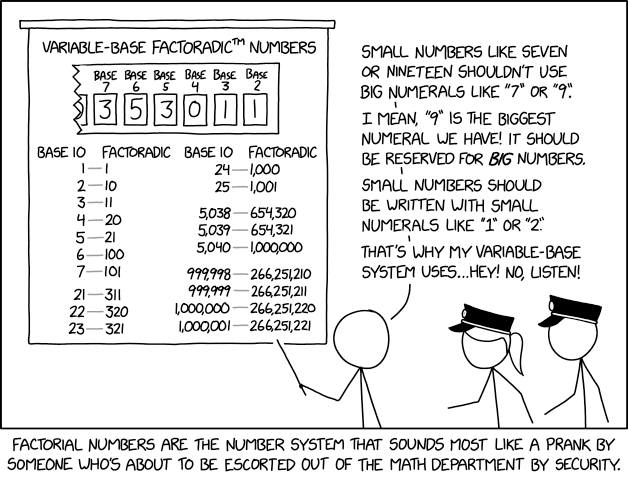
Source: securityboulevard.com - Author: hrbrmstr If you’ve got on this blog (directly, or via syndication) you’d...
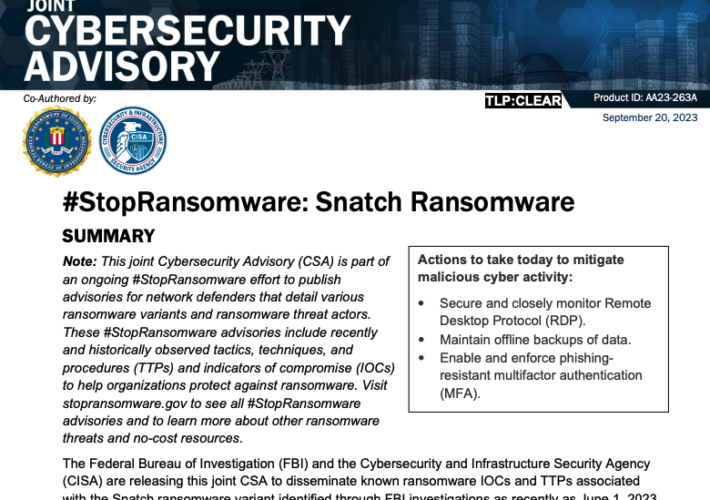
Source: securityboulevard.com - Author: BrianKrebs Earlier this week, KrebsOnSecurity revealed that the darknet website for the...
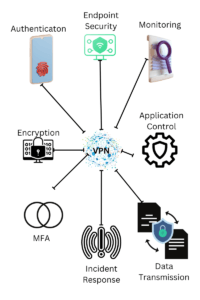
Source: securityboulevard.com - Author: Michael Toback Introduction In today’s interconnected world, the need for secure remote...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
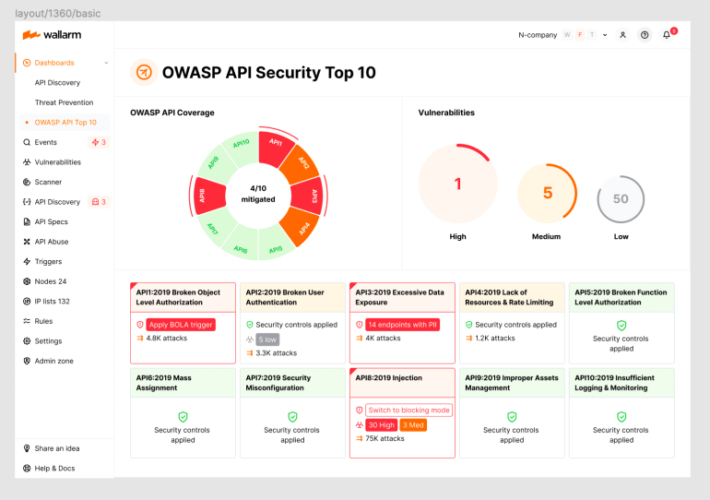
Source: securityboulevard.com - Author: wlrmblog Welcome to the 11th post in our weekly series on the...
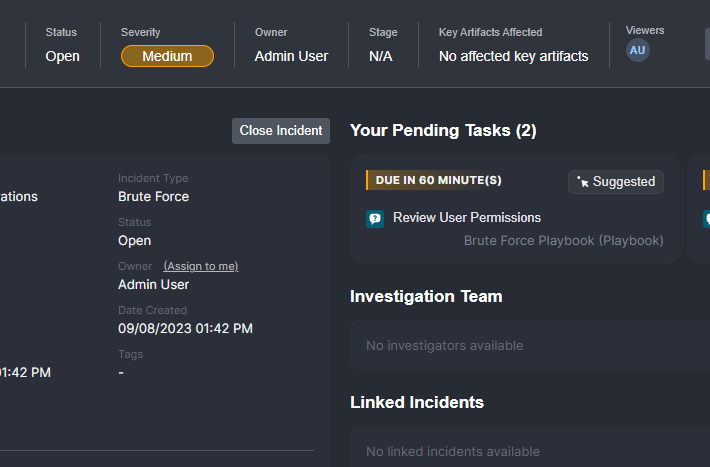
What Enterprise Security Teams Expect from Case Management Solutions – Source: securityboulevard.com
Source: securityboulevard.com - Author: Pierre Noujeim A less-talked about challenge in cybersecurity is managing multiple alert...
Source: securityboulevard.com - Author: bacohido By Byron V. Acohido Once again, politicians are playing political football,...
Source: securityboulevard.com - Author: Julie Criscenti Heck We’ve always known the value of partnering with Cisco...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Jeffrey Burt The federal government for the past few years has focused...
Source: securityboulevard.com - Author: Avast Blog Friday, September 29, 2023 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Sarah Hunter-Lascoskie In a non-digital world, checking someone’s age has its challenges....
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
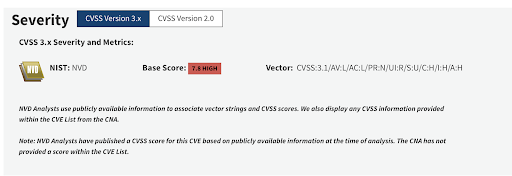
Source: securityboulevard.com - Author: Yael Citro libwebp exploit timeline CVE-2023-41064; CVE-2023-4863; CVE-2023-5129 On September 7th 2023,...
Source: securityboulevard.com - Author: Wes Wright I just joined Ordr as Chief Healthcare Officer and, as...
Source: securityboulevard.com - Author: Kasada Customer background Crocs is one of the world’s top non-athletic footwear...